Key Takeaways
- Facial biometrics verify the real user, not just a device: They provide stronger protection against fraud and AI-driven identity threats than other passwordless methods.
- Identity assurance sets passwordless methods apart: Biometrics create a trusted link between a user and their digital identity, unlike OTPs or passkeys.
- Decentralized biometrics balance security, privacy, and UX: Zero-knowledge approaches enable scalable, secure authentication across devices and platforms.
Authentication comes down to one simple question: is this person really who they say they are?
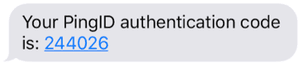
As password use continues to decline, passwordless methods, such as SMS OTPs and passkeys to call center verification and facial biometrics, are replacing them. But not all passwordless approaches deliver the same level of security, privacy, or user experience (UX).
According to Ping Identity’s Global Consumer Survey, biometric authentication ranked as the top feature globally that would increase trust in organizations, underscoring the importance of utilizing this capability to achieve verified trust in an era dominated by AI-driven threats.
Let’s take a look at high-assurance environments where identity assurance truly matters—consumer sectors like banking, fintech, insurance, and gaming, as well as workforce settings such as heavy industry, retail, food production, and organizations with numerous third-party identities spread across multiple partner/B2B relationships. In these environments, proving identity across every digital interaction is critical.