Comply with Cloud-first Mandates
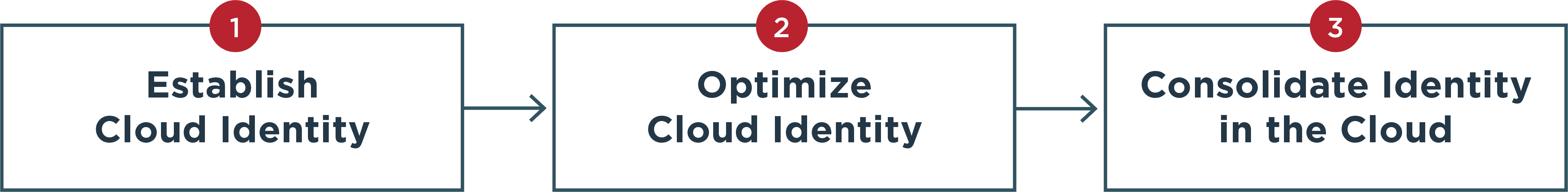
Digital transformation, including moving identity infrastructure to the cloud, is a high priority for some companies. Cloud IAM increases deployment speed because implementation is hosted in the cloud rather than on-prem, which would require investments in equipment and personnel. Upgrades are also easier, particularly when the service is managed by the vendor in the cloud.
Reduce IT Infrastructure and Support Costs
With more people working from home and using personal devices for work, shopping, social media and other activities, IT teams are required to manage more apps, resources and devices. On-prem IAM may be insufficient and the costs associated with employing and keeping in-house identity experts current on threats continue to rise, as does purchasing and maintaining equipment. Those costs can be greatly reduced using an Identity as a Service (IDaaS) or managed cloud service provider for cloud IAM.
Flexibility and Scalability
IAM solutions deployed in the cloud are available as a SaaS service, a managed service deployed in the vendor's private cloud, and as software deployed in the organization's own private or public cloud. Cloud IAM solutions are easy to scale for new users, such as when a company is adding hundreds of employees at a new location or an ecommerce site is running a promotion to attract thousands of new customers.
Enhance Security
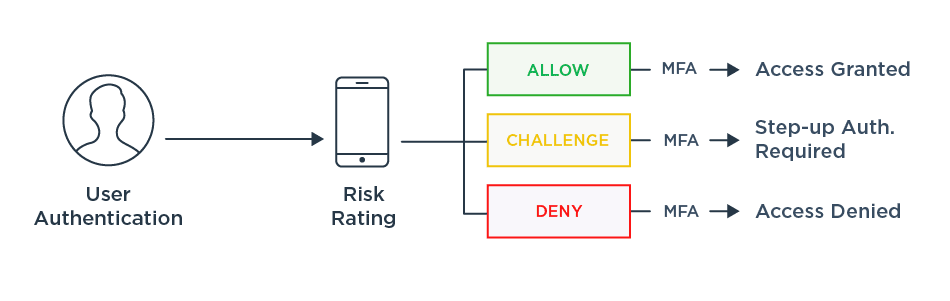
Cloud IAM enhances security with capabilities like two-factor authentication (2FA) and multi-factor authentication (MFA) that reduce reliance on passwords and the potential data breaches that come from compromised credentials. Both 2FA and MFA verify a user’s identity using multiple authentication factors. Passwordless authentication streamlines access even further by reducing or even eliminating the use of passwords.
Improve User Experience
Single sign-on streamlines the login process and gives users faster and easier access to the resources they need. Cloud IAM solutions are available for customers, employees and partners. From customers looking for a frictionless login experience at ecommerce sites to employees trying to get their work done using multiple applications throughout the day, using one set of credentials saves time and frustration.
Minimize Password Reset Requests
IAM solutions minimize reliance on passwords and the risks associated with stolen or compromised passwords. It is estimated that upwards of 50% of IT help desk calls are attributed to password resets. Forrester estimated that a single password reset request costs companies an average of $70.
Increase Productivity and Reduce Frustration for your Workforce
Employees typically need access to a range of applications every day, such as email, online meetings, HR, finance or CRM systems, to name just a few. When workforce users are required to create new accounts for each and use multiple passwords, which they may forget, productivity goes down. By minimizing the time spent on logins, IAM helps employees, contractors and other workers gain access to the resources they need faster and with less friction.
Regulatory Compliance
Cloud IAM helps enterprises comply with open banking requirements like the Payment Service Directive 2 (PSD2) and data privacy regulations like the General Data Protection Regulation (GDPR) and the California Consumer Protection Act (CCPA). As regulations are updated and new regulations are implemented, IAM allows you to quickly adapt and stay in compliance.