MULTI-FACTOR AUTHENTICATION
Authentication That’s Smart, Not Clunky
Block threats, not users. Make sure people are who they say they are without getting in their way.
We work with the world’s top brands
THE CHALLENGE
MFA Overload Doesn’t
Solve Password Problems
Attackers Still Love Passwords
Weak, reused, phished. Passwords still lead to fraud and data breach. MFA helps block ATO, secure agentic AI adoption and commerce, and keep humans in the loop.
Friction Hurts Productivity
Static, always-on MFA prompts pop up at every login. This frustrates users, boosts costs, and overwhelms IT teams with workarounds.
Hybrid Isn’t Going Away
Enterprises run a mix of SaaS, on‑prem, and custom apps. You need security that spans VPNs, legacy systems, and modern cloud, and you shouldn’t have to re‑platform.
THE SOLUTION
Adaptive MFA That Knows When to Step In
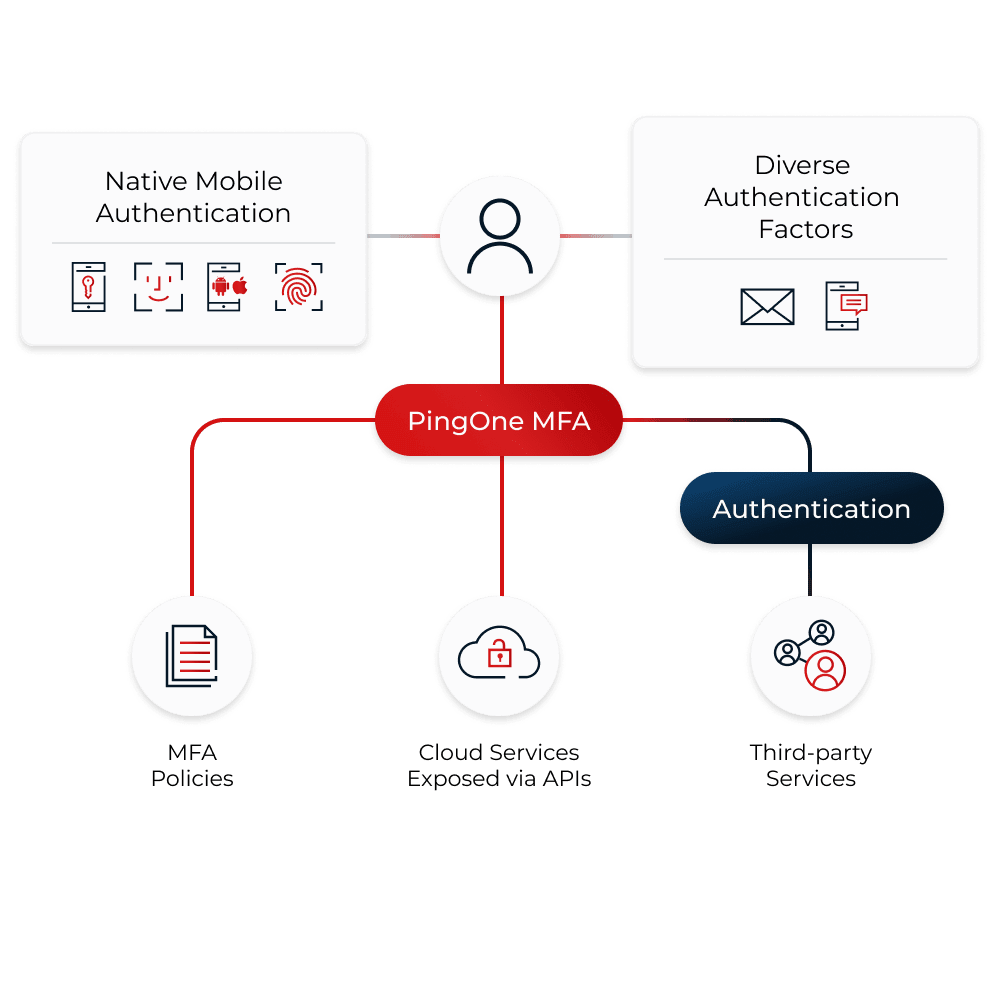
Go beyond static MFA. With Ping, you can confirm identities with context-aware policies and phishing-resistant methods. You can use risk signals like location, IP, device, or behavior to step up only when necessary.
