Common Agency Environment Credentials
Examples of commonly-found credentials in agency environments—each with their own issuance systems—can be found in the section below.
But before we dive into them, it’s worth noting that as of January 2022, the Office of Management and Budget (OMB) requires agencies to discontinue use of non-phishing-resistant authenticators.3 Therefore, Federal agencies should prioritize transitioning away from the credentials in that category and focus on exclusively using phishing-resistant authenticators.
Non-Phishing-Resistant Authenticators
Out of Band Tokens
Out of band tokens are used in situations such as when an individual has a PIV smart card but a PIV reader isn’t available, the individual requires an authenticator but is not eligible for a PIV card or the individual needs to access an application that doesn’t support PIV. This situation is most commonly associated with legacy or SaaS applications.
One-Time Passcodes
A one-time passcode (OTP) is a single-use password that is generated to support the authentication process. Passcodes can be delivered via software (e.g., email or text) or a hardware token. OTPs are not generally used as a first form of authentication; typically, they are used as a supplemental credential to support multi-factor authentication (MFA).
Phishing-Resistant Authenticators
PIV/CAC Smart Cards
PIV/CAC smart cards—hereby referred to simply as PIV cards—are PKI-based credentials that serve as the Federal Government’s primary type of authenticator. But not all users are eligible for these smart cards.
Non-PIV Smart Cards
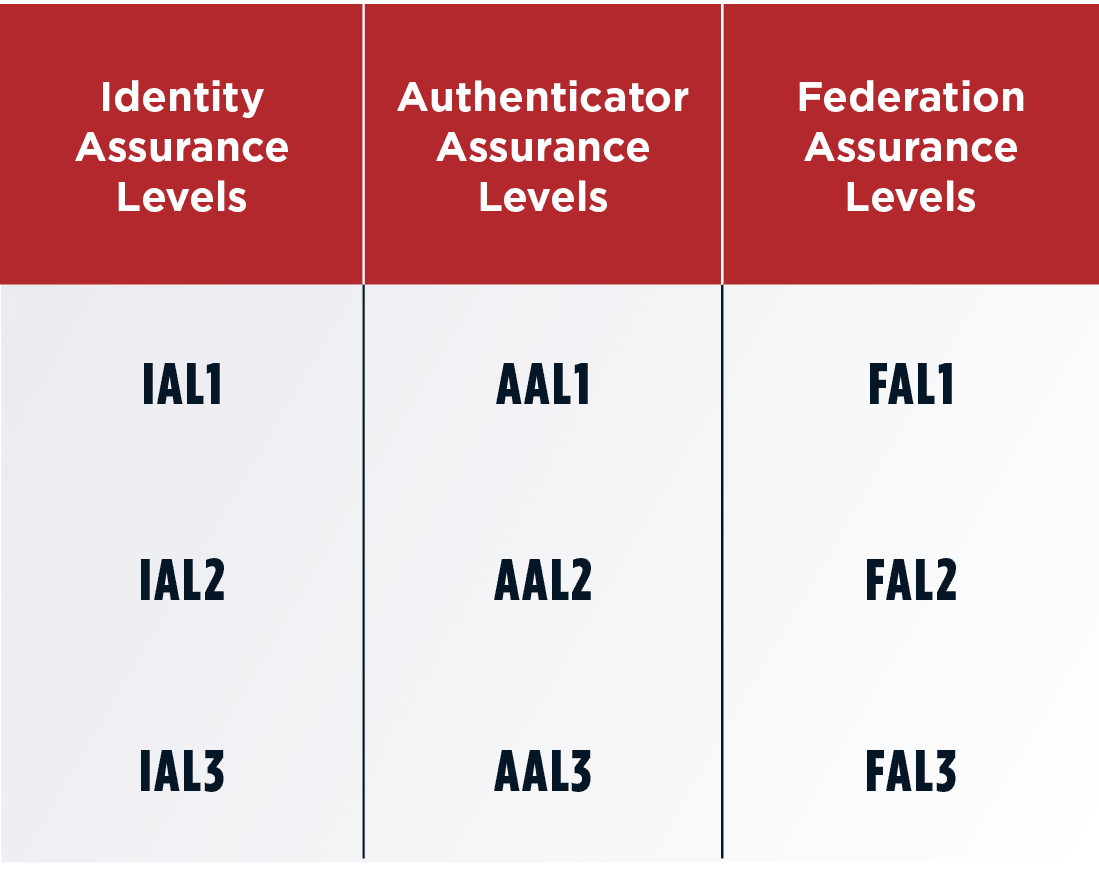
Some individuals aren’t eligible to receive PIV cards but they still need to access resources within the security requirements dictated by LOAs. Therefore, they require some sort of PKI-based smart card to perform their duties, which is why non-PIV smart cards were created.
Derived Credentials
Lastly, derived credentials were introduced to accommodate the rise of mobile devices in the workplace. Physical smart cards don’t work well with mobile devices, as form factors change with nearly every new iteration of a smartphone. It would also be impractical to re-issue smart cards that frequently.
Derived credentials satisfy the mobile use case, but it’s worth noting that they are never issued as an individual’s primary form of authentication. In order to receive a derived credential, an individual must already possess a PIV card.
Common Impacts of Fragmented Identity Ecosystems
Again, each of these credentials were issued by different systems, as agencies wanted to keep boundaries between credential types in order to prevent inappropriate use (whether accidental or intentional). However, the effort to fortify the security of Federal assets resulted in a disproportionate impact on operational efficiency, agility and productivity.
Examples of these impacts include the following.
Lack of Visibility
This siloed, fragmented identity landscape means IT and security teams cannot get full visibility into what identity solutions they even have deployed across the agency. Specifically, because there is no centralized ICAM authority, teams often can’t get insight into what components are deployed where. And even if they can get this insight, the components often require separate administrative logins to manage each system. This means there is no central pane of glass to understand and manage these different components.
Slower Maintenance
To abide by the best practice of separation of duties, every system should have a dedicated administrator. However, with so many identity systems in place, most agencies do not have the resources to allocate a dedicated administrator to each individual system.
This means that oftentimes administrators are responsible for multiple systems. Because of this, it takes more time for agencies to keep their systems up-to-date (including longer Authority to Operate review processes) than it would if each system had its own administrator.
Administrative Burdens
Employees may require access to systems with different security requirements, which means that for every unique system they require access to, they need the corresponding authenticator. As a result, agency employees may need to remember and manage multiple credentials to simply perform their everyday duties.
Administrative Errors
The lack of resources combined with the heavy administrative burden increases the chance of error. Without having centralized visibility into access permissions, agencies rely on administrators to keep track of and remember who has access to which resources and to what degree. This introduces unnecessary risk, such as an account remaining active when it should have been deprovisioned. A cyberattacker could take advantage of this oversight and use the forgotten account that is still active to gain entry to the system (as was the case with the Colonial Pipeline attack).
Interoperability Barriers
Interoperability between agencies is becoming increasingly important. However, establishing this interoperability is complicated by a lack of consistent ownership over identity across Federal agencies, as well as a lack of visibility into the identity vetting process and the identity’s attributes.