Everything you need to know about Federal ICAM
Just over a year ago, it would have been hard to imagine the transformation that the world’s workforce has gone through essentially overnight. Now, it’s clear that telework supported by the cloud is here to stay.
For organizations of all kinds, this requires the quick introduction of long-term digital transformation initiatives to properly secure your employees and sensitive assets, whether they’re located on premises or in the cloud. But these initiatives will only be successful if you reexamine the capabilities they’re built upon and enhance them wherever possible, as soon as possible.
government framework.
It's been really fascinating to see.
What I can only call a once-in-a-lifetime change in the government's expectations for Private and public partnership as it relates to its own digital transformation and the need For them to elevate their own technology capabilities into the 21st century, It's really fascinating how much identity is now a part of that conversation and what's even More interesting is the reality that for a long time the government has focused on.
Making identifying information, like your Social Security number, The same as your authentication, right?
If you have a Social Security number and you're able to produce it, that you are who you say you are, And we know that that's not accurate, right?
And so it's really interesting to see the US Government talking about their own digital Transformation with Identity as the Core.
Of that activity and using the language of a great identity control framework, Those of us that have managed identity for large parts of our careers using language like Authentication, approval, authorization.
And saying we need to build modern technologies into our citizen processes so that we can Authenticate, you know, that you are who you say you are for the first time hearing about Things like two-factor authentication and multi-factor authentication being used for US Government services is really amazing because that is a huge shift from where we were just Even a couple of years ago and to have those conversations at a level of our own US Government departments and agencies saying.
Hey, we can't do this ourselves.
We spent, you know, 50, 60, 80 years building everything ourselves.
We can't do that anymore.
We need public-private partnership.
It's really going to create a very, very interesting future for American citizens and American consumers that I don't think any of us thought would be possible in our Lifetimes, but now it's being recognized again that identity is the core of everything.
