If you’re like many enterprises, you’re leveraging APIs to advance your digital transformation initiatives and seize new opportunities. But all of those APIs are also new entry points into your organization's most sensitive data, making it easier for hackers and botnets to steal and manipulate critical information.
While API gateway products can provide foundational security capabilities, they can’t detect many cyberattacks on APIs. But PingIntelligence for APIs can. It helps you protect your enterprise against attacks like:
- Credential stuffing on login systems
- Botnets scraping data and launching DDoS attacks
- Hackers using stolen cookies, tokens or API keys
- Insiders exfiltrating data over time
When it comes to API security, it’s safe to say that PingIntelligence makes your job easier. And its most recent updates make experiencing PingIntelligence for yourself even easier, too.
Easier to Protect Your APIs
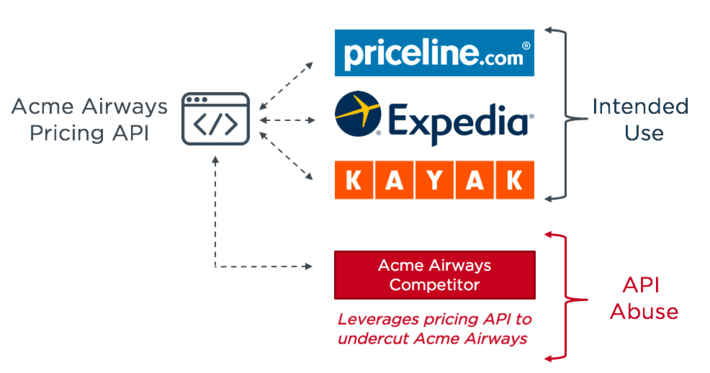
Identifying attacks on APIs isn’t easy for two primary reasons. Firstly, APIs provide more granular and direct access to data and services than web applications. This makes API-based integrations highly efficient, but it also exposes organizations to a new category of API attacks which they aren’t prepared to defend against today. Bad actors, but also competition can leverage exposed functionality and data for unintended purposes. In this example, Acme Airways publicly exposes a pricing API so that price comparison sites can use this information. Unfortunately for Acme, their main competitor has deployed a bot to “scrape” this data with the intention of using it to undercut Acme’s prices whenever a change is made.
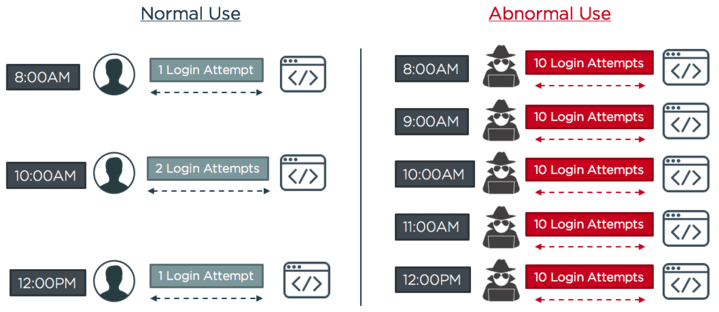
Second, hackers often fly under the radar of attack detection systems when using APIs in their attacks. Rather than using tradition credential stuffing methods like attempting to log in hundreds of times until a successful login event takes place, hackers will instead use bots to programatically attempt API access in ways that wouldn’t be caught by volume based detection systems. An example of this is detailed below:
Hackers execute low volume, programmatic login attacks to avoid detection.
In addition to many other vulnerabilities passing as anomalous behavior, PingIntelligence for APIs now protects against both of these attack vectors, enabling you to identify and block bad actors using these tactics. Today, attacks like these expose gaps in API security which existing tools—like content delivery networks (CDN), web application firewalls (WAF) and API gateways—are unable to detect.
Easier to Deploy with Apigee Integration
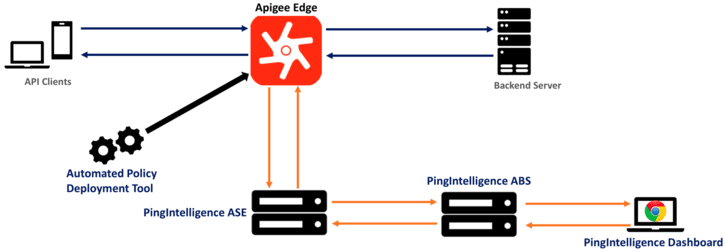
Recently announced, PingIntelligence for APIs is now available via sideband integration with the Apigee Edge full lifecycle API management platform. Apigee customers can now rely on the combined solutions to provide comprehensive API protection. PingIntelligence augments Apigee’s client authentication and threat protection policies with automated API threat detection and blocking on a per API basis. For example, the Apigee platform generates and validates scoped OAuth tokens for a range of clients and purposes, while PingIntelligence for APIs ensures the token presented hasn’t been stolen since its initial issuance.
PingIntelligence provides a shared flow to integrate Apigee Edge with PingIntelligence for APIs’ platform. The two mechanisms of calling shared flows are flow callout and flow hook policies. A Flow Hook in Apigee Edge applies the PingIntelligence shared flow globally to all APIs in an environment under an organization. The Flow Call Out policy in Apigee Edge applies the PingIntelligence shared flow on a per API basis in an environment under an organization.
A logical set-up of PingIntelligence ASE and Apigee Edge
Easier to Try for Yourself
Evaluation of the PingIntelligence for APIs solution is now available through a self-service trial delivered as a cloud-based service. Simply download the lightweight API Security Enforcer (ASE) to connect your API environment with the cloud-based service, then deploy it inline in front of APIs or sideband next to PingAccess or an API Gateway.
You can see for yourself how PingIntelligence for APIs can help protect you against targeted API attacks and improve your overall API security posture by enabling:
- Automated API discovery
- AI-based API threat detection and blocking
- Deep traffic visibility with metrics and forensics reports
- Threat dashboard
- Configurable API deception