In the digital world, determining whether someone is who they say they are can be a delicate balancing act. Strong security is vital for protecting your enterprise from breach and privacy violations, and you can’t simply fling open the virtual door to your resources before verifying who is ringing the bell. But make the authentication process too cumbersome and you end up with frustrated end users, which can lower employee productivity, annoy valued partners and drive away customers in search of a better user experience.
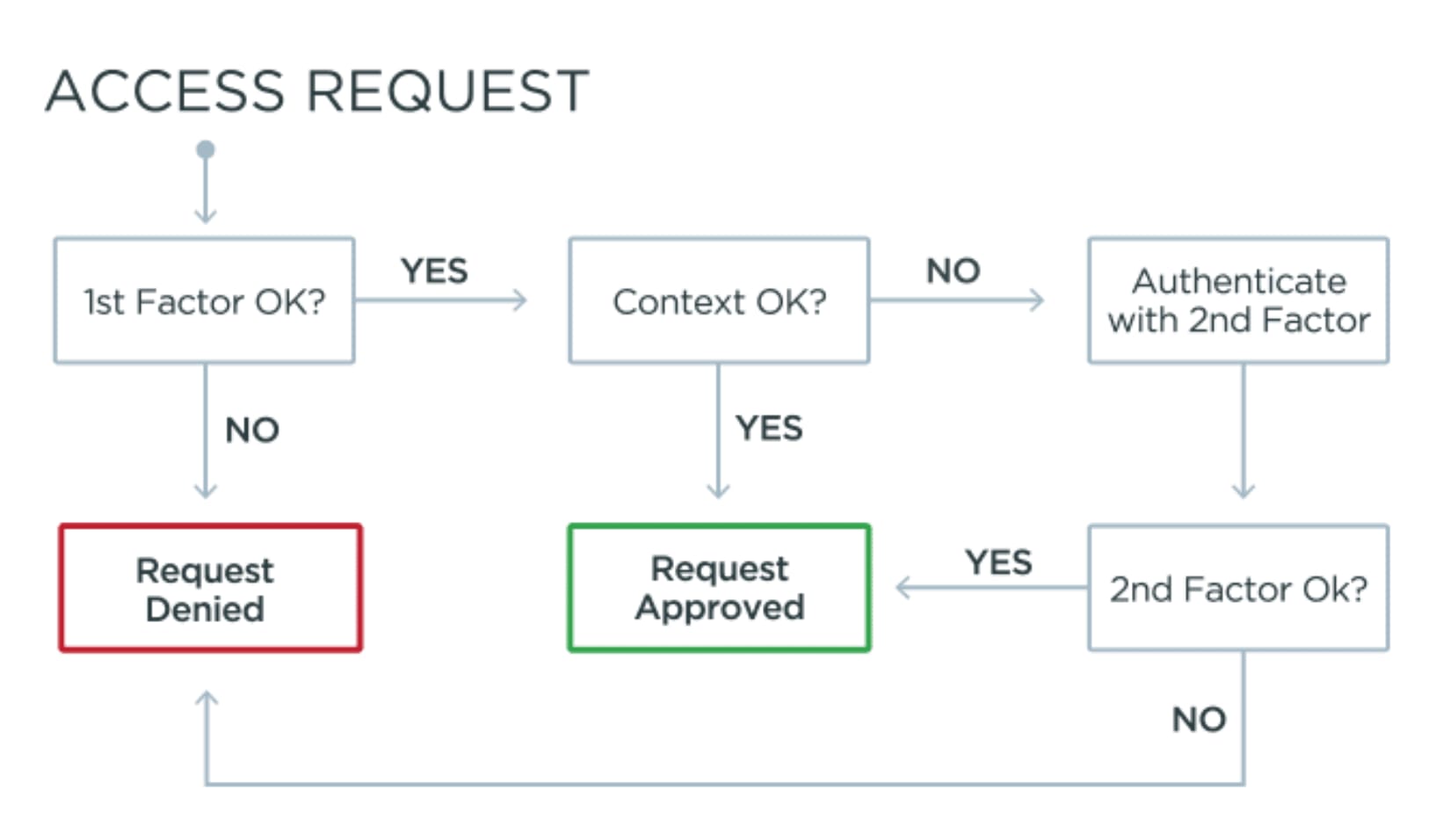
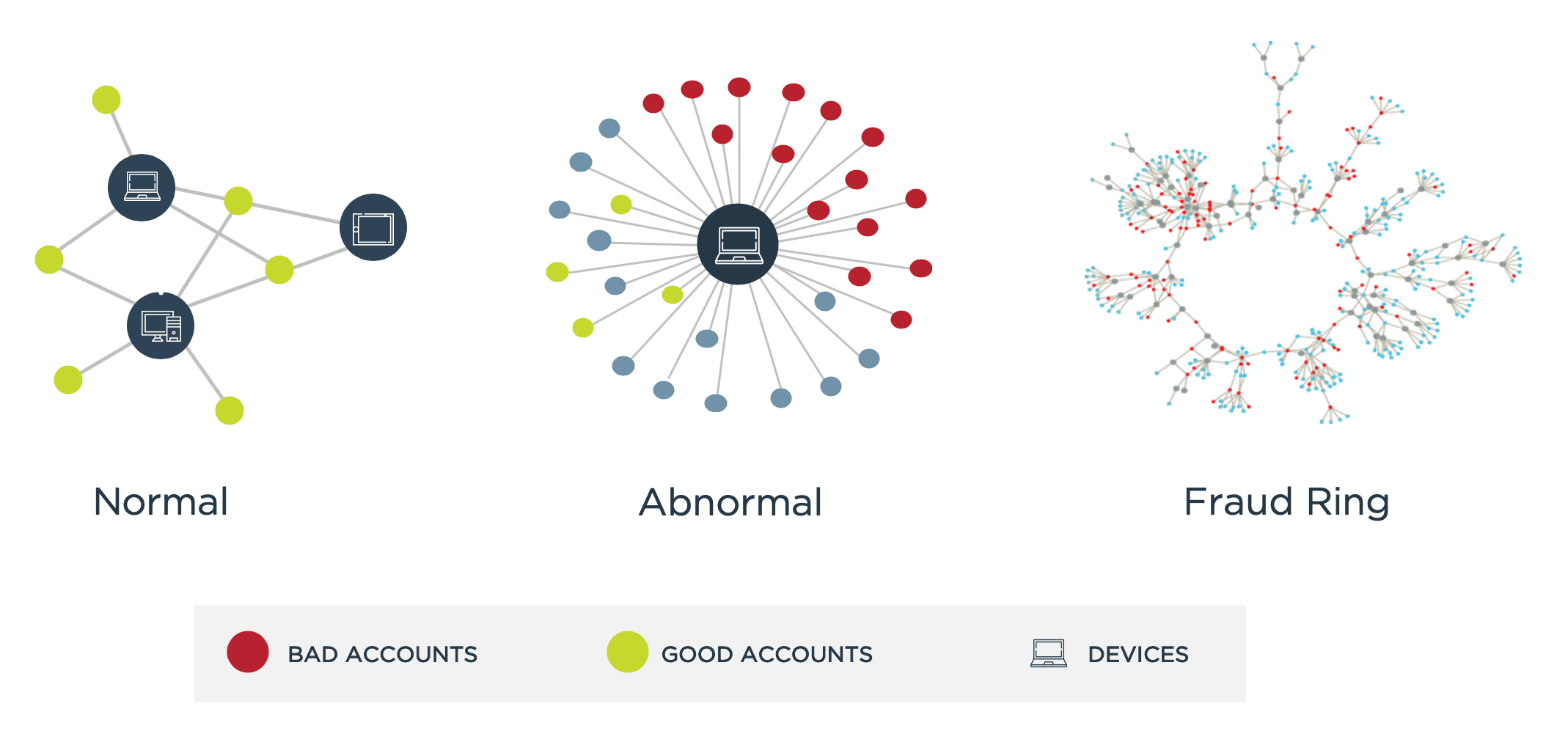
