Zero Trust is quickly becoming essential for financial institutions as they navigate an increasingly complex regulatory landscape. With the constant evolution of cybersecurity threats, regulatory bodies and government initiatives are placing greater emphasis on the need for a comprehensive approach to securing financial systems.
Regulatory Landscape in the United States
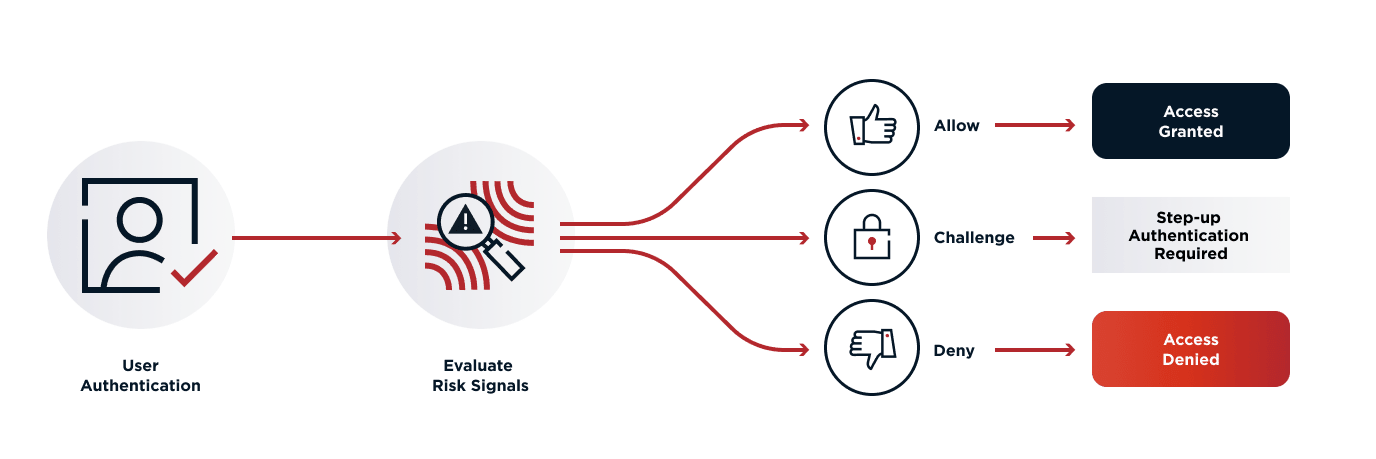
In the United States, regulations provide a detailed framework for implementing Zero Trust, emphasizing continuous monitoring, dynamic risk assessment, and real-time threat detection.
Key requirements include the use of granular access controls, multi-factor authentication (MFA), and strong encryption protocols to protect sensitive data and applications. These practices are designed to minimize the attack surface and limit lateral movement within networks.
They also ensure that no entity is trusted by default, regardless of its location within or outside the network. This stringent approach helps fortify the network and reduces the risk of potential breaches.
Regulation:
NIST Special Publication 800-207.
Regulatory Landscape in the European Union
In the European Union, Zero Trust security for financial services institutions is shaped by a range of regulations. These frameworks emphasize the need for robust cybersecurity measures, continuous monitoring, and incident response capabilities to safeguard critical financial systems.
These regulations align with Zero Trust principles, focusing on minimizing risk by enforcing strict access controls and real-time threat detection. This combined approach prizes security and reduces potential vulnerabilities in key financial systems.
DORA, in particular, mandates resilience in the face of cyber threats, while NIS2 strengthens cybersecurity requirements across the broader financial sector. PSR1 and PSD3 are expected to enhance security in open banking, promoting stricter identity verification, multi-factor authentication (MFA), and encryption to protect sensitive financial data.
Regulations:
Regulations in Australia and New Zealand
Australia and New Zealand prioritize a proactive, risk-based approach to cybersecurity, echoing key Zero Trust concepts like the continuous validation of access and minimizing implicit trust within networks. This security model takes into account the innate uncertainty in defenses and demands constant vigilance and validation.
Australia’s Prudential Standard CPS 234 mandates strict cybersecurity measures, requiring financial institutions to ensure the resilience of their information assets. It also encourages the enforcement of robust security controls, including continuous monitoring and incident response.
In alignment with Zero Trust principles, institutions must adopt stringent access controls, multi-factor authentication (MFA), and encryption to safeguard sensitive data. In New Zealand, the Privacy Act emphasizes protecting personal data, reinforcing the need for strong identity verification and secure data management.
Regulations:
Regulations in the Asia-Pacific Region
In the ASEAN region, financial services institutions are increasingly adopting Zero Trust security models to comply with evolving cybersecurity regulations. These frameworks emphasize the need for robust risk management, continuous monitoring, and the protection of critical financial systems against cyber threats.
Zero Trust principles are reflected in the requirements for strong authentication methods like multi-factor authentication (MFA), encryption, and granular access controls to protect sensitive data. These methodologies form the basis of stringent determinants for data and resource access, reducing potential vulnerabilities.
Best practices also include regular risk assessments, incident response planning, and the adoption of secure APIs for open banking. As cybersecurity threats grow, these regulations align with Zero Trust by promoting a proactive, risk-based approach to network security and access management across the region. Efforts like these are critical in ensuring the secure operation of critical financial infrastructure in the face of growing global cyber threats.
Regulations:
Regulations in the Middle East Region
In the Middle East, financial services institutions are increasingly implementing Zero Trust security measures in response to regulatory frameworks. These regulations emphasize stringent data protection, continuous monitoring, and proactive threat detection to safeguard critical financial infrastructure.
Zero Trust principles are reflected in the requirements for multi-factor authentication (MFA), strong encryption, and strict access controls to mitigate unauthorized access to sensitive data. These measures help ensure that only validated entities can access specific resources, thus reducing the risk of potential breaches.
Best practices also involve regular security assessments, real-time threat detection, and incident response capabilities to ensure resilience against cyberattacks. These frameworks align with Zero Trust by promoting a “never trust, always verify” approach to access management and data protection in the region’s financial sector. This stance underscores the need for continuous validation and minimal implicit trust within networks.
Regulations: