The healthcare world has been going digital for a while and new federal government regulations tied to the 21st Century Cures Act are accelerating that trend. As the Centers for Medicare and Medicaid Services (CMS) predicted, the industry has also seen explosive growth of healthcare apps addressing use cases built on top of public APIs. The CMS Patient Access final rule, as well as the Office of the National Coordinator for Health IT (ONC) Information Blocking rule, now impose deadlines for most healthcare organizations to allow patients to access and share their electronic health information (EHI) via APIs. These new regulations are being enforced starting in 2021.
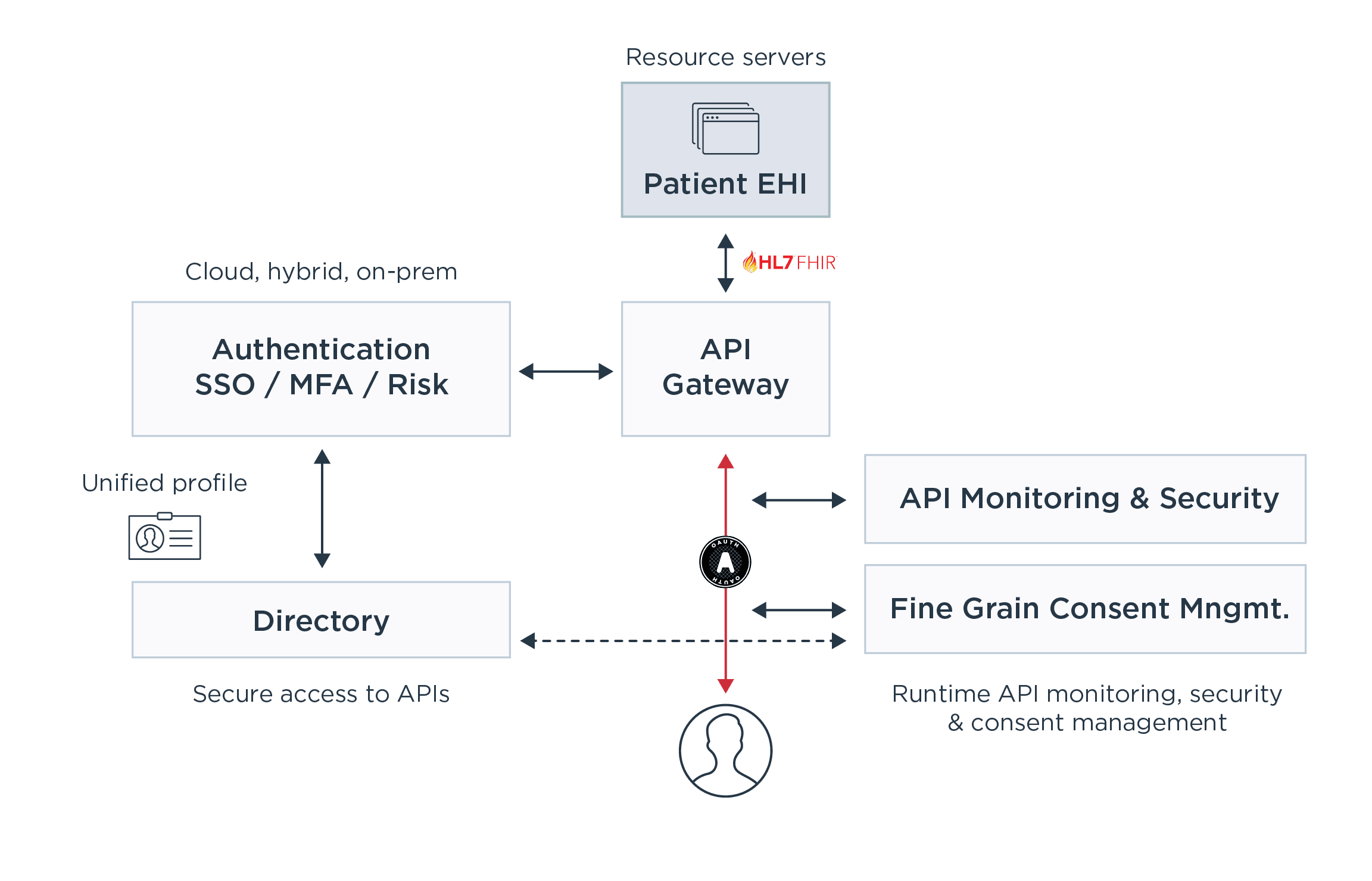
Both the CMS and ONC rules require health organizations to make use of the Fast Healthcare Interoperability Resources (FHIR) API, developed by the non-profit Health Level Seven International (HL7), to implement “interoperability” of health information. In addition, implementers must use the FHIR complementary security and app registration protocols, specifically the SMART Application Launch Implementation Guide (“SMART IG”) 1.0.0, which is a profile of the OAuth 2.0 specification, and the OpenID Connect Core 1.0 standard.
An organization implementing a Patient Access API must also make documentation regarding the API functionality and operation publicly accessible by posting it directly on their website or via publicly accessible hyperlink(s). The documentation must include at a minimum the API syntax, function names, required and optional parameters and their data types, return variables and their types/structures, exceptions and exception-handling methods, software components and the configurations an app must use to successfully interact with the API, and more.
In summary, health information must be accessible via an API, the API implementation must be documented, and that documentation must be made publicly accessible. The API provides access to highly sensitive health information that must be kept confidential and secure under federal and state privacy and security rules, including HIPAA, meaning that health organizations will face steep penalties if that data is breached. Given the high value that stolen health data commands, one can only anticipate that cybercriminals will look to target these new APIs to breach health organizations and steal patient data.