- Increased Productivity
- Improved Security
- Strengthened with MFA
- Enhanced with Risk-Based Authentication (RBA)
- Decreased IT Costs
- Improved Job Satisfaction for Employees
- Enhanced Customer Experience
- Increased Adoption Rates
- Tighter B2B Collaboration
- Regulatory Compliance
1. Increased Productivity
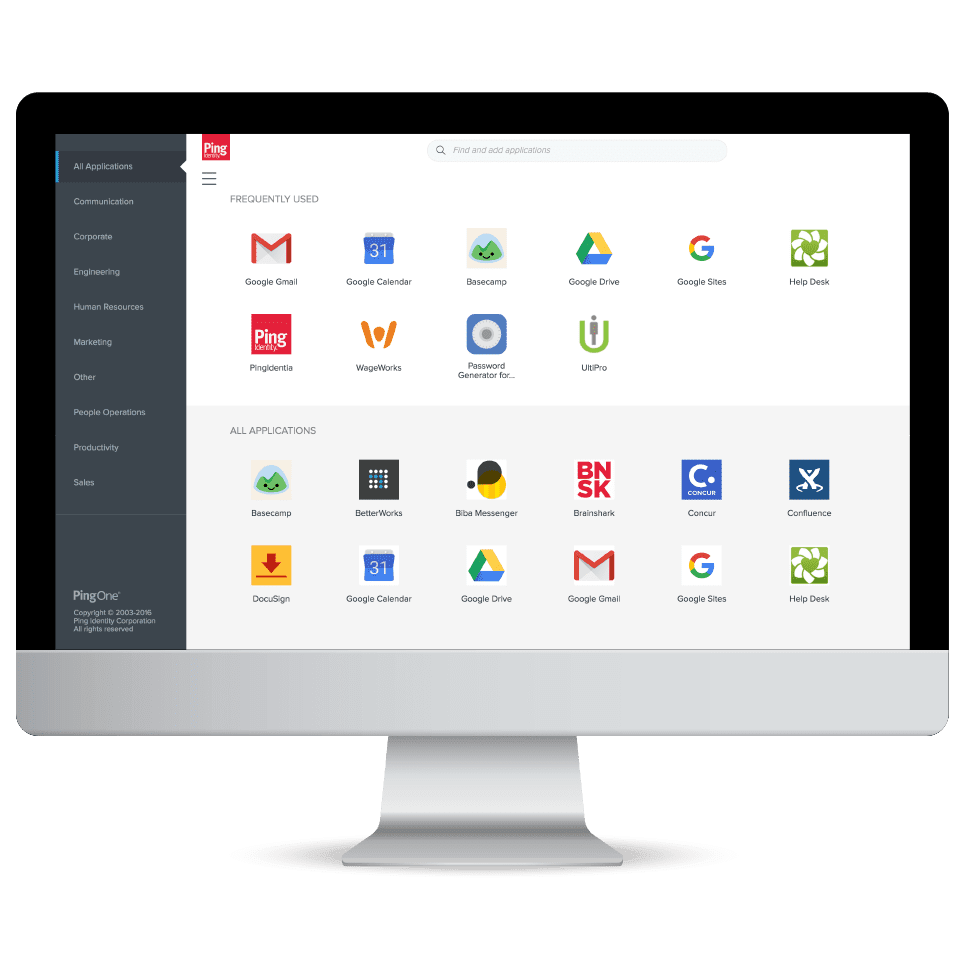
SSO increases employee productivity by reducing the time they must spend signing on and dealing with passwords.
In a workforce context, employees only need one password to access all of their apps, which can save them time logging in, thus increasing productivity. SSO solutions often give them access to a dock where all their apps are available, further enhancing the employee experience and allowing them to focus on their job tasks more quickly and efficiently.
2. Improved Security
A common myth about SSO solutions is that they compromise security. This misconception is based on the idea that should a master password be stolen, all related accounts will be exposed. However, the reality is that with good practices, SSO significantly decreases the likelihood of a password-related hack. With SSO, users only need to remember a single password for all their applications and are more likely to have secure passphrases. They are also less likely to reuse passwords or write them down, which reduces the risk of theft. A further benefit is that authentication policies can be centralized across the application landscape, making management and enforcement of things like password complexity and MFA methods more streamlined.
3. Strengthened with MFA
To provide an additional layer of security, SSO can be combined with MFA capabilities, which require users to provide two or more pieces of evidence to prove their identity when signing on. For example, a password and one-time password (OTP), generated on or securely delivered to one of their mobile devices. Modern MFA also includes passwordless technologies, such as FIDO2 passkeys, which help combat vulnerabilities created by passwords, like phishing attacks.
4. Enhanced with RBA
RBA, or risk-based authentication, is another strong security feature security teams can utilize to bolster their SSO process. RBA permits the use of tools to observe user activity and context to identify any strange behavior caused by an unauthorized user or cyberattack. For example, multiple login failures or incorrect IPs could trigger the system to require MFA or block the user completely depending on the circumstances.
5. Decreased IT Costs
Gartner estimates that 40% of all help desk calls are due to password issues. Another study by Forrester reveals password resets1 cost organizations upward of $70 per fix. SSO drives down help desk costs by reducing the number of required passwords to just one.
