If you’ve been following this blog post series on the different OAuth 2.0 grant types, you’ll know that we’ve already covered three of the four types: authorization code flow, implicit grant flow and client credentials. Congrats on making it this far!
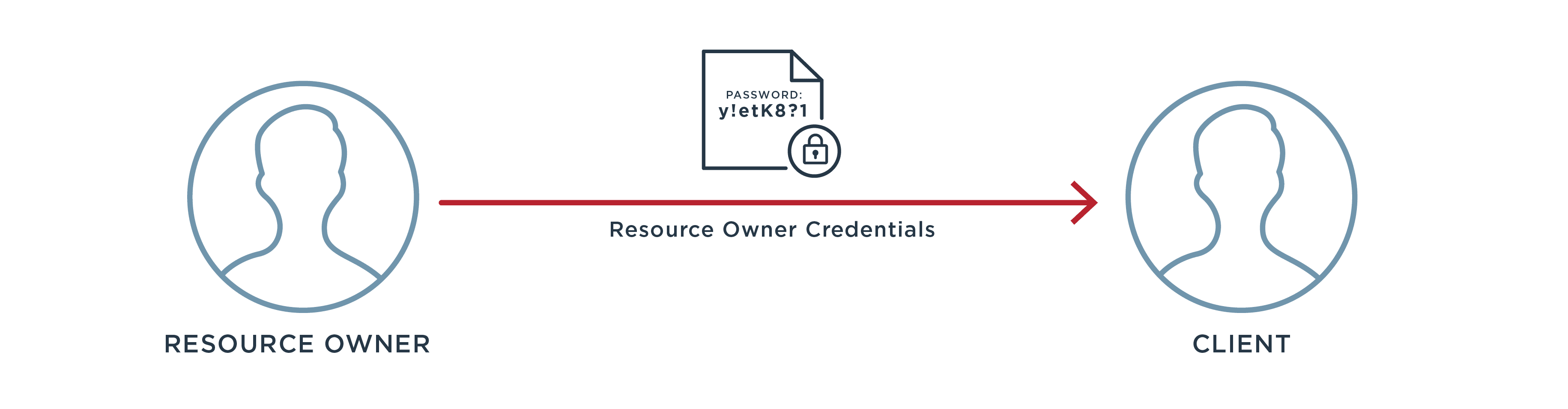
We’re at the final grant type: resource owner credentials. This one is pretty simple in concept, but be aware I’ve left it for last for a good reason. If you take just one piece of information away from this post, let it be that this grant type should be avoided whenever possible.