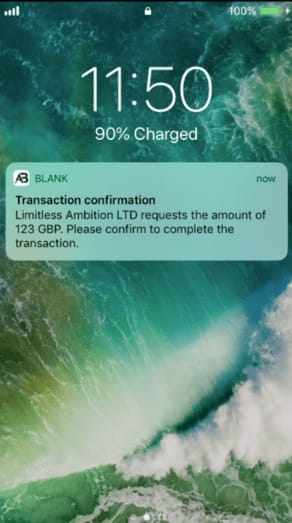
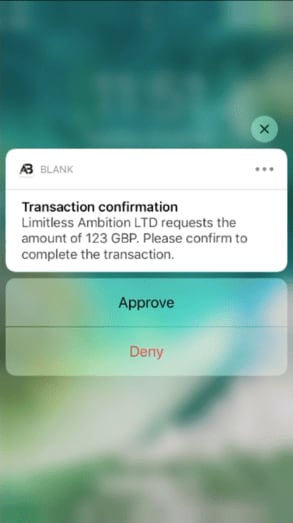
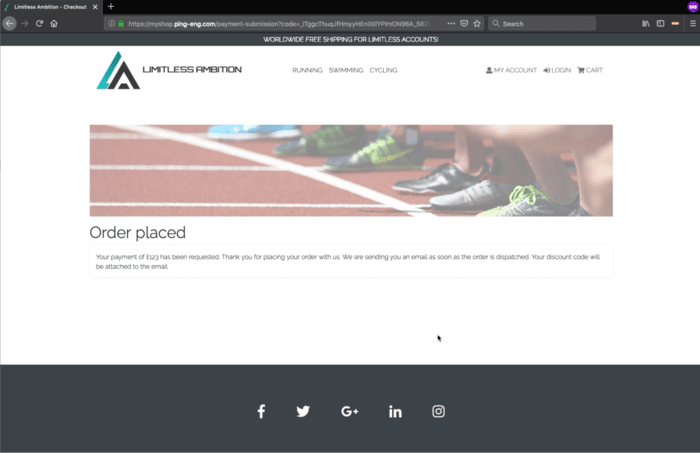
More than ever, today’s consumers expect an elegant experience when interacting with your business, especially when those exchanges take place in the digital space. These expectations are only increasing as consumers transact in the Open Banking world. From mobile banking to online purchasing to the use of third-party financial data aggregators, your customers expect control over how and when they share their personal financial data. They desire the controls to release their data, to whom, and to manage which third parties have access to their data over the lifetime of their relationship with them.
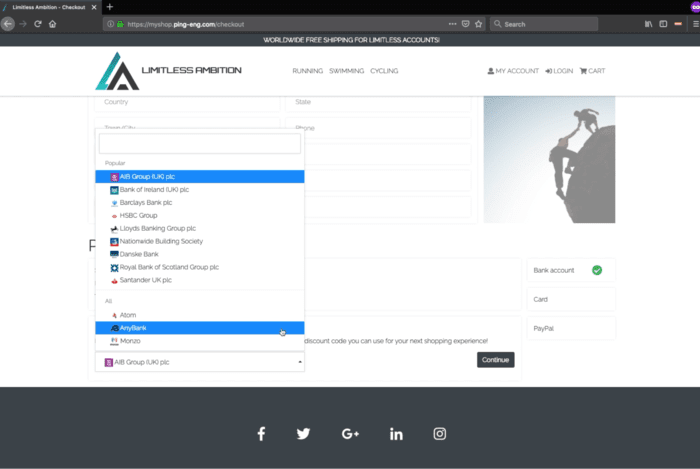
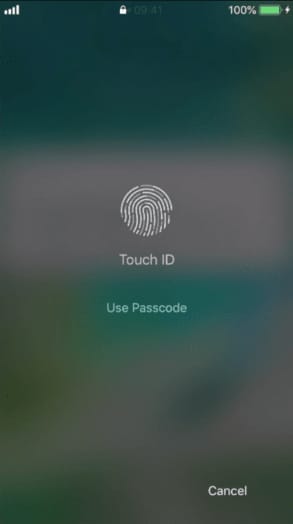
For enterprises that want to improve the end-user experience during authentication and authorization, a new technical specification is designed to help you do exactly that. Client Initiated Backchannel Authentication (CIBA) is an extension to OpenID Connect, the open federated identity standard for single sign-on (SSO) that enables seamless access to SaaS, mobile, cloud and enterprise applications. Of particular importance to financial services enterprises and financial technology companies but holding the promise of innovation across multiple industries, CIBA is gaining steam worldwide—and Ping Identity now supports this important extension.