What is a Fraudulent Device?
Broadly defined, a fraudulent device is any IoT (internet of things) device that is used to carry out illegal activities. Cybercriminals create them by bypassing the native security features on devices, allowing them to use these devices maliciously. Fraudulent devices can be created in several different ways:
Jailbreaking: This is where software restrictions on an Apple device running iOS are removed, allowing the user to modify the OS, install non-approved apps, and gain admin-level privileges. In a jailbreak, kernel patches are used to permit root access, allowing the installation of software not available through the app store. This creates security issues because much of the built-in security is lost, including verified app security. Thus, the device can be used maliciously by the owner or hackers.
Rooting or cracking: This is similar to gaining admin privileges through jailbreaking, but it is specific to Android devices. Many Android device manufacturers permit users to unlock their devices and to add apps that are not officially approved. This less robust security can lead to malicious use of a device, which is one reason why the majority of devices used for fraud are Android devices.
Tampering: Bad actors may also tamper with a device’s software (e.g., via malware) or hardware if they have physical access. One example of device tampering is skimming, where cybercriminals add a device to a credit card reader in order to “skim” or steal credit card information when cards are swiped during a transaction.
Flashing: This is the act of replacing the OS and resetting a device to factory settings, creating a new device identifier, and sidestepping attempts to detect, via device fingerprinting, that too many accounts are associated with a device.
Fraudulent devices that fall into any of the above categories can be detected in a variety of ways, including looking for telltale code, file permissions, and APIs.
However, the most common fraudulent devices are created using emulators, which are much more difficult to detect.
What are device emulators?
Emulators allow a user to virtually clone or emulate a different type of device. Using emulators, a large number of virtual devices can be created, often by cloning the same device over and over. This eliminates the need to purchase and set up a variety of different devices with different OSs. Emulators can be used to spoof or clone devices, essentially creating many virtual devices.
Used legally, emulators are useful tools developers use to test apps on different devices and OSs without purchasing every possible device and OS combination. They can create virtual versions of every iPhone or Android phone and test how an app runs on each to detect bugs and other programming problems.
Gamers also use emulators to play games made for other platforms without buying multiple systems. For example, an emulator can allow a PC to play games created for Playstation or Xbox.
Unfortunately, emulators are also used by cybercriminals for illicit activities.
Why are fraudulent devices a threat?
Bad actors also use device emulators to run on computers, on servers, or within web browsers to create fraudulent virtual devices. They then use those devices to act like legitimate users to carry out various fraudulent activities. With more than six billion people worldwide (including 85% of Americans) using smartphones, mobile e-commerce spending is at an all-time high. Accordingly, fraudulent activity is growing.
Here are just a few reasons why fraudulent devices are such a big threat.
Detection avoidance
Hackers adapt and evolve their approaches to avoid detection and sidestep device fingerprinting, which would ordinarily raise a red flag when a high number of virtual devices have the same characteristics, are all missing the same functionality, or are from the same source. Bypassing this allows criminals to appear even more like legitimate users.
Developer-level control
Using emulators, fraudsters gain the same flexibility and efficiency as developers, allowing them to create different types of devices to carry out an attack. Having access to multiple devices and applications simultaneously, fraudsters can successfully bypass authentication and rules-based security measures to carry out attacks For example, organized crime rings set up emulator farms, feeding them hacked data collected worldwide.
With this enhanced control, criminals program virtual devices to click on ads, download apps, or create fraudulent accounts. The devices can be used for coupon fraud, social media spam attacks, account takeover efforts, and mobile payment account hacks. In late 2020, for example, emulators helped fraudsters steal millions directly from mobile banking customers’ accounts with multiple financial institutions in the U.S. and Europe in just a few days.
Availability of emulators
While online fraud used to require a certain level of technical know-how, it has become much easier for people to commit online fraud using an emulator to create fraudulent devices. Emulators are now available as web browser add-ons, and there are detailed instructions and video tutorials online describing how to use them.
