There are four grant types in OAuth 2.0—authorization code, implicit, resource owner password credentials and client credentials—and which one you should use will depend on the use case. I've covered authorization code in a previous post, and now it’s time for another important and useful grant type that’s very different: the implicit grant type.
You may recall from my earlier post that authorization code flow is the best possible flow for security, and if you can use it, you should. But there are going to be situations where time efficiency is paramount. That’s where implicit flow comes in, because it is designed for lightweight applications. With the explosion of Angular, React.js, other frameworks, and the ease with which you can make SPA’s (Single Page Applications) or client-side rendering apps, keeping things lightweight and fast are important considerations and the security concerns are covered.
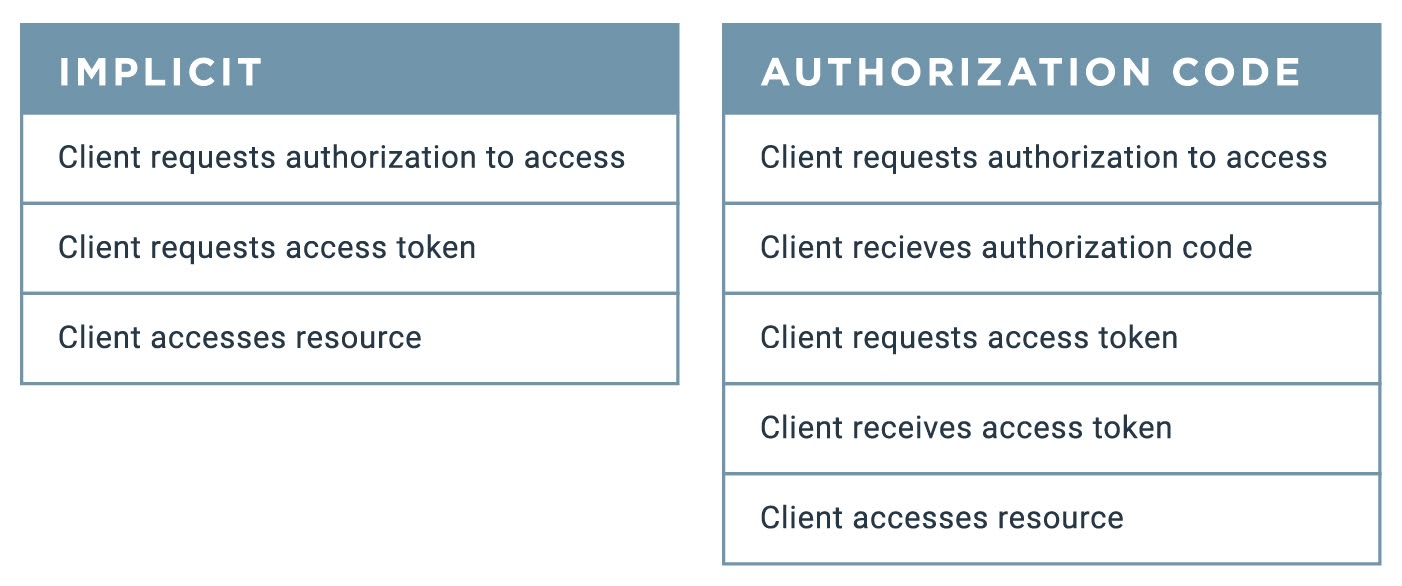
The key distinction between how these two flows work is that implicit flow skips a step taken by the authorization code flow. This blog will focus on the subtractions made to the overall abstract flow, so it’s a good idea to be somewhat familiar with the different roles (even if it’s just knowing there are different roles) and the overall path.