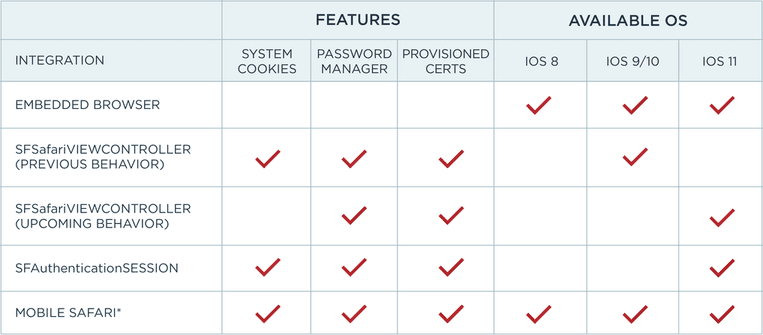
Hey Identity Architects, are you aware of the changes coming in Apple's new versions of iOS and macOS? These changes take effect in autumn of 2017 and may affect single sign-on (SSO) user experience in your organization.
The current beta releases of Safari have been enhanced to reduce collusive cross-domain tracking of users. This is being accomplished through additional restrictions on the browser state mechanisms--particularly cookies and the HTML5 local storage mechanisms. Those very mechanisms are relied upon by most organizations to achieve single sign-on.
Single sign-on (SSO), specifically the ability to authenticate once and have that authentication applied to multiple web/mobile applications without requiring additional authentication challenges to the user, is also technically a cross-domain tracking system--just one which the user gets significant value from.
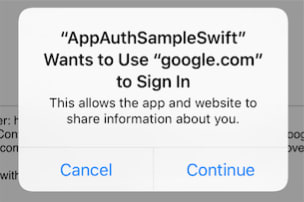
In this article, we'll cover these upcoming changes to Safari and its related services, and specifically how native applications are impacted.