Safeguard Your Organization
When it comes to selecting a single sign-on solution for your organization, not all solutions are created equal. Choosing the best workforce SSO solution depends on your IT environment and user base.
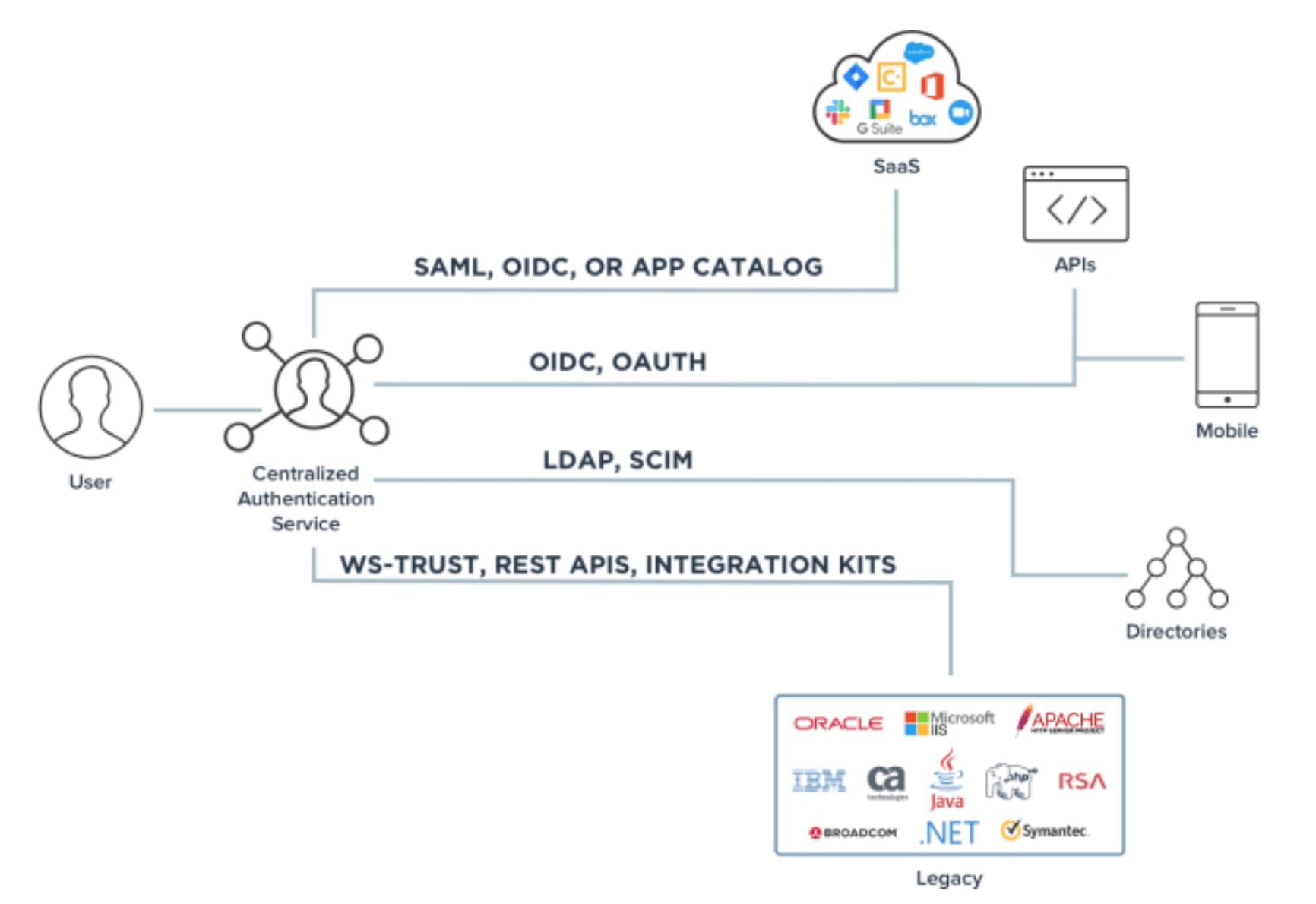
Some SSO solutions control authentication for users accessing resources from desktops in a single security domain. Others provide universal SSO across complex hybrid environments that include legacy on-premises, cloud-based and software-as-a-service (SaaS) applications. SSO solutions can act as an authentication authority. They can be used for many identity types and use cases, from cloud to on-premises.
IBM’s Cost of a Data Breach Report 2021 found that data breach costs rose from $3.86 million to $4.24 million, an increase of 10% from the prior year. Compromised credentials were the most common initial attack vector and responsible for 20% of breaches, at an average breach cost of $4.37 million.
According to Accenture’s 2021 Cyber Threat Intelligence Report, data migration to the cloud and the advance of internet-connected devices, such as Internet of Things (IoT) objects, switches and routers control data flowing in and out of the organization, increase the risk of cyberattacks. The report also highlights that in multiple ransomware attacks in 2020, data was destroyed rather than encrypted.
We'll explain the fundamentals of single sign-on (SSO) and provide criteria to help you choose the best SSO solution for your business.