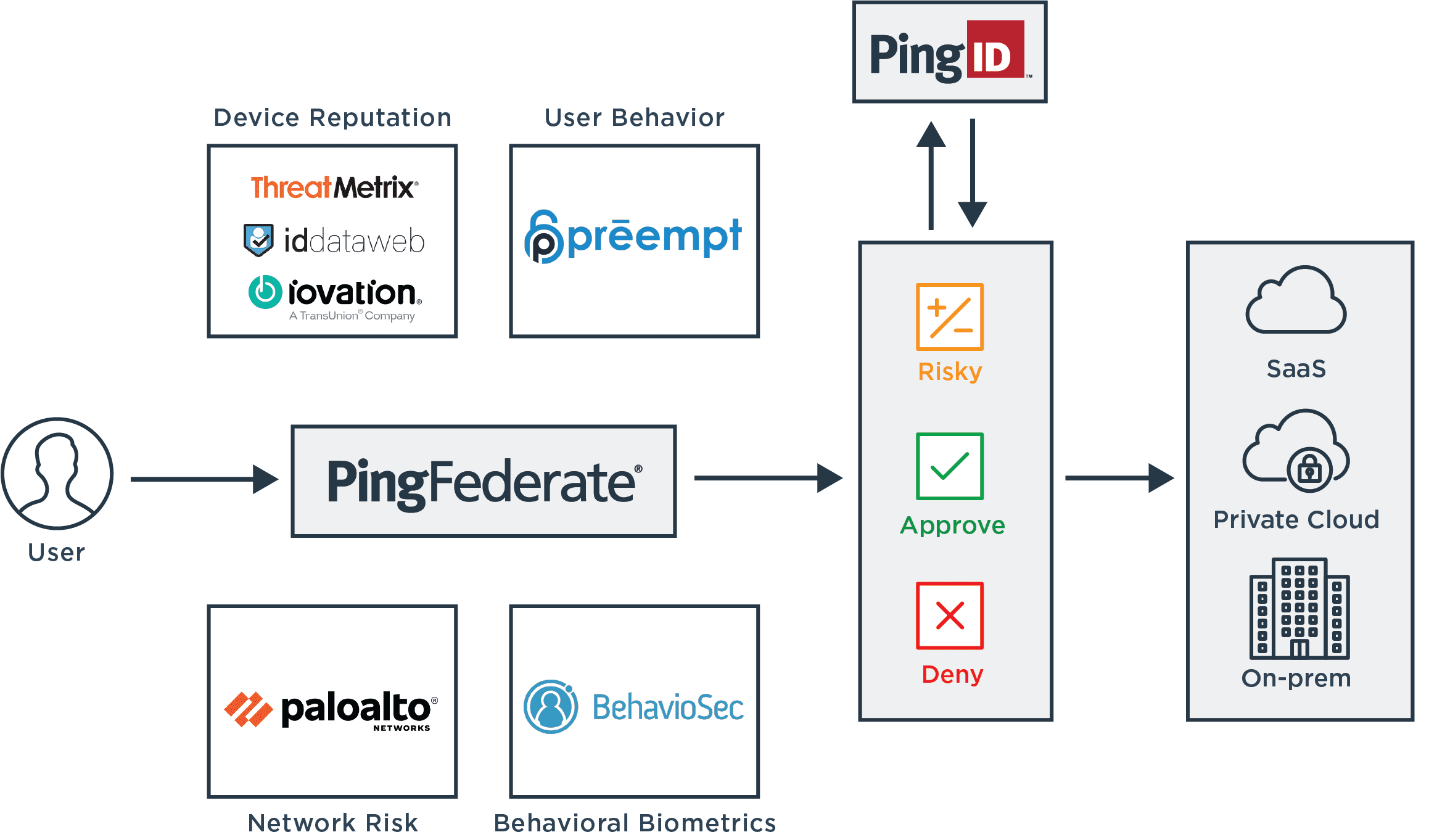
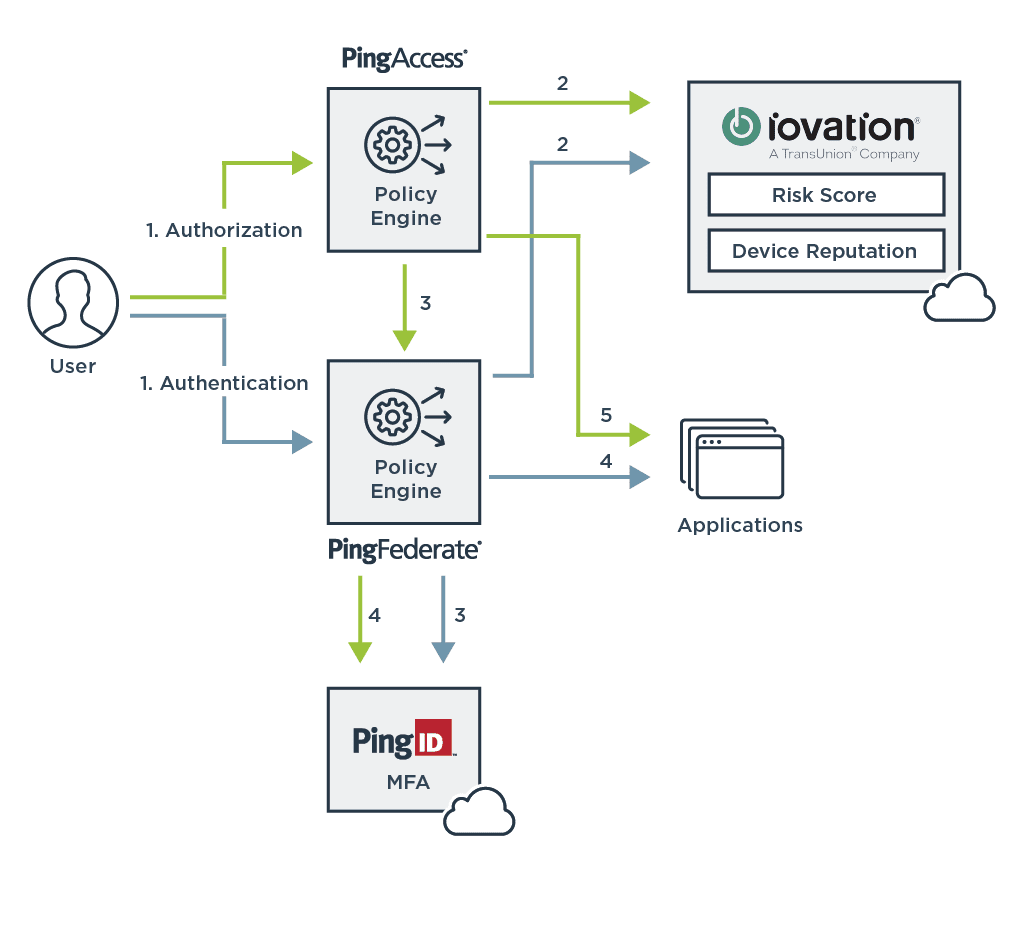
Creating the best digital experience possible while providing the necessary security often hinges on risk-based authentication: the concept of dynamically assessing the risk of a given interaction based on a variety of factors and adjusting the authentication process accordingly. Risk-based authentication can provide just the right balance of strong protection with frictionless user experience, and Ping’s powerful integrations enable your enterprise to choose the optimal authentication techniques for your business needs.