PingAccess
Tour the Product
In part one of this whiteboard, you'll learn how PingAccess can increase productivity by extending single sign on to all applications, even your most difficult use cases.
PingFederate provides a range of convenient approaches to enable single sign on.
But extending single sign on to all applications can be difficult because some don't natively support federation standards like SAML, OAuth, and open ID connect.
And others might be protected by agent-based legacy, web access management solutions.
When PingFederate, and PingAccess are deployed together, you can easily extend single sign on to all applications.
There are HTTP header injection, jot tokens, and even token mediation to applications protected by legacy web access management agents.
This enables the seamless addition of all applications to your federated architecture.
PingAccess also provides an out of the box integration to Microsoft Azure active directory, allowing Microsoft customers to enjoy single sign on and access security to all of their on premise applications.
PingAccess enables these connections without requiring application developers to refactor applications with heavy agents or integration kits.
If agents are required, PingAccess provides lightweight agents that are easy to deploy and manage, thanks for watching.
View parts two, three, and four in this series to learn how combining PingFederate, and PingAccess can benefit your organisation.
For a more in depth understanding of the benefits of the combined solution, download the white paper, expanding SSO to comprehensive access management.
Meet PingAccess
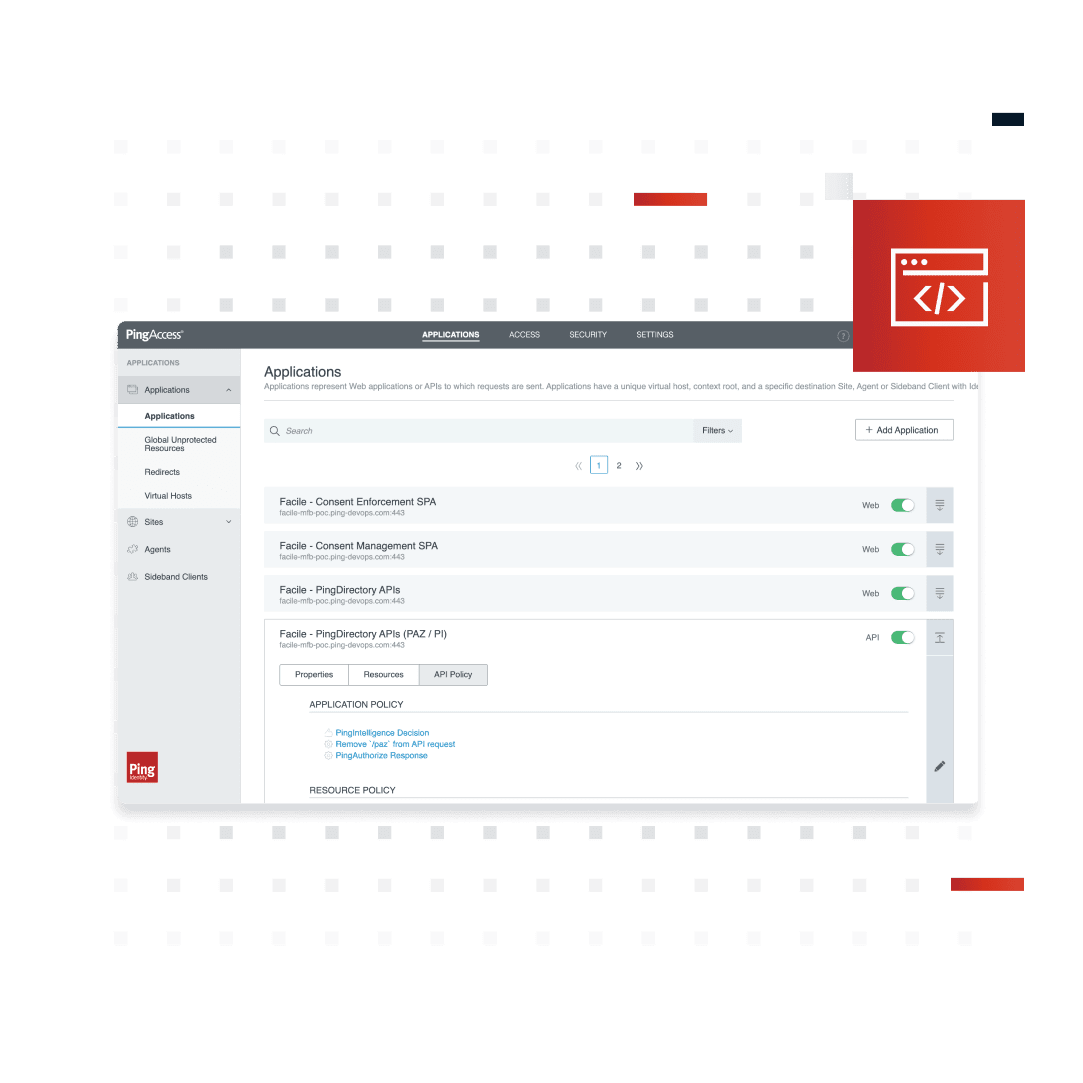
PingAccess is a centralized access security solution with a comprehensive policy engine. It provides secure access to applications and APIs down to the URL level and ensures that only authorized users can access the resources they need. PingAccess allows organizations to protect web apps, APIs, and other resources using rules and other access criteria.