Some organizations have implemented specific password complexity requirements, like length and the use of special characters. However, these requirements may make passwords more difficult to remember. This can lead to more users constantly having to reset their passwords, fueling password fatigue and login frustration. These challenges are not only aggravating for users, but they also place added strain and costs on IT teams.
With strong identity verification capabilities, including document verification and liveness checks, a password reset option, and other account recovery use cases, can be self-serviced. This further improves the user experience, while also driving down operational costs and improving security.
6. Improved Job Satisfaction for Employees
Employees are using an increasing number of applications in the workplace, with each often requiring unique login credentials. This places a lot of burden on workers and can be time consuming and frustrating. It was found that an average of 68% of employees have to switch between ten apps every hour.
SSO enhances job satisfaction by allowing employees to work without interruption and quickly access everything they need. Easy access is particularly valuable for employees that are in the field or working from multiple devices.
7. Enhanced User Experience
SSO solutions are not only for workforces, but they’re also for customer use cases. Findings from our 2024 Consumer Survey reveal 54% of global consumers have abandoned an account or online service due to login frustrations, and 75% wish they could change how they log in to apps and websites they frequently use.
Retailers, healthcare providers, banks, and other B2C organizations can eliminate these issues and give customers access to everything they need with SSO. Users will enjoy a more seamless experience with less friction and less frustration. The immediate benefits of improved user experiences include customer loyalty, higher conversion rates, and enhanced brand visibility.
8. Increased Adoption and Engagement Rates
The competitive nature of today's market means customers have plenty of alternatives. If they experience too much friction or confusion when interacting with your brand or trying to purchase your products, they will seek out another option, and fast. SSO increases the chance users will choose you more frequently.
9. Tighter B2B Collaboration
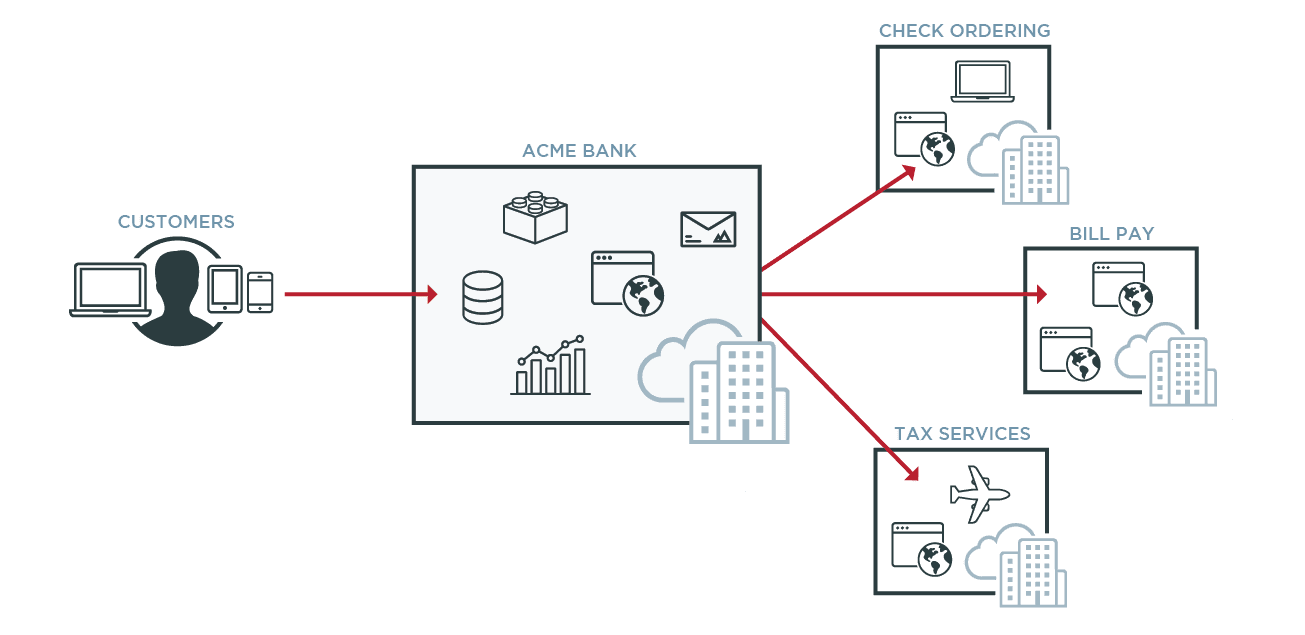
SSO plays a critical role in the success of B2B partnerships as well. Everything from cars and phones to essential home items are built and distributed through collaborative efforts between multiple enterprises. This type of business collaboration requires giving employees from other companies access to specific data, digital tools and applications. Federated SSO (or federated identity management) can help create more efficient and effective collaboration between businesses by bridging identity systems.
Businesses also often collaborate to provide related services to joint customers. Federated identity management simplifies access to services from multiple companies, enabling customers seamless access across company boundaries.
10. Regulatory Compliance
Industry regulations like Sarbanes-Oxley and HIPAA require companies to implement security measures to protect data. SSO is often implemented as part of a broader identity and access management (IAM) solution. This combination can help you comply with regulations requiring strong authentication and access control. IAM can also help businesses comply with other regulatory requirements pertaining to privacy, activity tracking, and single logout.