What Is Runtime Identity?
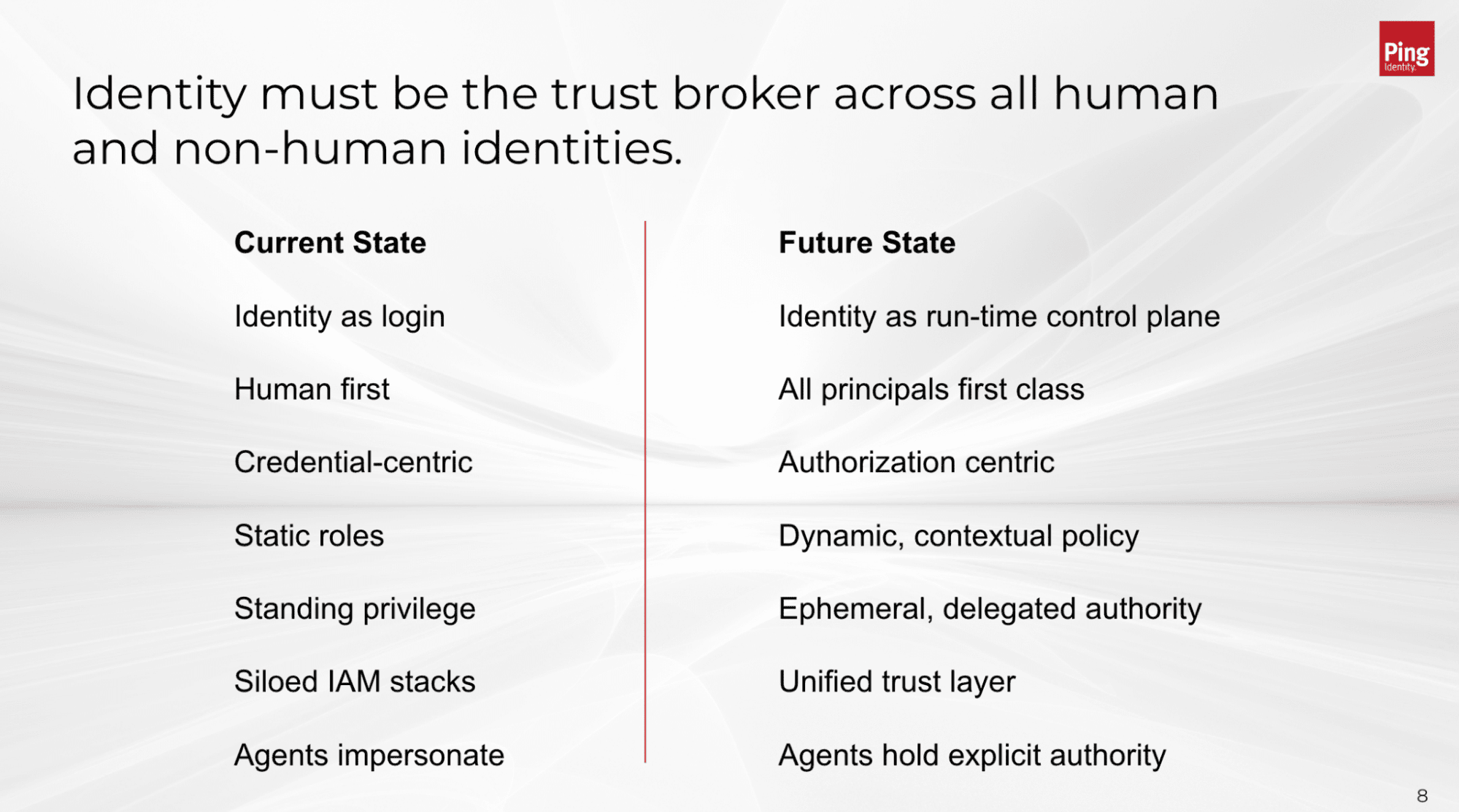
Runtime identity moves the security boundary from access at login to the moment of action at runtime. Traditional security models rely on session-based trust: they authenticate once at login and trust the user’s actions for the rest of the session. But as autonomous AI agents continue to rapidly multiply and gain greater autonomy, a one-time login is no longer enough. Identity must be continuously verified at the moment of action.
Definition of Runtime Identity
Runtime identity is an approach to identity and access management (IAM) where access decisions are continuously evaluated at the exact time an action occurs, under context, rather than just at the start of a session. It treats every request—whether from a human or an AI agent—as a unique decision point checked against real-time context, policy, and risk. This approach is especially important when it comes to the detection, delegation, privilege, and authorization of AI agents.
