SINGLE SIGN-ON (SSO)
One Login.
All Access.
Give your users secure, one-click access to everything. No more password overload.
We work with the world’s top brands
THE CHALLENGE
Too Many Apps & Passwords.
Too Much Risk.
Credential Pile-Up = Security Breakdown
Every account login is a prime target for attackers. The more credentials you manage, the bigger the breach window.
User Frustration Kills Productivity
Frequent sign-ons, password resets, and account recoveries slow your business down and lead to risky workarounds.
Hybrid Complexity Is Real
Modern SaaS, on‑prem apps, and legacy systems rarely speak the same language. Connecting them with custom solutions is costly and brittle.
THE SOLUTION
SSO That Just Works, Everywhere
Sign on once. Access everything. Let Ping be your identity and access control plane and broker secure, standards-based, one-click access to everything your users need.
Built for modern identity, Ping plugs into your stack and scales with you. Whether your apps are in the cloud, bound to legacy systems, or even custom to your org, we unify authentication behind the scenes to keep the experience fast and friction-free. Less risk. More control.
Why You’ll Love Our SSO
Simple, secure access for users. Centralized control for IT.
Stronger Security
Fewer passwords means fewer breaches. Centralized authentication using modern standards means a smaller attack surface.
Better UX = Happier Users
One login. Fewer prompts. Fast self-service password resets and account recovery keep people moving.
Lower IT Costs
Fewer user helpdesk tickets. Fewer app-by-app configuration. One authentication policy engine to manage it all.
What Makes Our SSO Work
Security, scale, and interoperability that’s built to work with your tech stack.
What Makes Our SSO Work
Security, scale, and interoperability that’s built to work with your tech stack.
Establish trust between users, tenants, domains, and apps with proven standards-based identity federation. Quickly and easily.
Let users manage their own registration, profile updates, password resets, and account recovery. No helpdesk delays.
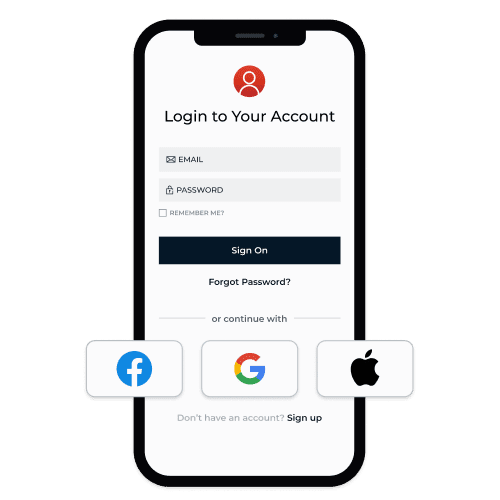
Let customers sign on with their familiar social profiles, and link them to enterprise accounts for a single, unified profile.
DIVE INTO THE DETAILS
From federation to OIDC/SAML brokering to adaptive policies, explore the Ping capabilities that make seamless sign-on possible across every app, user, and environment:
Works with
What You Have
Whether you're connecting popular SaaS apps or complex internal systems, Ping provides turnkey integrations and powerful tools to deliver SSO across your entire landscape. We support modern cloud apps like Microsoft 365, legacy systems, APIs, and everything in between, all with one consistent, secure identity foundation.
Sample Integrations
“PingFederate is legendary for its ability to work with a wide variety of existing environments.”
~2 Days
to deploy with complete client integrations
6,200
SSO logins per month
Why Ping?
Securing your most sensitive access points shouldn’t mean being locked into a single stack or stitching together a dozen tools. Our platform combines a powerful IdP foundation with a suite of services that are interoperable with any provider. No matter where you start, you can unlock value with flexibility, speed, and scale across every stage of your identity journey.
Here’s what sets us apart:
Universal identity services, built to work anywhere
Trusted globally, proven at enterprise scale
Easy to deploy, effortless to evolve
Ready to Simplify Access Across Your Enterprise?
See how SSO boosts security and gives your customers, employees, and partners an experience they’ll love.
Helpful Resources
Helpful Resources
Frequently Asked Questions
New to SSO? Modernizing an older setup? We’ve got clear answers to common questions about standards, deployment, and best practices.
The specifics depend on the SSO protocol that’s used, but generally speaking, an SSO token is a short-lived, digitally signed package issued by your identity provider after you sign on. Apps use this token to verify who you are and what you’re allowed to do so you don’t have to re-enter your password for each app.
Yes. SSO offers a secure way for users to access multiple applications without having to re-enter their credentials every time. This reduces the number of opportunities for a bad actor to take advantage of a compromised password since each user only has to sign on once. SSO systems also exchange secure SSO tokens instead of sending passwords back and forth, which keeps sensitive information even more secure.
Ultimately, the implementation method depends on your environment, but the process follows a common pattern. First, you set up a central identity provider (like Ping), connect it to your directory, and configure trust with your applications using open standards. Then, you can manage authentication policies like sign-on, account linking, MFA, and adaptive access from one place. We can help you find the best approach for your systems and guide you through setup.
You may hear terms like single sign-on (SSO) and federated identity management (FIM) mentioned together, but they’re not the same thing. SSO enables users to access multiple applications and resources within a single organization or domain after signing on once. FIM extends that concept across multiple domains or organizations, allowing different identity systems to trust each other—so users can sign on once and access apps managed by partners or external providers. Another unique term is cloud SSO, which centralizes access to cloud-based applications and services, enabling users to authenticate once with a trusted identity provider for all their SaaS and cloud resources.