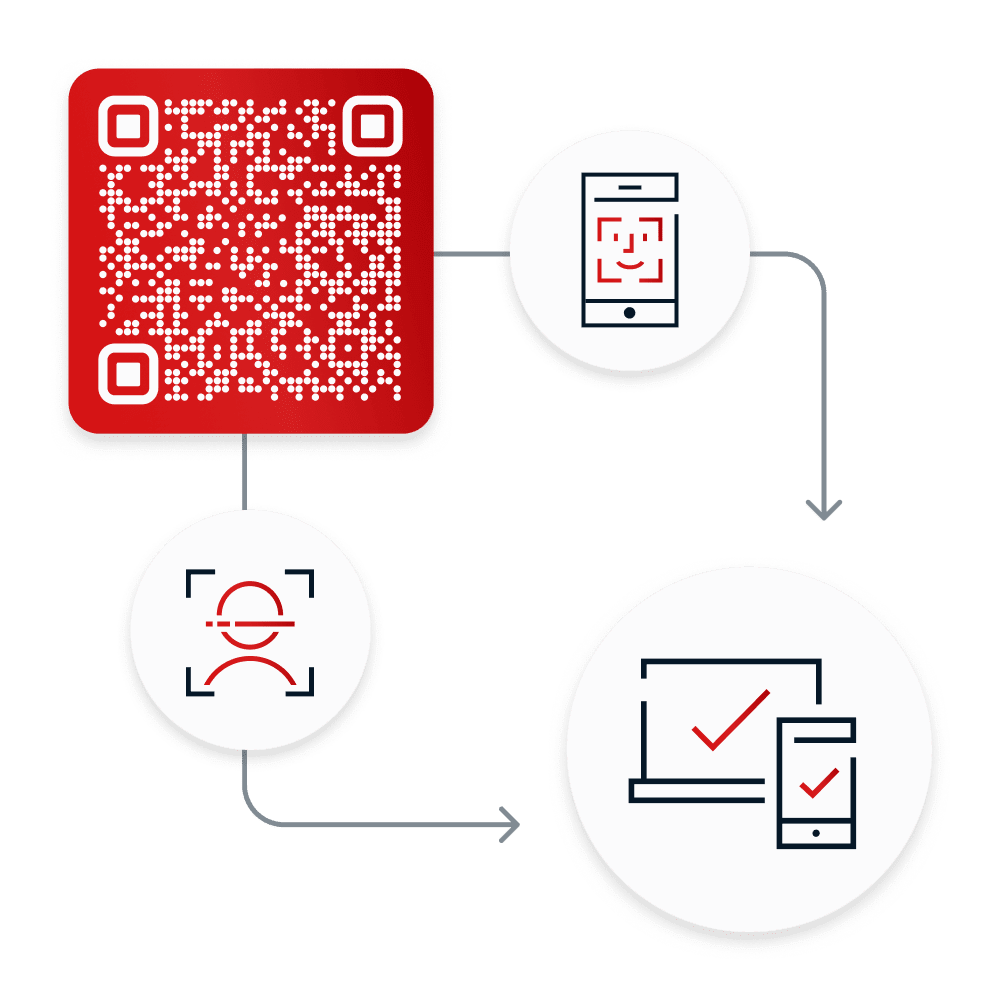
You can even go passwordless using push notifications, QR codes, platform biometrics, and FIDO authenticators. And as AI users take action, you can verify the humans behind those decisions. Most importantly, you can enforce security that stays out of the way.
Why You’ll Love Our MFA
Simple, secure authentication that keeps users happy and IT efficient.
Stop Breaches
Shut down credential-based attacks with strong, risk-based authentication.
Go Passwordless
Make login easier and more secure with push notifications, biometrics, and more.
Make Users Happy
Reduce prompt fatigue and friction with adaptive policies that step up only when needed.
Cut IT Costs
Enable self‑service and streamline admin to shrink password reset ticket load.
Secure Agentic AI
When AI agents act on someone’s behalf, verify it with human-in-the-loop oversight.
What Makes Our MFA Work
Security, scale, and interoperability that’s built to work with your tech stack.
What Makes Our MFA Work
Security, scale, and interoperability that’s built to fit right into your tech stack.