How It Works
PingAccess works in conjunction with PingFederate (or other common token providers with OAuth 2.0 and OpenID Connect (OIDC) protocols) to integrate identity-based access management policies through a federated identity store. Access requests are either routed through a PingAccess gateway to the target site or intercepted at the target web application server by a PingAccess agent, which coordinates access policy decisions with a PingAccess policy server. In either instance, policies applied to access requests for the target application are evaluated and PingAccess makes a policy-based decision to grant or deny access. When access is granted, organizations can modify client requests and server responses to provide additional information.
With PingAccess you can:
Centrally manage access to apps and APIs
Increase API security by applying policies to client requests
Continuously evaluate authentication tokens
User Journey Alignment
PingAccess is integral to the “Authorized” stage of the user journey.
Secure Authorization
PingAccess provides the comfort of knowing that only the right users can access sensitive resources. A comprehensive policy engine ensures that those requesting access have the appropriate permissions, user context, and device posture to access applications down to the URL level. For APIs, policies can be applied to disallow certain HTTP transactions to users in untrusted contexts—such as administrators using DELETE outside the corporate network.
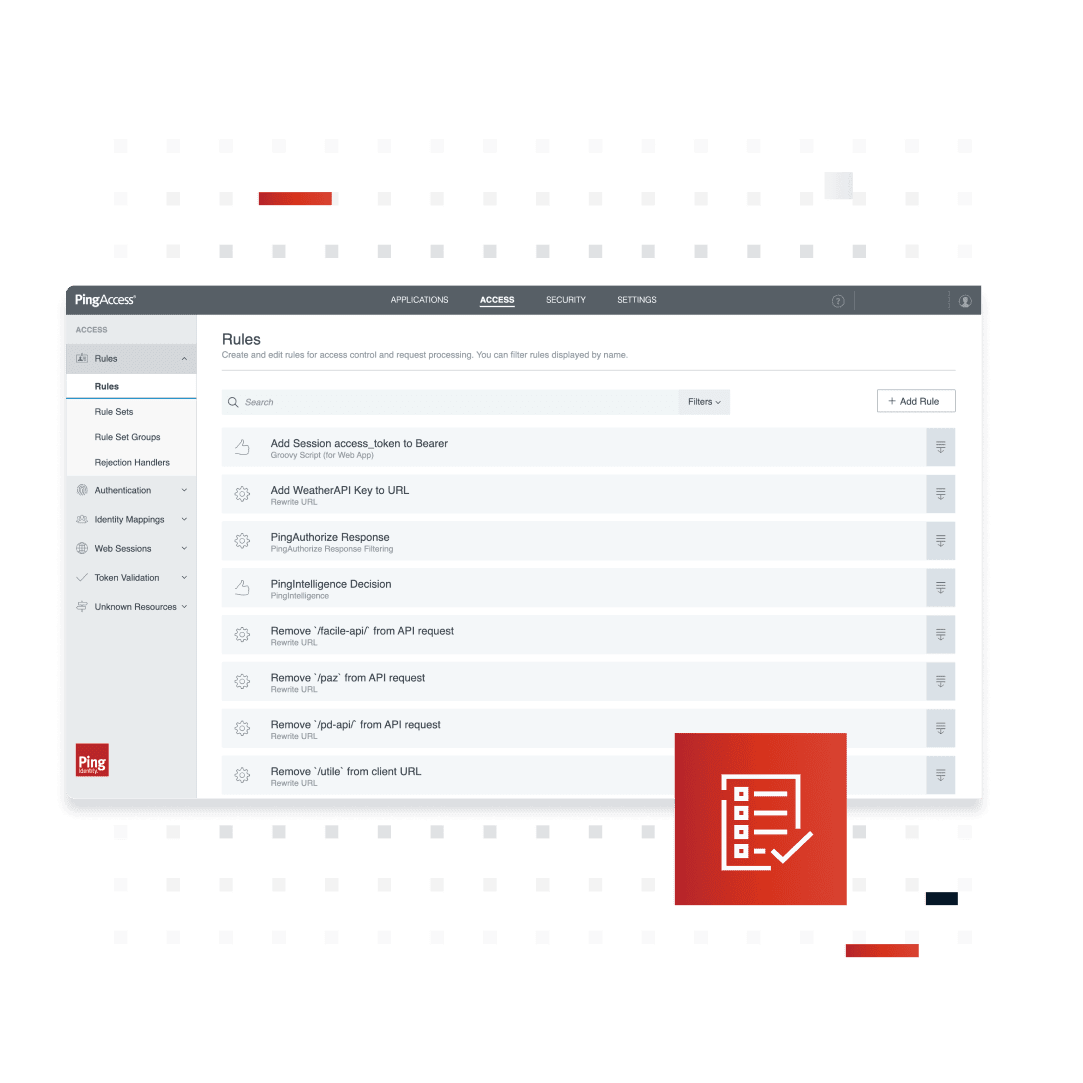
Contextual Policies and Continuous Authorization
By applying policies in context, PingAccess can verify user identity across specific resources by evaluating a diverse range of methods and circumstances. ABAC, RBAC, authentication levels, IP address, web session attributes, and OAuth attributes and scopes can be used to approve or deny access to sensitive resources. PingAccess also integrates with third-party threat intelligence providers to augment contextual data included in authorization policies. It also continuously validates authentication tokens with PingFederate. If there’s a change in user context or if a single logout process terminates a user’s authentication session, all application sessions will immediately be terminated.
Centralized Administration and Session Management
Ensure consistent enforcement of security policies by centralizing access control across application portfolios in hybrid IT environments. From a single console, policies for web applications, APIs, and single-page applications hosted in any domain can be written, managed, and updated. PingAccess abstracts sessions from applications and APIs, removing the risk of errors and inconsistent session security parameters. It also reduces the risk of man-in-the-middle attacks like session hijacking with encrypted session tokens scoped for specific applications.
