Depending on your security policies and user base, several delivery methods are available. Choosing the right one comes down to balancing security, accessibility, and the experience you want to provide your users.
Each of these delivery channels carries a different balance of usability and security, but they’re increasingly evaluated alongside phishing-resistant options like FIDO2-based passkeys and platform biometrics so that the right method can be applied to the right context.
SMS OTP
A unique and time-sensitive code is sent to a user's mobile device via a text message. This method is extremely popular due to its speed and convenience. Because SMS is vulnerable to threats like SIM swapping and message interception, it is now generally treated as a lowest-common-denominator option for low-risk scenarios or legacy user segments, not as a control for protecting sensitive actions.
Voice OTP
A code is delivered through an automated voice message over a phone call. This is considered secure since the code is delivered audibly directly to a specific number.
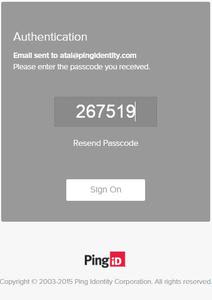
Email OTP
Codes are sent directly to a user's inbox. While this adds an extra layer of security since users must log into their email, some question this method because emails are not tied to a specific physical device. As a result, email OTP is typically positioned as a convenience or recovery factor for low-risk flows, while more sensitive operations are shifted to passkeys and biometrics tied to specific devices or trusted providers.
Messaging Apps
Codes are sent via popular messaging apps like Telegram or WhatsApp. Users enjoy the added security of these platforms because they automatically encrypt messages. Even with end-to-end encryption, messaging-app OTPs largely mirror the risk profile of SMS and email, so they are best suited to low-risk scenarios.
Hardware Keys
Physical devices generate one-time codes with the push of a button. Certain organizations prefer hardware keys since they operate offline and are inaccessible to remote fraudsters.
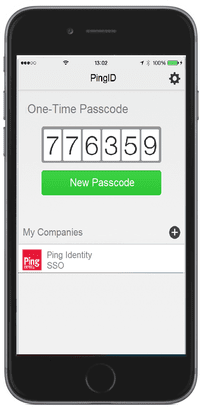
Authenticator Apps
Codes are generated by mobile applications like PingID. Since these apps work offline and entirely within user devices, they are considered extremely secure. Authenticator apps—such as PingID—sit at a sweet spot for many organizations: when you can rely on a user’s personal device, they offer one of the best balances of security and friction. Increasingly, these apps don’t just generate OTPs; they also manage device-bound credentials and leverage local biometrics, making them an ideal choice for medium-risk scenarios where strong assurance and good UX are both essential.