Identity and access management (IAM) is no longer just a behind-the-scenes function. It’s the foundation of digital trust for modern enterprises. As organizations look to balance stronger security with frictionless experiences, Ping continues to lead the way forward.
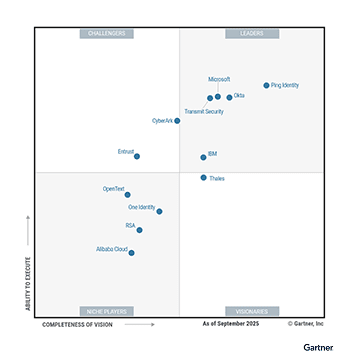
We’re proud to share that Ping Identity has been named a Leader in the 2025 Gartner® Magic Quadrant™ for Access Management for the ninth consecutive year, positioned highest in Ability to Execute and furthest in Completeness of Vision (for the second year in a row).
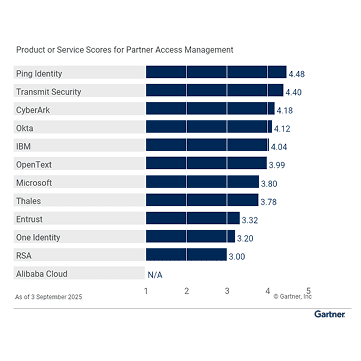
Ping also scored highest across three use cases—Workforce Access Management, Partner Access Management, and Machine Access Management—in the 2025 Gartner® Critical Capabilities for Access Management.
This milestone reflects our commitment to innovation – working with our customers to deliver secure and frictionless digital experiences."
Andre Durand
Chief Executive Officer