Preventing these incidents requires a layered defense strategy. No single control eliminates risk entirely, but combining multiple methods significantly reduces the attack surface. The following approaches range from simple configuration changes to advanced authentication mechanisms. Organizations should implement as many as feasible based on their risk profile, user population, and technical capabilities.
Limit Authentication Attempts
The easiest option to address MFA bombing is limiting the number of prompts sent to a user within a specific timeframe. Even trained users may approve a push notification after being prompted ten times, so limiting the number of prompts to three to five attempts, for example, can help. Most enterprise MFA solutions include this as a standard configuration option. However, this is a baseline defense and should be paired with other controls.
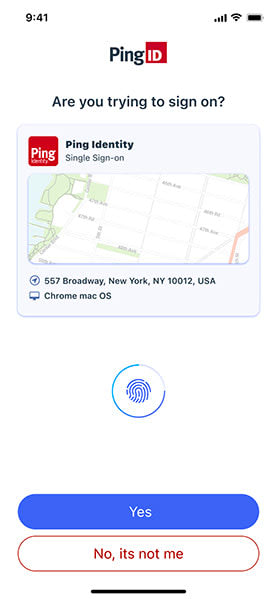
Add Contextual Information to MFA Prompts
Providing users with authentication request context (such as IP address, device type, browser, location, and timestamp) helps them identify suspicious requests. For instance, seeing a notification flagging a log in from an unfamiliar geographic location reduces blind approval by requiring conscious evaluation.
When the push notification is received, the user can review the contextual authentication information, decide whether it is legitimate, and accept it or reject it.
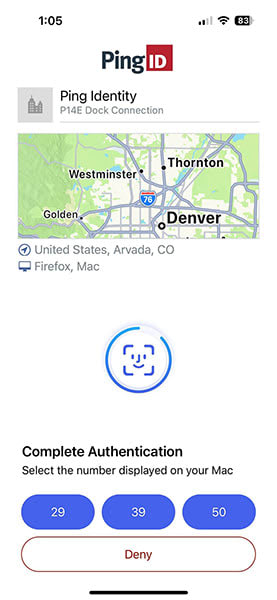
Require Number Matching Verification
Number matching forces proximity by presenting a two-digit number on the login screen and asking the user to select or enter it in their authentication app. This prevents absent-minded approval because the user must actively engage with both devices.
Leading identity and access management (IAM) providers now offer or mandate number matching because it significantly improves security with only a slight increase in friction.
Leverage Device Trust Signals
Authenticating the device in addition to the user creates a more complete trust picture. Organizations can establish a known device inventory and require MFA only for unknown or noncompliant devices. Advanced threat protection capabilities can assess device posture alongside user credentials. If an unknown device attempts access even after approval, the system can trigger additional verification or block the request entirely.
Use Risk-Based Authentication
Beyond tweaking the settings of MFA prompts, risk-based authentication (RBA) is a more targeted option for dismantling MFA bombing. RBA is adaptive and helps create intelligent access policies based on data inputs and risk signals such as location, device, network, time of day, and user behavior patterns.
When users see prompts less frequently, they pay more attention to each one. For example, if the user attempts to log in from a known device at a known location, the risk of account takeover is low, and no MFA is required. However, if the login attempt is from an unknown device at a location that was never previously used, the risk of fraud is high and requires stronger authentication, perhaps via a QR code. Organizations that leverage RBA through advanced threat protection capabilities have seen significant reductions in unnecessary MFA prompts.
Implement Phishing-Resistant Authentication (FIDO2)
FIDO2 (Fast Identity Online) allows users to authenticate biometrically on security keys or other FIDO-compatible devices. It is considered the gold standard because it can eliminate push notifications entirely by enabling authenticators like Face/TouchID. Instead, users authenticate with a physical security key or biometric scan that cannot be remotely triggered by an attacker.
FIDO2 is resistant to phishing, man-in-the-middle attacks, and prompt flooding. While implementation can involve hardware costs, it is ideal for high-risk users such as executives and IT administrators. Supporting FIDO2 through passwordless authentication and adaptive MFA capabilities is critical to offering an experience that improves usability while strengthening security.
Educate Users on MFA Security
Organizations must put strong security tools in place in order to protect themselves and their users, but user education is another key part of stopping MFA bombing attacks. This notion is particularly true for certain segments of the population like the elderly who might not be as current with modern smartphone technology.
Organizations should educate users on their MFA policies so people know what to expect when they log in to a digital property. Beyond that, teaching users about online fraud techniques like prompt bombing is a great way to spread awareness, while also giving them the tools to protect themselves.