And one of the critical requirements for the government, any government, But in, in the US in particular, a critical requirement for the US government is to protect Its citizens, which we've done for centuries in the analog.
We have not protected our citizens in the digital realm in the United States, And now there's becoming a recognition that the, the analog and digital self is still a citizen.
And the digital self needs to be protected just like the analog self, Because that's the obligation of a strong and a strong and successful government.
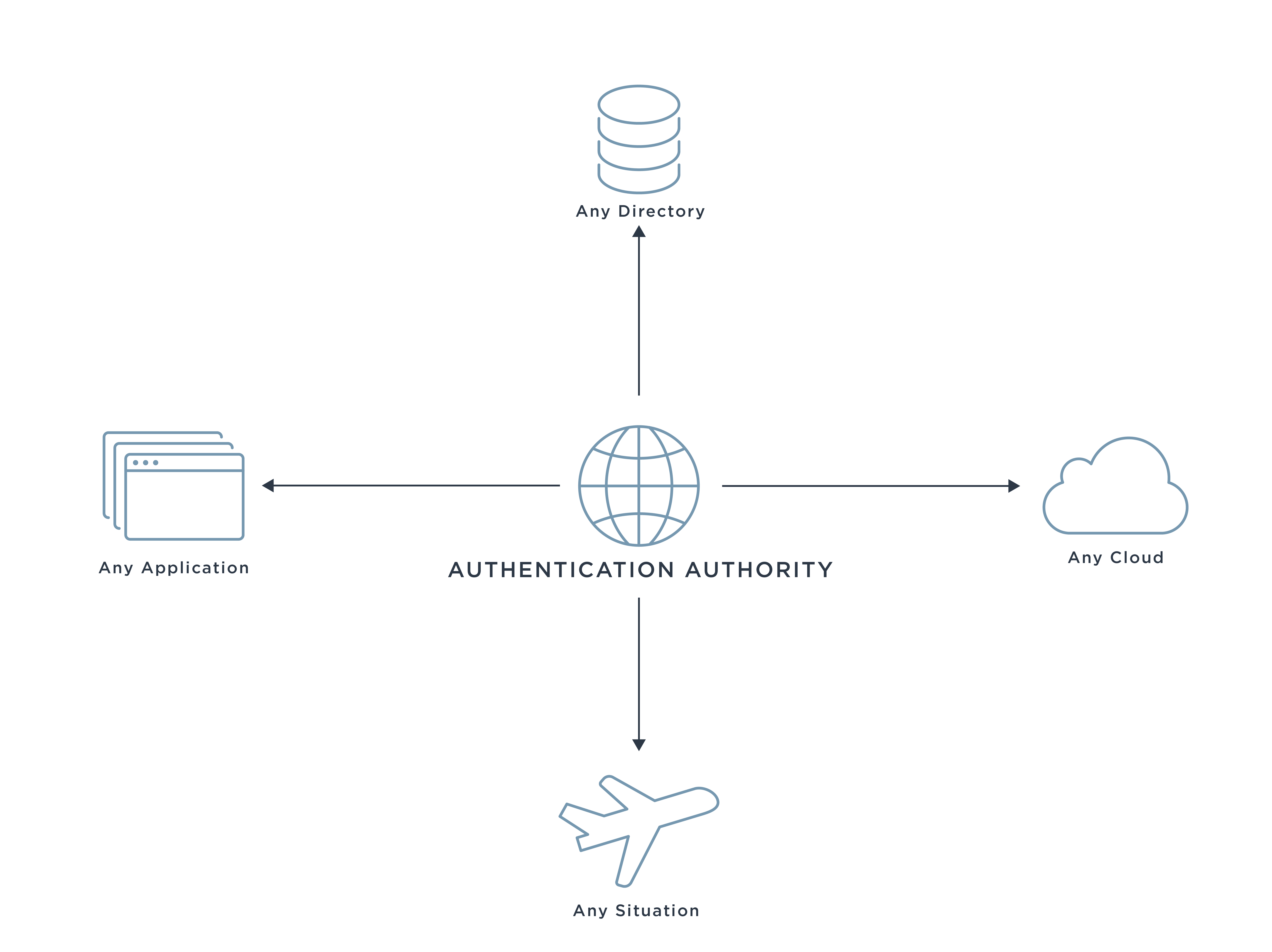
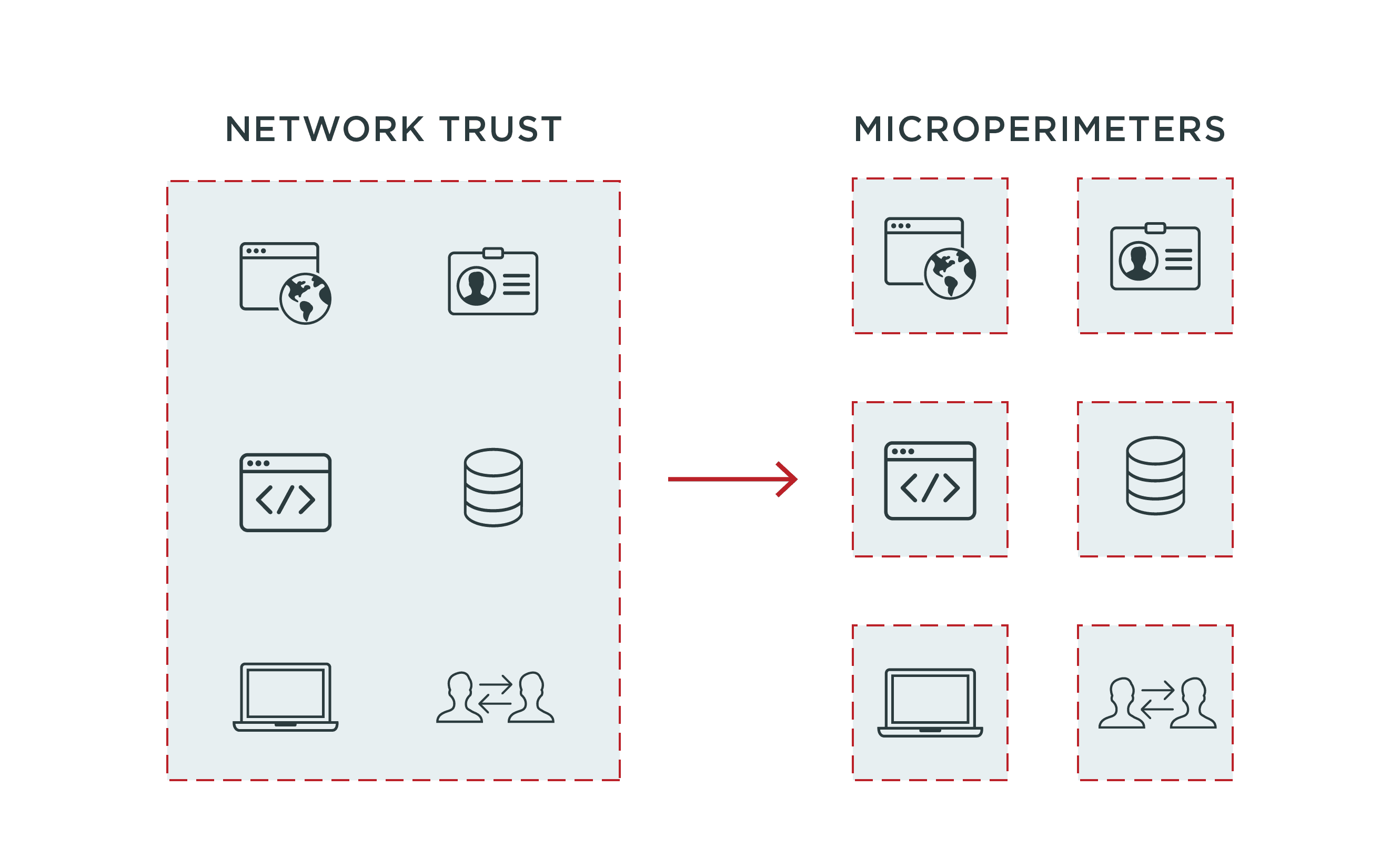
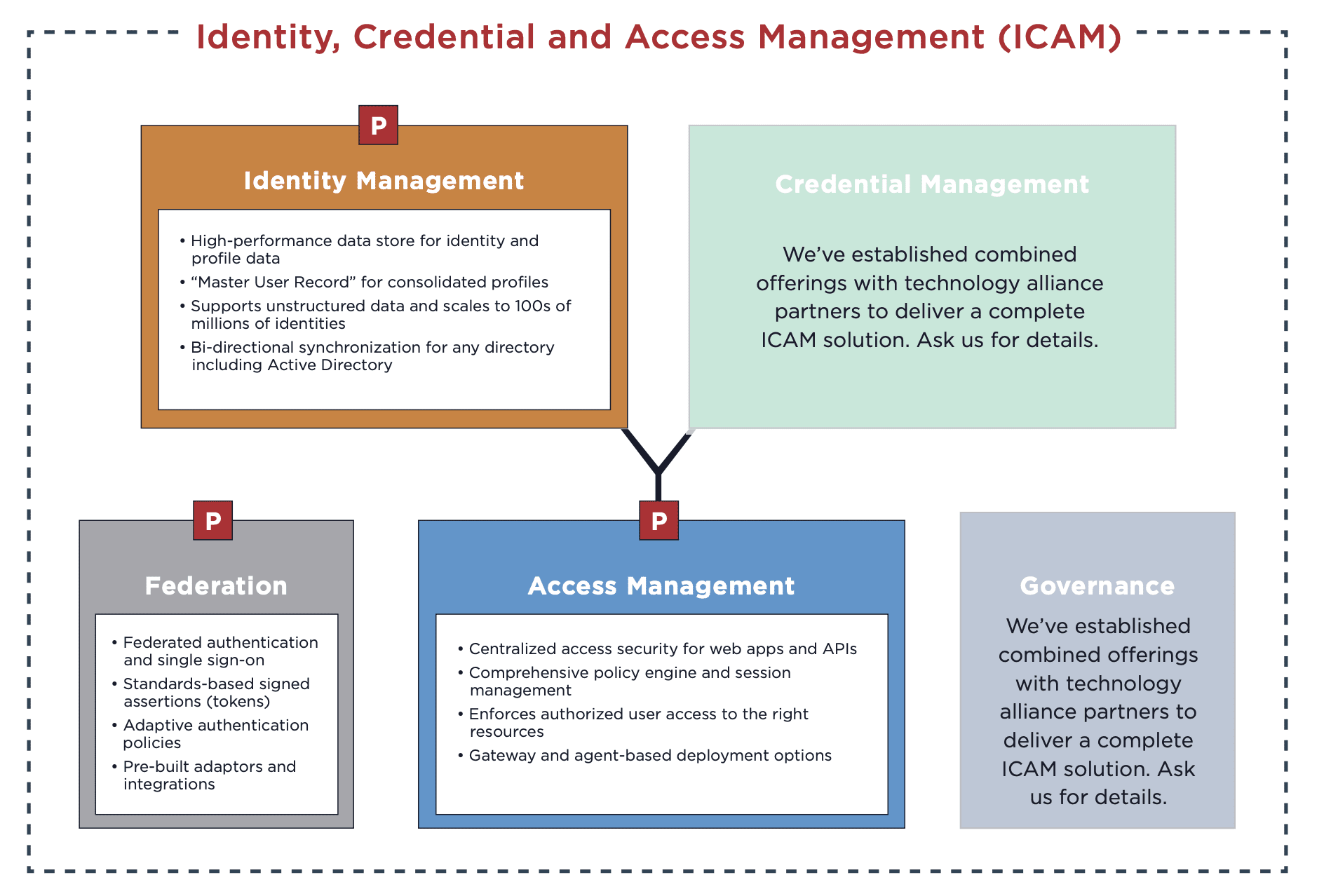
For federal government agencies, this specifically means reviewing your Federal Identity, Credential, and Access Management (ICAM) architectures. You’ll need to identify areas where you can uplevel your existing ICAM capabilities in accordance with the latest standards and policies, including the May 12, 2021 Executive Order on Improving the Nation’s Cybersecurity which mandates the adoption of Zero Trust architecture.
So what exactly is Federal ICAM (FICAM), and how can it accelerate other critical digital transformation initiatives? Let’s find out.