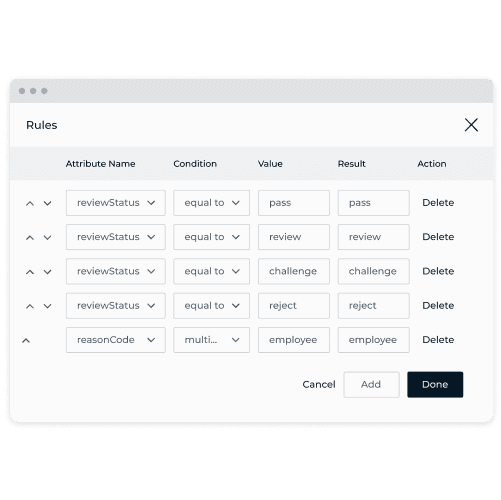
Continuously evaluate context, and trigger step‑up authentication only when something looks off.
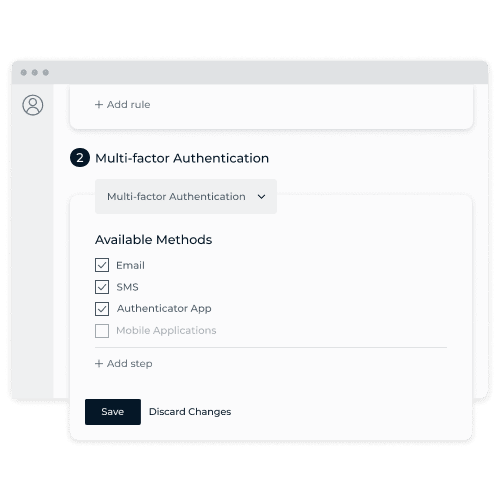
Push notifications, OTPs, biometrics (face, fingerprint), QR, FIDO/WebAuthn. You name it, we support it.
Use SDKs and APIs to plug MFA into your mobile and web apps, and authenticate everything from human users to agentic commerce.
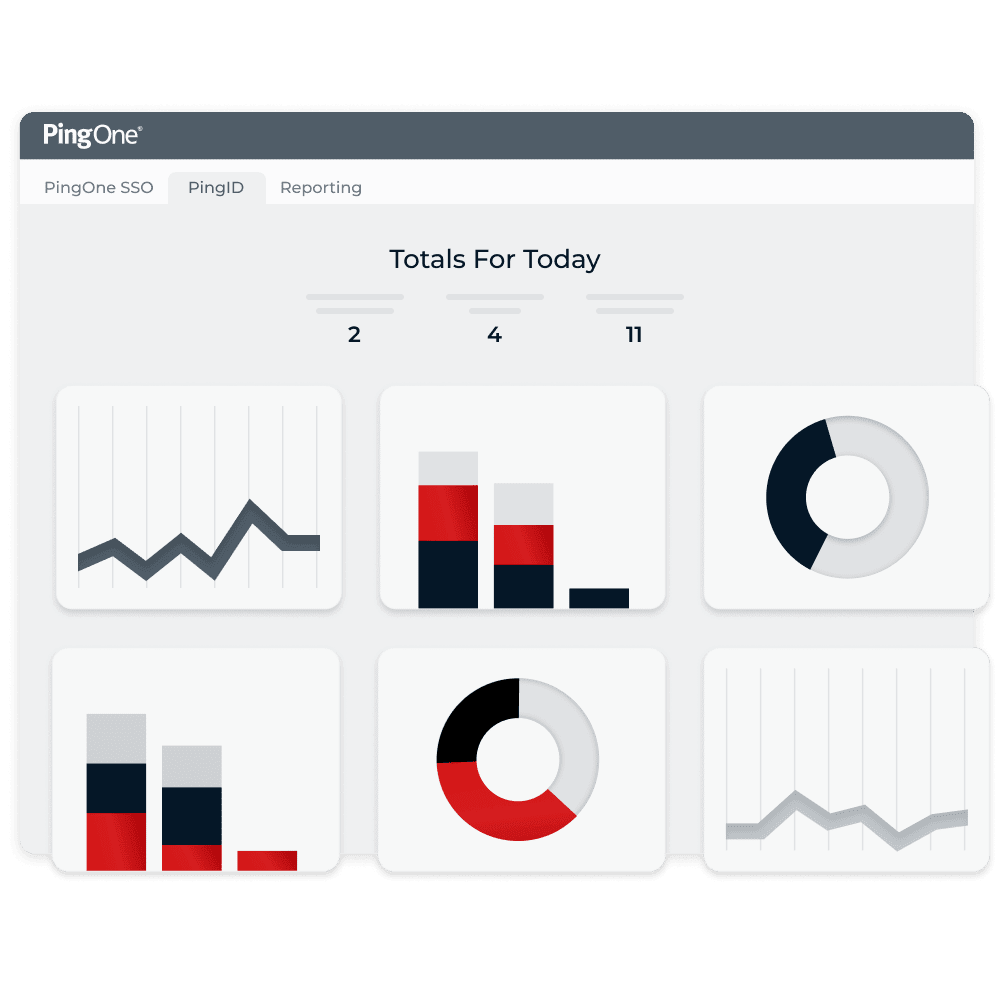
In a single view, admins can track adoption, monitor usage, and review SMS costs to fine-tune the user experience.
