The following tools are crucial to upholding IAM security. They include but are not limited to:
Single Sign-on (SSO)
Single sign-on is a type of IAM control that enables users to authenticate their identity across numerous resources via one set of credentials. The first time a user signs on, the username and password are directed to the identity provider for verification. The authentication server checks the credentials against the directory where user data is stored and initiates an SSO session on the user’s browser. When the user requests access to an application within the trusted group, instead of requesting a password, the service provider requests that the identity provider authenticates the user’s identity.
Advantages of SSO include:
Attack surface reduced from many credentials down to one
A streamlined user experience and minimized password fatigue
Lowered security risks involving partners, customers and other entities associated with the organization
Multi-factor Authentication (MFA)
When a hacker finds an account supported by only one password and one username, they know they've hit pay dirt. Cybercriminals have access to software purchased on the Dark Web that can send hundreds of thousands of passwords and usernames to this account in less than a minute. Once the account recognizes the right combination of letters, numbers and symbols, the hacker can access the account and potentially get ahold of sensitive company information.
Multi-factor authentication ensures that digital users are who they say they are by requiring that they provide at least two pieces of evidence to prove their identity. Each piece of evidence must come from a different category: something they know, something they have or something they are. If one of the factors has been compromised, the chances of another factor also being compromised are low, so requiring multiple authentication factors thereby provides a higher level of assurance about the user’s identity. These additional factors might take the form of numerical codes sent to a mobile phone, key fobs, smart cards, location checks, biometric information or other factors.
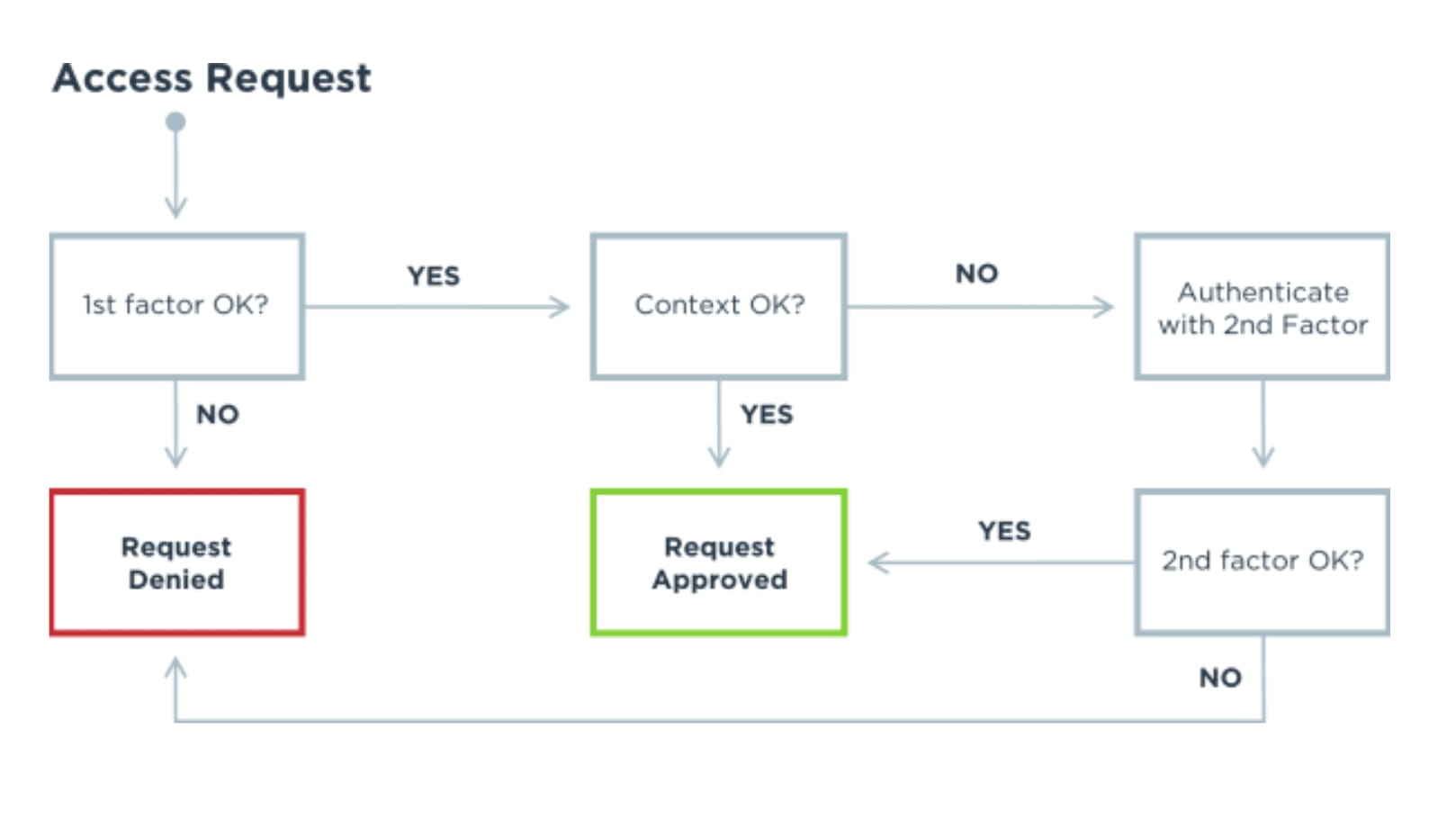
See how an access request works with MFA:
Directory
User identity data is a prime target for attackers, especially when it’s housed across decentralized data stores with inconsistent security policies. IAM security can help keep employee, partner and customer data safe via a directory that centralizes and encrypts identity data, protecting it from attacks. A solid directory solution can also help protect against insider attacks by allowing enterprises to limit admin access and by sending active and passive alerts when suspicious activity occurs.
Self-service Password Resets
One important but often overlooked feature of an IAM security solution is the ability to implement self-service password resets instead of requiring users to send requests to IT department help desks. By enabling employees to use MFA to authenticate their identity and reset passwords, not only do you reduce the number of costly password resets, but the security risk of password hijacking by hackers monitoring system "chatter" is significantly reduced.