Migrate to the Cloud
With cloud, API, and mobile-first mandates, it’s easy to see how significantly limiting legacy web access management (WAM) systems are. PingAccess provides a modern, lightweight solution that includes the tools and expertise to coexist or migrate from your legacy WAM. Token translators and policy migration tools help to enable coexistence and avoid downtime disruption.
Granular API Access Control
PingAccess provides foundational API security by controlling access to your enterprise’s internal and public-facing APIs. You can deploy at the perimeter of a protected network between mobile, browser, or server-based client applications and protected APIs to ensure only users with the right attributes can gain access. PingAccess also supports basic API access control, limiting users to transactions permitted by the authorization scopes contained in their access tokens.
Benefits & Features
Delivers access control capabilities beyond web application management, including cross-domain, multi-cloud environments, APIs, and single-page apps
Centralize access management by integrating existing applications without code or architecture changes
Audit all access correlated by identity and context
Write, manage, and update policies for web applications, APIs, and single-page applications from a centralized console
Allow internal and external users to easily access the web apps and APIs they need
Protect and control access to web apps and APIs
Easily integrate with web applications and APIs, gateway and agent deployment models
Deploy in less than 30 minutes
Easily integrate with existing applications without code or architecture changes
Handle tens of thousands of transactions per second with advanced clustering, replication, intelligent rate limiting, and built-in load balancing
Business Value
Increase security
Minimize friction
in the user
experience
Gain IT and
business agility
Flexible Deployment Options
PingAccess can be deployed as:
PingOne Advanced Services - Dedicated tenant cloud services
PingOne Cloud Software - Deploy anywhere cloud containers
Platform Alignment
PingAccess is an integral part of the PingOne Cloud Platform and is essential to the “Authorize” phase of the identity and access management user journey.
Platform Alignment
PingAccess is an integral part of the PingOne Cloud Platform and is essential to the “Authorize” phase of the identity and access management user journey.
Need to Meet FedRAMP or DoD IL5 Requirements?
PingAccess is also offered as part of Ping Government Identity Cloud, a FedRAMP High Authorized and a DoD IL5-certified solution meeting DoD's Cloud Computing Security Requirements Guide (SRG) for Impact Level 5 (IL5).
Start Today
Contact Sales
See how Ping can help you deliver secure employee, partner, and customer experiences in a rapidly evolving digital world.