Key Takeaways
The Security Boundary Has Shifted: Traditional IAM secures the login, but it does not secure the actions after login. Runtime identity moves the security boundary to the exact moment an AI agent or human attempts a task
Continuous, Contextual Authorization: Because AI agents act autonomously and can escalate privileges mid-task, trust must be evaluated continuously based on real-time risk, policy, and context
Enforce Explicit Delegation: AI agents should never "inherit" broad user permissions. Runtime identity ensures agents operate with narrowly scoped, purpose-built authority
Contain the Blast Radius: By evaluating every single action in real time, you proactively prevent unauthorized privilege escalation and limit the potential damage of a compromised agent
A Unified Identity Platform: Manage humans and AI agents under a single architectural model across CIAM, Workforce and B2B use cases, eliminating security silos and simplifying governance across your entire environment
Runtime Identity: Built for a World that Acts in Real Time
Runtime identity builds on existing identity and security models, but it addresses critical gaps that emerge in environments driven by AI agents, APIs, and continuous digital workflows.
For years, identity systems were designed for moments of access—login events, session creation, and static roles. That model worked when systems were predictable and interactions were discrete.
But today’s environments are fundamentally different.
AI agents act autonomously. APIs are called continuously. Developers and services interact dynamically. Context shifts mid-task. Risk evolves after access is granted.
The moment of login is no longer where control is needed. Control is required at the moment of action.
Runtime Identity reflects this shift. It extends identity beyond access to become a trust broker in real time - continuously evaluating every request in the moment based on context, policy, and risk.
This is not a replacement for existing identity approaches, but a natural evolution. As systems become more dynamic, identity must move closer to execution, ensuring that every action, whether made by a human or machine, is explicitly authorized at the moment it occurs.
This shift is especially critical for AI agents, which can reason, chain actions, and escalate privileges independently. But it applies just as broadly to modern architectures - APIs, microservices, and automated workflows - where decisions must be made continuously, not just at the start of a session.
When identity operates at runtime:
Every action becomes a decision point
Authorization becomes continuous and contextual
Privilege becomes dynamic and scoped to intent
Control moves from access to execution
This is how organizations move from granting access to governing behavior.
Why Runtime Identity Matters
As AI agents gain more autonomy and continue to act on behalf of users and organizations, identity must move closer to the action itself. Static access models can’t keep up with systems that operate continuously and adapt in real time.
Security: Prevents overprivileged access by enforcing policies at each action
Risk reduction: Limits blast radius if an agent is compromised
User trust: Ensures actions taken on a user’s behalf are controlled and transparent
Business agility: Enables safe adoption of AI without slowing innovation
Compliance: Improves auditability by tracking who (or what) did what, and why
How it Works
Identity systems weren’t originally designed for continuous, autonomous behavior. Runtime Identity shifts the security boundary from a one-time checkpoint to a continuous control system.
Actors and Identities: Every human, service, and AI agent is recognized as a first-class identity
Contextual Signals: The system analyzes real-time clues, including device health, location, behavior patterns, and data sensitivity
Continuous Evaluation: Every request is checked against centralized policies in real time, under context
Dynamic Enforcement: Access is granted, denied, or "stepped up" (requiring extra verification) instantly based on the current risk profile
Key Use Cases for Runtime Identity
Runtime identity becomes critical anywhere actions are dynamic, delegated, or automated.
AI Digital Assistants: Control what data an employee's assistant can access and what actions it can perform on their behalf
Agentic Commerce: Allow personal agents to shop and purchase within defined, real-time limits without granting full account access
High-Risk Transactions: Trigger additional verification the moment a sensitive action is attempted, such as moving large sums of money or changing security settings
API & Workforce Automation: Ensure digital workers and service-to-service calls are validated at every request, reducing the "blast radius" of a potential compromise
Best Practices for Runtime Identity
Organizations adopting runtime identity should focus on control, visibility, and least privilege.
Evaluate access continuously: Enforce policy at every action, not just at login
Apply least privilege dynamically: Adjust permissions based on real-time context
Use delegated access models: Avoid credential sharing; grant scoped authority instead
Incorporate human oversight: Require approval for high-risk or irreversible actions
Monitor all activity: Log and analyze every action for audit and anomaly detection
Limit token lifespan: Use short-lived credentials to reduce exposure
Centralize policy enforcement: Ensure consistent decisions across systems and agents
Frequently Asked Questions
Runtime identity means checking access at the moment something happens at runtime, not just when a user logs in. It ensures every action is verified in real time.
Traditional IAM verifies identity once at login and assumes trust afterward. Runtime identity continuously verifies each action as conditions change.
AI agents act autonomously and continuously. Runtime identity ensures their actions stay within approved boundaries at all times.
No. Authentication still verifies who or what is acting. Runtime identity builds on that by controlling what actions are allowed afterward.
It reduces overprivileged access, limits exposure if credentials are compromised, and ensures every action is evaluated against current risk.
No. While critical for AI agents, it also benefits APIs, microservices, and any system where context and risk can change during a session.
Organizations risk overprivileged access, lack of accountability, and inability to control actions after login, especially with autonomous systems.
Start Today
Contact Sales
See how Ping can help you deliver secure employee, partner, and customer experiences in a rapidly evolving digital world.