Secure everything from SaaS and on-prem apps to VPNs and multi-cloud environments, all with one policy engine.
Get started and go live fast with simple APIs and out-of-the-box connectors for Microsoft 365, VPNs, and much more.
DIVE INTO THE DETAILS
From WebAuthn to biometrics to risk signals, see the Ping controls that shut down breaches and keep experiences smooth.
Works with
What You Have
Improving your security shouldn’t require a rebuild. Ping integrates fast with your current stack, so you can implement strong authentication in a matter of minutes. Plus, self-service features and simple admin make your MFA rollout effortless.
“When we implemented PingOne Protect, we called it 'Forever Session' ...95% of interactions on our website don't require a password.”
88%
reduction in fraud, putting MILLIONS back into the business
$570K
recovered in annual productivity time
Why Ping Identity?
Securing your most sensitive access points shouldn’t mean being locked into a single stack or stitching together a dozen tools. Our platform combines a powerful IdP foundation with a suite of services that are interoperable with any provider. No matter where you start, you can unlock value with flexibility, speed, and scale across every stage of your identity journey.
Here’s what sets us apart:
Universal identity services, built to work anywhere
Trusted globally, proven at enterprise scale
Easy to deploy, effortless to evolve
Tough on Breaches.
Easy on Users.
Whether your trusted users are human or not, they deserve secure, seamless access. Let’s make MFA work smarter for everyone.
Helpful Resources
Helpful Resources
Frequently Asked Questions
Choosing an MFA solution is a big decision. We’re here to help. We’ve got clear answers to common questions about our MFA and how it works.
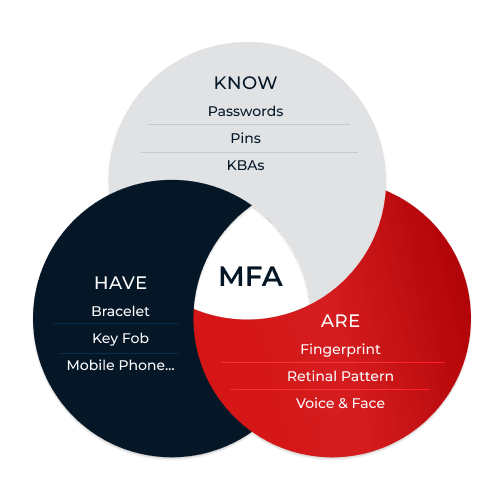
MFA is a login security method that requires two or more independent factors (like a password plus a mobile push notification or biometric check) to verify the identity of a user.
It continuously evaluates risk signals like device, IP, geolocation, and behavior, and it only prompts a user for extra authentication when needed.
Modern MFA is context‑aware and API‑first, which makes it a more intelligent and flexible form of authentication. Legacy MFA uses static, persistent prompts, or has limited authentication methods that make it less smooth for admins to integrate and for users to operate.
Not always. Passwordless is the concept of removing passwords at login to access apps and systems. But you can still require multiple strong authentication factors (e.g., biometrics + device) for MFA, especially if users are accessing sensitive assets and resources.
Standards‑based FIDO/WebAuthn authenticators with device‑bound keys are proven to be resistant against phishing.
Start Today
Contact Sales
See how Ping can help you deliver secure employee, partner, and customer experiences in a rapidly evolving digital world.