Key Takeaways
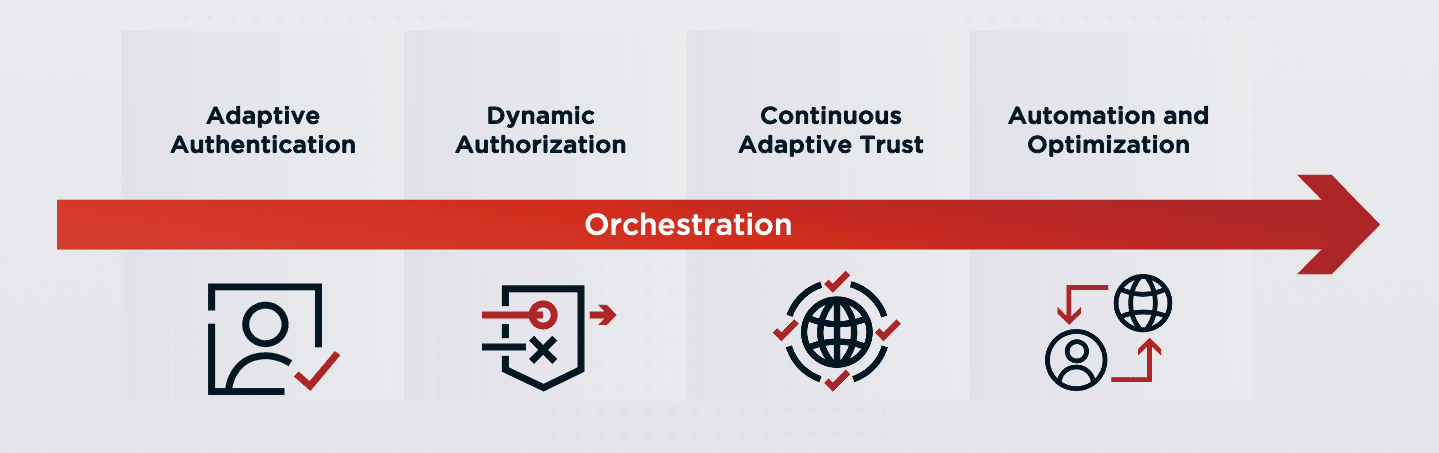
Continuous Evaluation: Move beyond one-time checks by reassessing user trust throughout sessions, transactions, and resource requests everywhere as needed.
Adaptive Controls: Use device, network, and behavior signals to adjust permissions, step up assurance, and reduce friction responsibly for users.
Zero Trust Alignment: Treat continuous adaptive trust as a milestone that complements broader architecture work across workforce, partner, and customer programs.
Identity-Centric Execution: Combine risk detection, decision engines, orchestration, and identity verification solutions to protect data and experiences at scale.
Since the term "Zero Trust" was coined over a decade ago, it's become the de facto cybersecurity paradigm.1 And for good reason: understanding security broadly through the lens of trust in users ultimately better protects your organization's resources.
But Zero Trust is a journey that hinges on how well you can truly evaluate trust in a user when handling their access requests day in and day out. Adopting a continuous adaptive trust model, where user trust is continually reevaluated, is a crucial step on the road to a full Zero Trust architecture.