Browser extension emulators are not installed on a fraudster’s computer but are hosted on remote servers. They are created in this format for ease of use, just like simple, popular browser extensions web users employ to store passwords, find coupons, or translate a webpage.
This emulators-as-a-service approach is, by extension, fraud as a service, transforming emulator attacks into systematic, large-scale efforts. Because they have become easier to use, emulators are a growing threat that is accessible to almost anyone hoping to commit fraud.
How can fraudulent devices be detected?
As always, it is important for your enterprise to be aware of all types of fraud and stay ahead of the game.
Along with staying abreast of the latest attacker techniques and emerging threats, a two-pronged approach is strongly recommended to protect your business and its customers from fraudulent devices:
Data enrichment: merging multiple sources of device intelligence
Behavioral biometrics: using both internal and external data to improve fraudulent device detection
Data enrichment
Cybercriminals attempt to imitate legitimate devices in a variety of ways, including spoofing signals to sensors and removing traces of their existence after deleting an emulated device. These tricks are sophisticated, but not foolproof.
Advanced data enrichment technology can help you differentiate between human vs. non-human users, which allows fraudulent devices to be identified by pairing device attributes with behavioral data. This makes identifying whether a device has been tampered with or spoofed more straightforward. This is because emulators leave a footprint on the OS and have incomplete critical behavioral data, such as mobile attributes missing accelerator or gyroscope data. These are automatic red flags that can be easily identified.
Behavioral biometrics
These markers work in tandem with behavioral biometrics to identify emulated devices. Behavioral biometrics use machine learning to develop expectations of how humans interact with devices and what those patterns look like. Using sensors embedded in mobile devices from touch screens to GPS radios, behavioral biometrics extract and analyze hundreds of data points that define exactly how people use their devices. Algorithms then examine each device seeking access to user systems or apps to determine whether each device’s data points reflect the properties of a physical or an emulated mobile device.
These biometric tools examine device parameters, including how firmly users touch the screen, how fast users tap and swipe, how users move their wrist and palm when touching the screen, and more. A single swipe on a touchscreen provides the position and pressure of the user's finger and the intensity of vibrations created by the accelerometer in response to the action.
Although these interactions generate hundreds of data points, the human patterns they reveal are consistent across different interactions. The amount of pressure applied when swiping varies from person to person, and this pressure is consistently unique to each individual. In other words, it is rare for any two individuals to have the exact same swiping behavior.
On the other hand, it is not unusual for emulated fraudulent devices to have the same programmed parameters for virtual swiping and other actions across all virtual devices a fraudster creates. Doing things this way is much simpler for the fraudster than programming unique values for every variable, which would be much more time-consuming.
Another biometric data point is the orientation of a user’s phone when swiping. When moving their finger across the screen, a user usually tilts the device toward themselves. The angle and direction of this tilt varies for each person, but the uniqueness of this behavior to each individual user is consistent.
These dozens of behaviors amount to a collection of nuances that cannot be easily simulated. Examining this behavioral data differentiates a real user from a fraudster and makes committing fraud more difficult.
Conclusion
Unfortunately, emulators are commonplace. Recent developments have led them to be used more often as mobile device fraud continues to grow and evolve worldwide.
Traditional fraud detection tools struggle to detect emulated devices, which means a site likely has emulated traffic interspersed with genuine traffic from real devices. However, emulators are vulnerable for the same reasons they are powerful: since they are not physical devices, they cannot easily provide all of the unique attributes of a physical device.
Using a powerful two-pronged approach built on data enrichment and behavioral biometrics creates hard-to-spoof data points and parameters. This makes it exceptionally difficult for emulated devices to pass for physical devices without relying on specific footprints or classical detection methods. Thus, biometric tools are effective against even the most advanced emulation software.
