While the work from anywhere (WFA) movement has taken on new significance over the past year, the trend has been gaining momentum for quite some time. As the distributed enterprise, the use of personal devices and the expectation of remote access to resources have become the norm, the workplace is no longer confined to a physical location. This is dramatically changing the world of work for both the enterprise and employees.
Business applications like Slack, Zoom and Salesforce are enabling greater workforce mobility, making it easier than ever for your employees to be productive from anywhere—whether they’re working from home, on the road or from an Airbnb rental. At the same time, though, this newfound freedom presents unique challenges when it comes to keeping those same employees safe and ensuring data and resources remain secure.
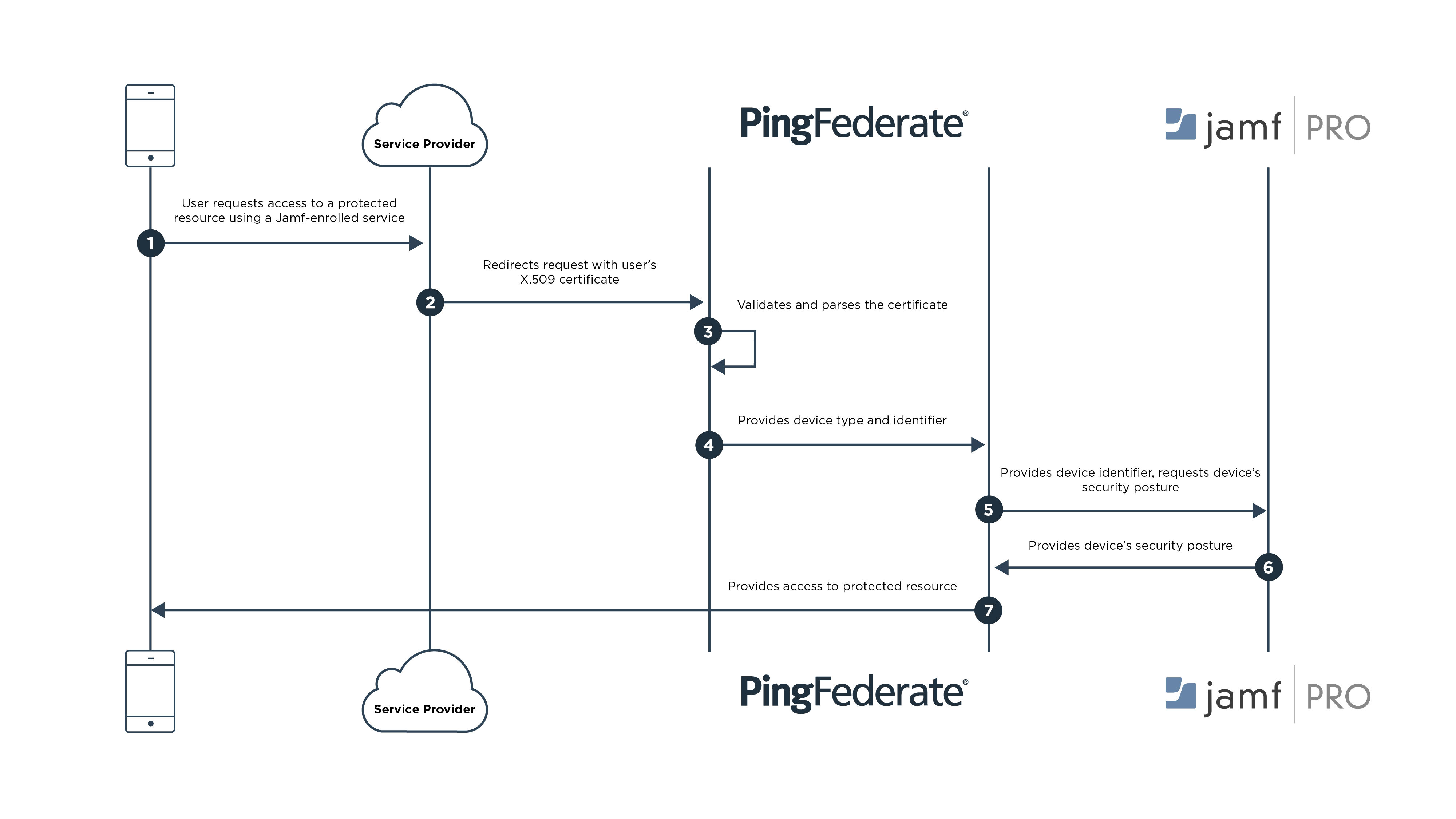
As the once-trusty perimeter crumbled, identity and access management (IAM) emerged as the backbone of a strong security posture. Identity provides the sturdy yet flexible infrastructure needed to secure the modern distributed enterprise, providing capabilities like single sign-on (SSO) and multi-factor authentication (MFA). But to support and secure an increasingly free-range workforce, IAM must expand and extend to your employees’ personal devices. This can be achieved through integration of IAM with mobile device management (MDM) platforms.