The Evolution of Identity Systems
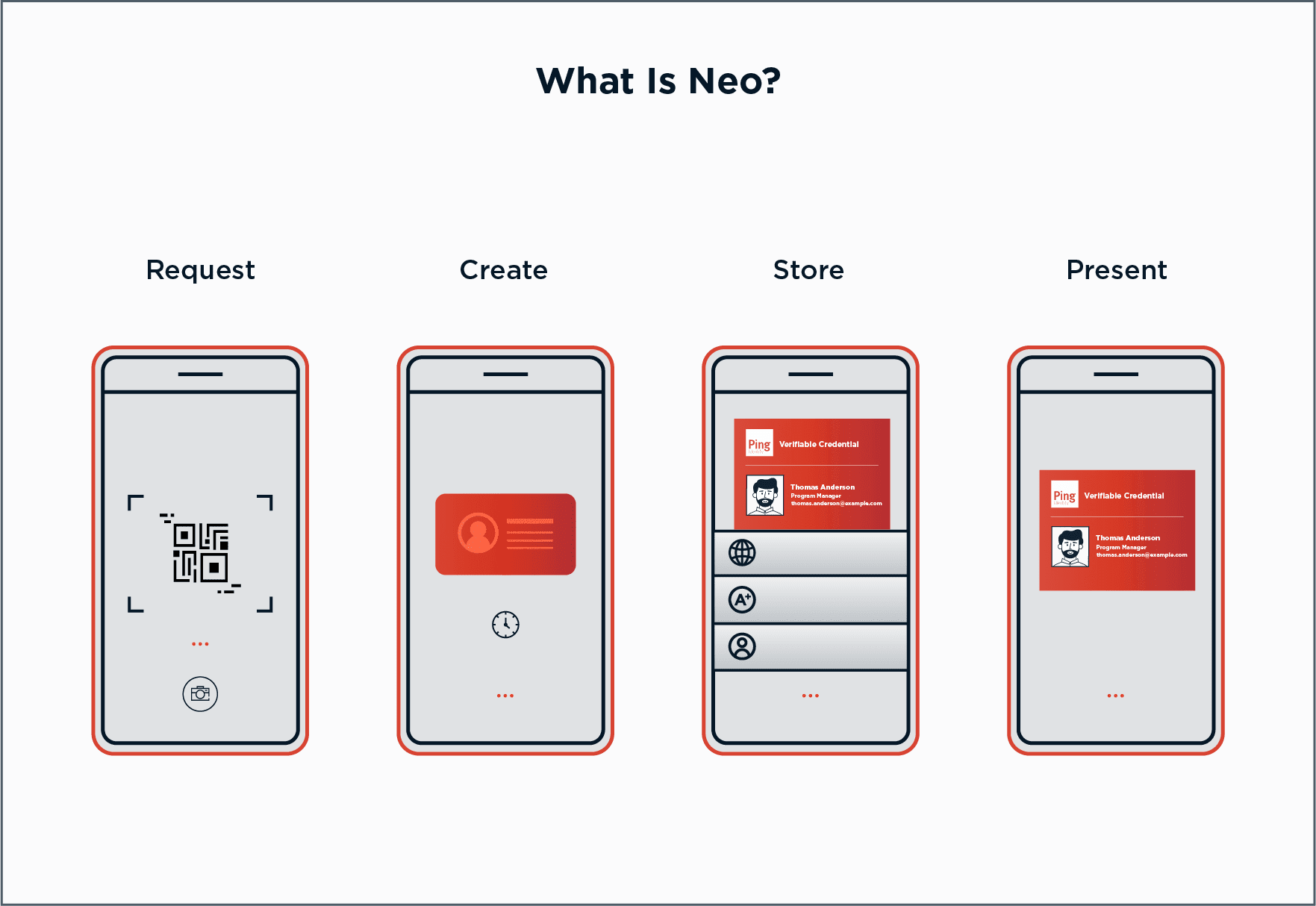
Neo means “a new and different form of something that existed in the past” and PingOne Neo reimagines today’s centralized IAM systems. Traditional centralized IAM systems store personal information, and are controlled by a single entity. Decentralized identity allows identity information to be securely stored and controlled by the owner.