Learn more about thwarting emulators and fraudulent devices
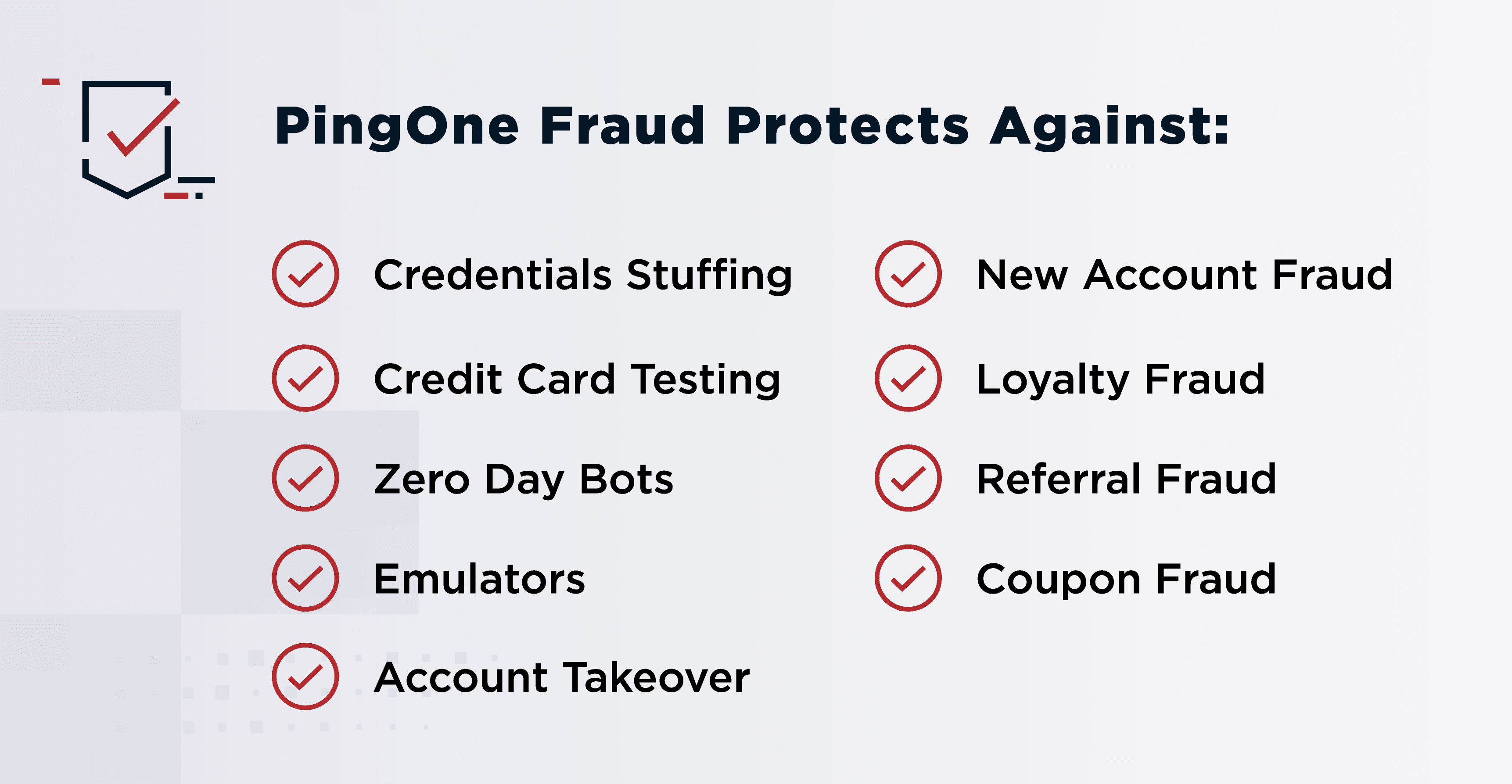
PingOne Protect detects a wide variety of fraud using behavioral navigation, behavioral biometrics, device attributes, network attributes, and more to help you protect critical infrastructure by detecting fraudulent activities without impacting the user experience.
Related Resources:
Start Today
Contact Sales
See how Ping can help you deliver secure employee, partner, and customer experiences in a rapidly evolving digital world.