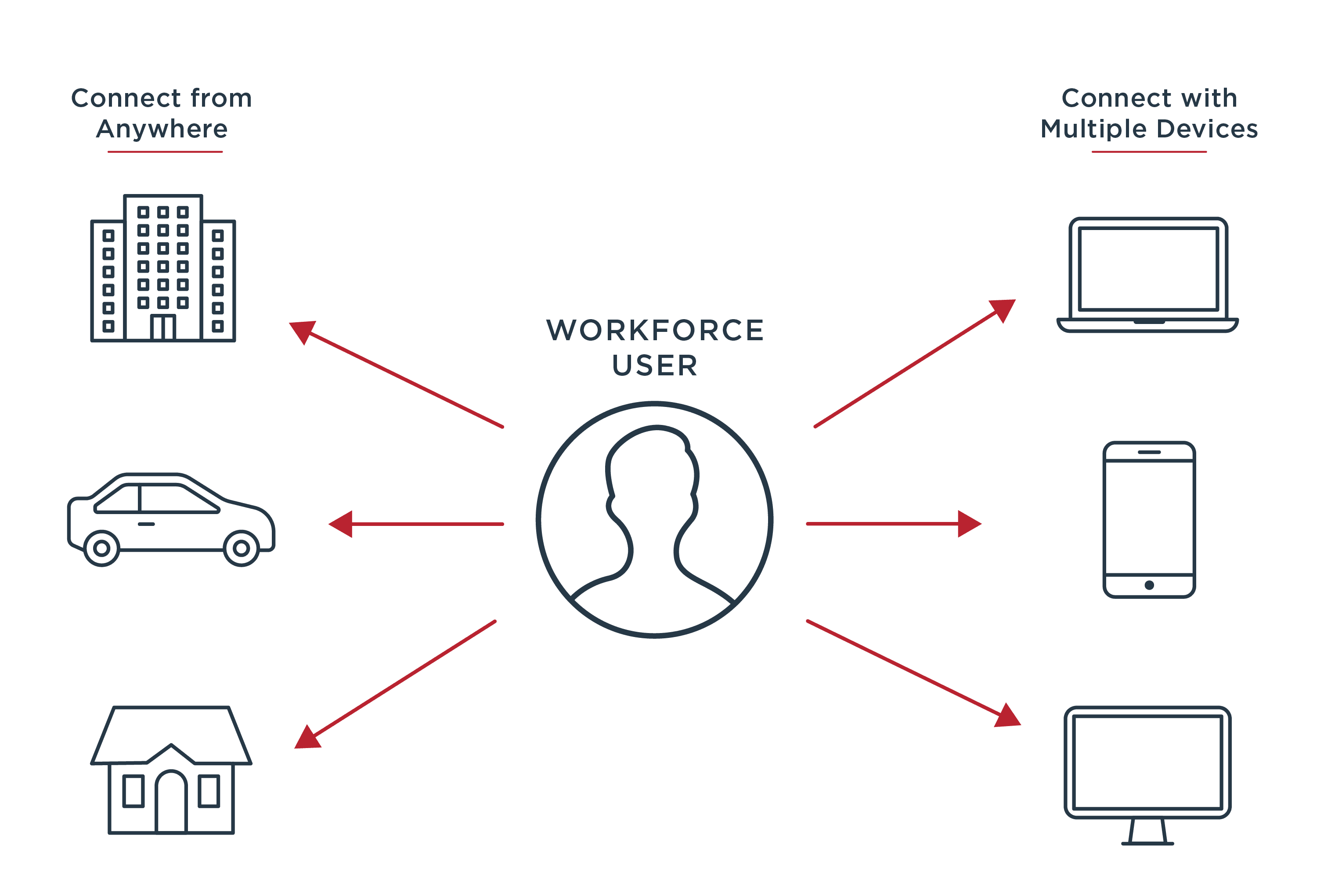
Ping’s Adaptive Access Security solution helps large enterprises secure access to every corporate resource. You’re able to support the productivity of an increasingly remote workforce, make smarter security decisions and advance digital transformation initiatives.
Enable Your Dynamic Workforce:
Reduce risk with centralized session and policy management and provide your workforce with secure access to every resource.
Make Smarter Decisions:
Extend existing security platforms to prevent new threats by using intelligence to dynamically and continuously evaluate user risk scores and by leveraging machine learning to detect and block threats to APIs.
Increase Agility and Adoption of New Technologies:
Modernize legacy web access management (WAM) to reduce costs, drive efficiency and rapidly adopt cloud, API and mobile technologies to meet business needs.
Solution Features
|
Capabilities and Benefits
Access Security for Every Resource
- Web and API access management
- Fine-grained user data access controls
- Attribute-by-attribute data access governance
- Allow, block, filter or obfuscate unauthorized data based on entitlements
- Automated API discovery
Reduce Risk with Consolidated Security
- Centralized policy and session management
- Externalized authorization with a graphical policy administration interface for business users
- Delegated account administration and data access
- Continuous self-learning of API traffic doesn’t require written policies
Dynamic Policies & Intelligence
- Dynamic authentication policy enforcement
- Dynamic authorization based on real-time risk scores, data source lookups and more
- Artificial intelligence for each API to determine anomalous traffic behavior
- Automatic API threat detection and blocking
- API deception and honeypot for instant hacking detection
Migrate Legacy WAM
- Integration with existing IAM infrastructures
- Gateway and agent deployment models
- Support for current WAM deployment models
- Enablement of a proxy-based architecture
- Automated policy migration from Oracle Access Manager and CA Siteminder
Cloud Your Way
Support cloud mandates with your choice of where to deploy enterprise IT.
On Premises: Deploy as traditional software in your data center for ultimate control and unmatched reliability
Your Cloud: Deploy to the cloud of your choice (AWS, Google, Azure) and with cloud automation and orchestration, including Docker images, which are DevOps ready
Hybrid IT: Combine on-premises and cloud deployment options to fit your enterprise’s unique needs
Integrations
Modernize your legacy IAM by integrating the Adaptive Access Security solution with leading security providers:
- Risk score providers for dynamic authorization
- API gateways through sideband or inline deployment options to monitor API traffic
-
Adaptive Access Security
Explore an intelligent approach to securing the borderless enterprise.
White Paper
-
2020 Gartner Magic Quadrant for Access Management
See why Gartner named Ping a leader in seamless and secure access management.
Analyst Report
-
Security Leader's Guide to Access Security
Secure your enterprise and enable digital transformation with modern MFA.
Guide
Start Today
See how Ping can help you deliver secure employee and customer experiences in a rapidly evolving digital world.
Request a free demo
Thank you! Keep an eye on your inbox. We’ll be in touch soon.