Personal identity, decentralized identity or self-sovereign identity gives individuals the control to manage and share their own identity information.
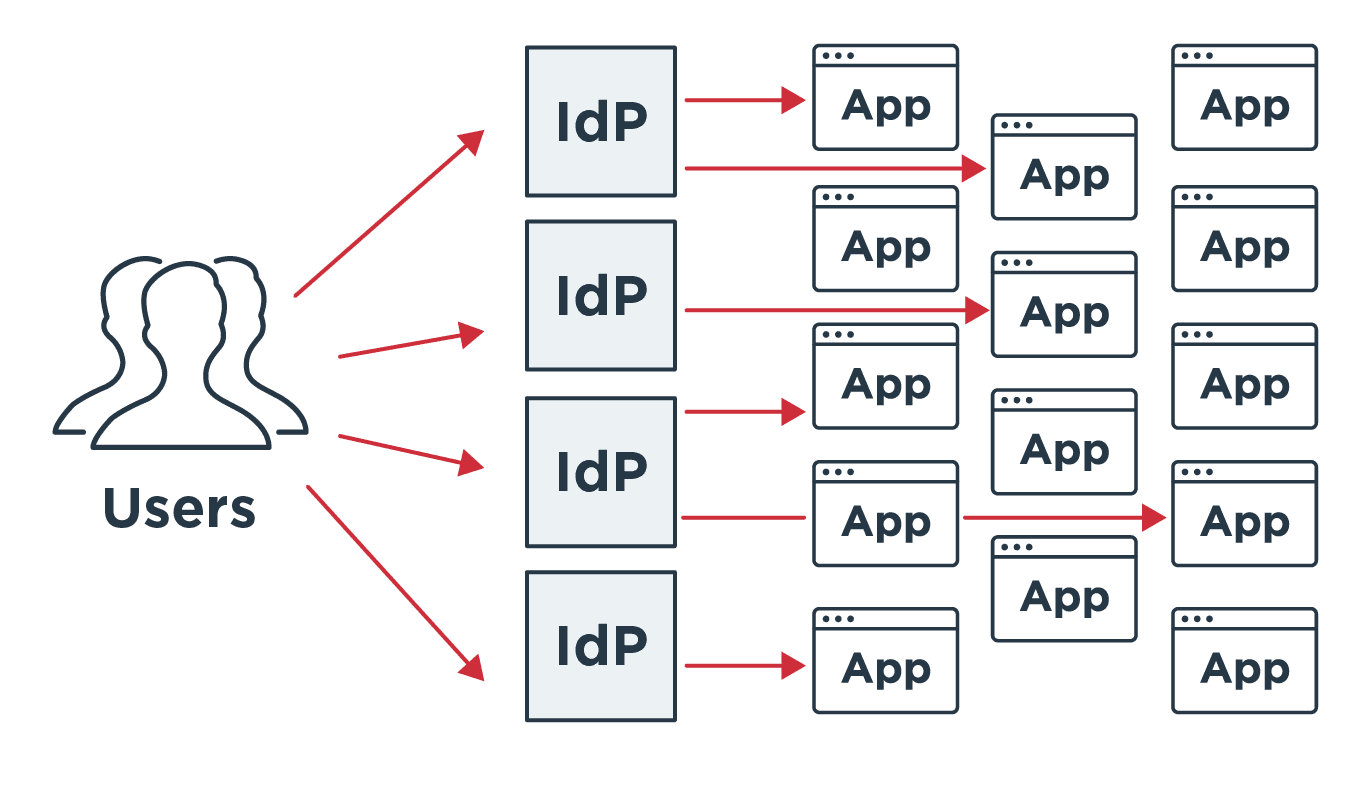
It moves us away from the current model of identity management, where individual organizations store identity information for each user. Sagar explains, “One drawback to the current approach is privacy. You have to trust multiple businesses to manage and protect your identity. Then there’s the usability and maintenance of all these different identity providers (IdPs) that you connect to.”
The current model puts the onus on users to remember what information they’ve shared with which organization to enter proper credentials. So as more happens online, users’ personal data is collected and stored in more places. Meanwhile, demands on organizations that collect data are growing, in the form of privacy regulations and necessary protections against data breaches and fraud.
