To ensure the highest level of convenience, organizations typically focus on three MFA options for supplementing a user’s password:
- One-time passcodes via SMS. The ubiquitousness of mobile phones means that most customers will be able to receive single-use passcodes via text messaging.
- Email verifications. Also nearly everywhere, email accounts are convenient delivery mechanisms for wide swaths of customers.
- Push notifications from your custom mobile app. This method allows you to turn customer devices with your app installed into trusted devices and use push notifications from your custom app for MFA.
Each option has their advantages and disadvantages. Your priority when implementing MFA, should be to give customers the most secure, convenient options for MFA.
SMS
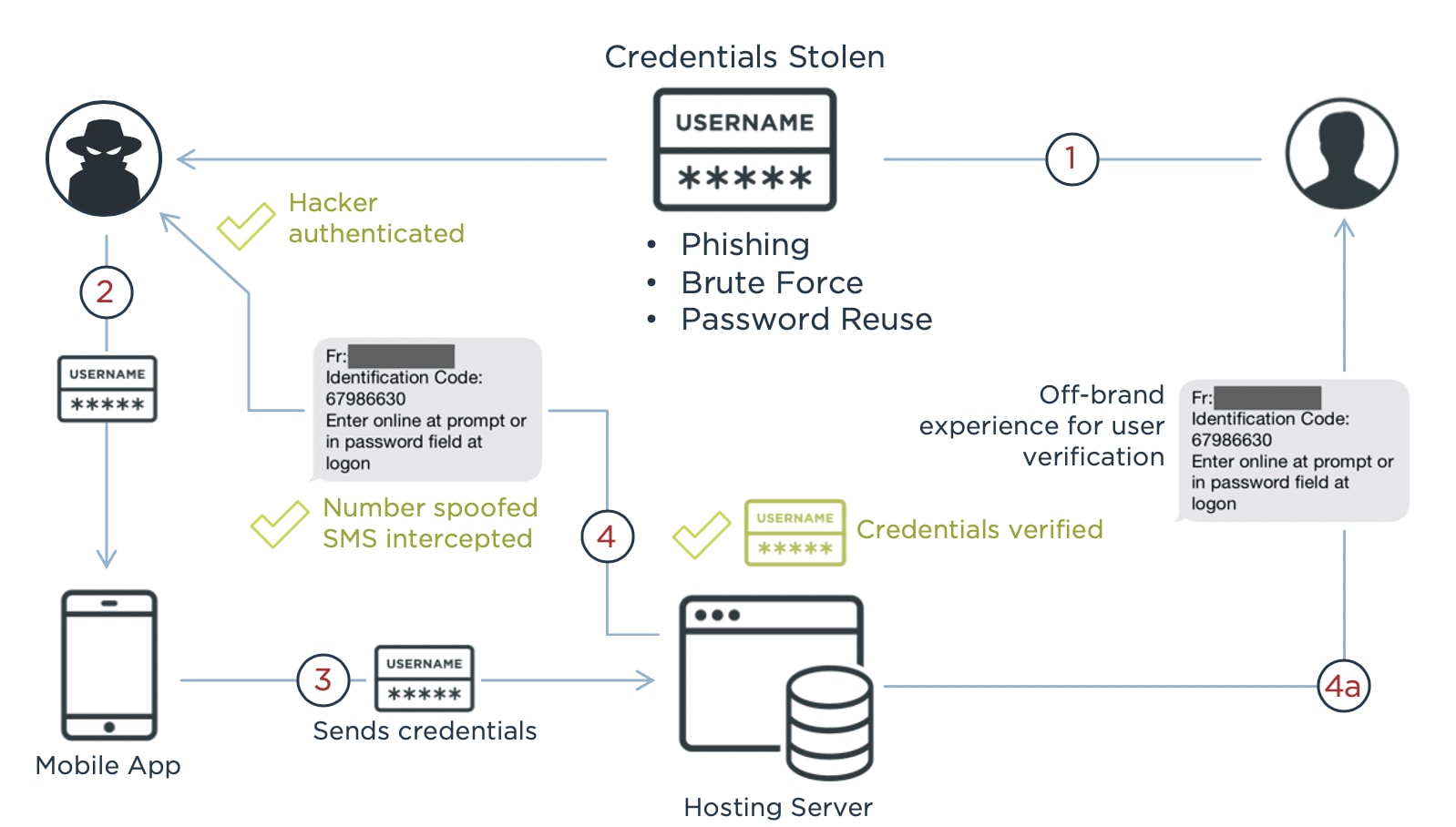
First, let’s talk SMS. Offering your customers an additional way to authenticate is clearly better than nothing, and presenting them with a second factor that allows them to verify their identity is good defense against bad actors and can drastically reduce fraud. But we’ve been writing in this space for several years about the risks of using SMS, and if someone is really motivated, they can bypass this security check.
For instance, SIM swapping, whereby someone uses social engineering to fraudulently convince a wireless carrier to assign the phone number to a new SIM card, or SIM cloning, which duplicates the SIM card so that it can be used in a different phone, are two ways that MFA can be compromised. Motivated scammers have shown how easily MFA can be compromised through vulnerable SMS messages.
Also, while SMS is a medium nearly all customers are used to, it has inconveniences as well as insecurities. Your customers have to wait for the text to arrive, which may be affected by telenetworks and other variables out of your control. And then it often involves memorizing, or using smartphone copy and paste (which isn’t always the easiest to use!) to paste in a code. Your customer may have to close their web browser, open the SMS app, copy the text, and then reopen the web browser—an approach to MFA that’s far from convenient.
Email
Like SMS, email is something most customers are familiar with, but it has some of the same inconveniences as SMS. Customers have to wait to receive an email, and they must open their email and then copy a code or click a link, which may force them to open a second browser tab. It’s not the end of the world, but it also isn’t the most convenient set of actions.
And that doesn’t address what’s arguably an even bigger problem: security. A recent Ping survey found a whopping 47% have let others use their password for an entertainment or e-commerce service, and nearly one quarter of that group is likely to reuse those passwords for a service that can unlock more personal information, such as email and banking.
Since so many customers share and reuse passwords, the odds are too high for comfort that a hacker who is attempting to log in to a site using a compromised or shared password will also be able to log into that customer’s email account, thereby bypassing the MFA capability.
Push Notifications to Trusted Devices
A third—and better—option is to create a “trusted device” by installing your mobile app on a customer’s phone. In this case, your app has access to unique device secrets that will only ever be tied to a single device, and these unique device identifiers are much more difficult to compromise than phone numbers or email addresses (which regularly change devices).
At its core, it’s much more secure, and it’s also more convenient. Your customers don’t have to open browser tabs or copy random numbers with a smartphone UI. Instead, a push notification is sent to their smartphone from an app they already have—your app, then they can face scan or fingerprint to verify their identity, and they’re in. That’s it.