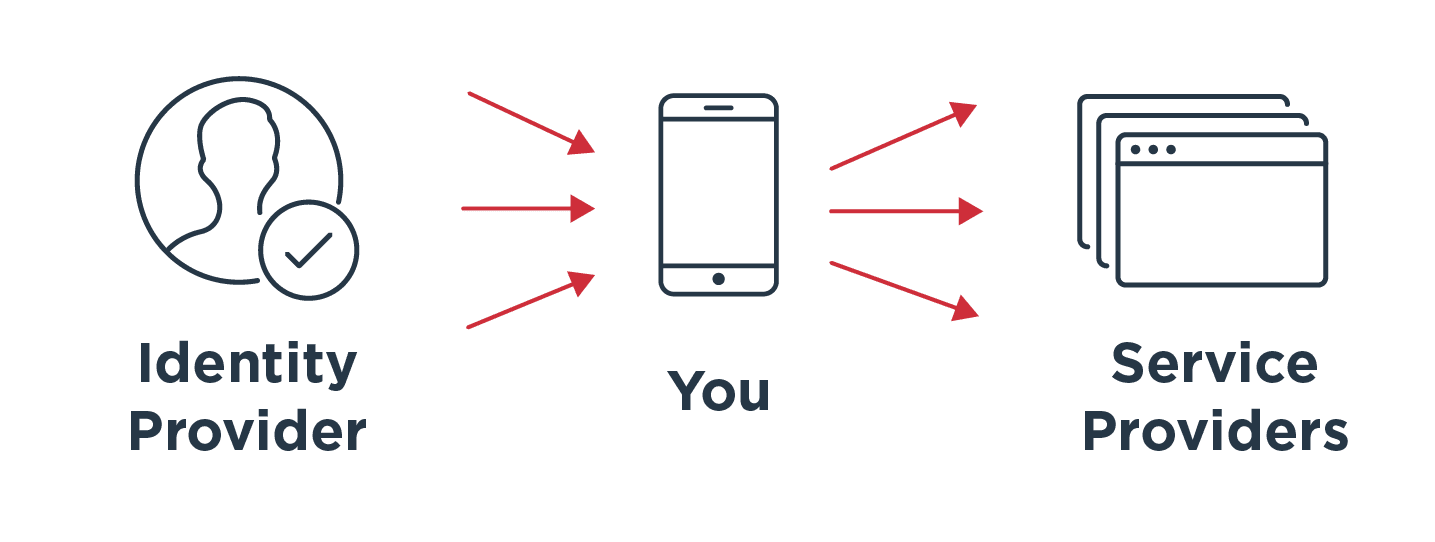
Sagar is excited as a technologist about where personal identity is headed. “It’s a fundamental shift. We are used to organizations holding our identity data—Google, Facebook, etc.—and everyone needs your identity before they give you access. If you have 1,000 identity providers and 1,000 service providers, that’s 1000 x 1000 connections to maintain and manage. It’s not scalable. Making your phone an identity provider, essentially, is an exciting space as we move to where you are your own identity provider. You control your attributes and with who, when and where you share those.”
Sagar continued, “With your phone or something in your phone acting as a wallet storing a verifiable record of yourself it becomes much easier. The consumer is in control without having a backend connection to maintain. It doesn’t negate the problem where they lose control of how a third party uses their identity data once it’s out, even when they’ve consented. It doesn’t solve all the problems.”
A Sign of the Shift: The European Digital Identity framework
One of the biggest signs of a shift toward personal identity is the European Commission’s (EC’s) European Digital Identity (EDI) framework. It proposes an EU-wide framework enabling individuals and organizations to link national digital identities with drivers licenses or other forms of identification.
“If successful, we’ll see a push from the European community,” Carbone predicted. “Regulators are also exploring wallets and personal identity. We’ll likely see a push around personal identity and identity wallets across Europe.”
Europeans will then be able to identify themselves or provide confirmation of certain personal information to use offline or online services across the EU. An individual’s identity will reside in a digital wallet on a mobile device or laptop. It might integrate e-signatures, electronic timestamps and electronic registered delivery services. The EDI will eliminate revealing personal information not relevant to any specific task or transaction, such as opening a bank account, filing taxes, proving age, renting a car or checking into a hotel.
The biggest hurdle for adoption, said Sagar, is education. “I don’t think the average person knows how and where identity is stored. They have a login, they know their username and password. It will be a fundamental shift in thinking to see the benefits and embrace your phone or your e-wallet as your main ID source. The cultural shift will be the biggest hurdle. As Federico mentioned, there are countries where they tend to be skeptical of new tech. It will take longer in those places to adopt a new way of identifying yourself.”
Despite the challenges, individuals and organizations will reap significant benefits. The EC hopes to have agreed on a toolbox to implement the EDI framework by September 2022. The toolbox will be published in October 2022, then pilot projects will test the technical framework.
The next priority is how to monetize implementing and using this approach. It has support. Individuals have begun to embrace it. But businesses need to buy in, plan, design and implement the infrastructure and provide and promote it to users.
“Organizations need to be able to monetize this,” Carbone observed. “Organizations must always invest. Unless they can monetize this, we won’t see a big push. We see trends start and grow because there’s money to be made. If there’s no money to be made or saved, organizations won’t push for it.”
Sagar agreed. “Much of it will be covered by regulation. Some countries—Denmark, Sweden—already have some version of this. Driver's licenses are stored in your wallet. Much of the activity is in government services. It may become an EU regulation, but it must be driven by policy. It’s early and an exciting emerging trend and I hope it will catch on.”