PingOne for Customers Roles has four roles. I’ve included the highlights for each role below, and while these aren’t the only abilities associated with each role, they typically help you determine which role or roles should be assigned to an individual.
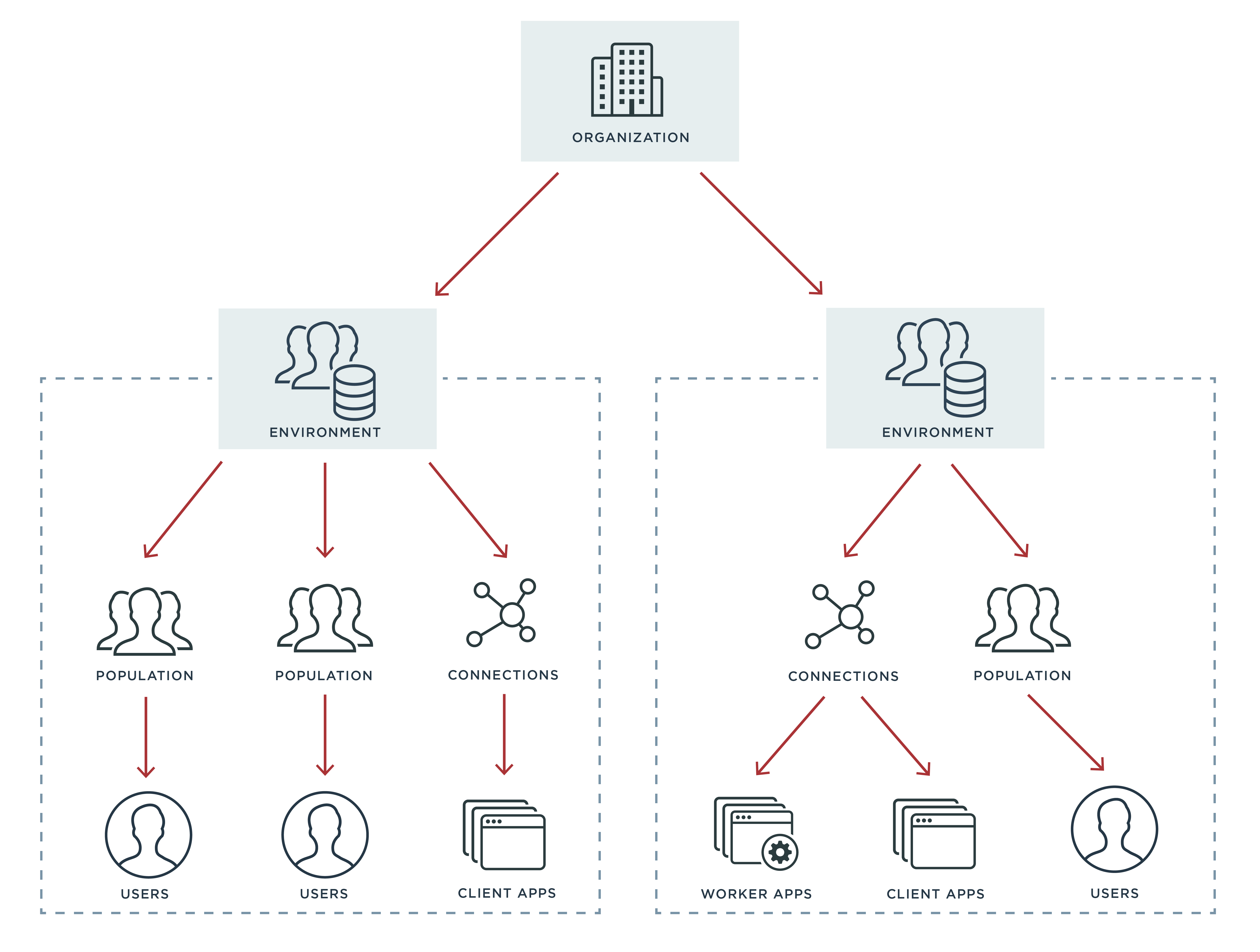
The Organization Admin. This powerful role oversees the entire organization, and its main ability is having access to organization resources. A user with this role can read and update licenses, for example, or they can also create, delete and update environments.
The Environment Admin. The environment admin oversees one or more environments. While not as powerful as the organization admin, the environment admin exerts control over resources at the environment level, such as populations, password policies, notifications and emails, branding and app role assignments.
The Identity Data Admin. This role bestows the ability to create, modify and verify users. Key actions revolve around passwords, such as reading a user’s password state or setting, recovering, validating, resetting or unlocking a user’s password.
The Client Application Developer. Last but not least, the client application developer can manage an application’s settings. This role can retrieve or reset an app secret, as well as create and modify resources.
One important thing to keep in mind when assigning roles is that they are not boundless; roles can be scoped to certain components in order to restrict access only to the components needed. For example, if you have multiple environments in your PingOne for Customers instance, you can assign the environment admin role abilities over a single environment and not others. Or, the identity data admin may have responsibilities in some environments but not others.
What’s so Cool about Roles?
One of the great things about roles is that we at Ping did a lot of the hard work in creating a customizable permissions set. We made some logical collections to allow you to quickly assign someone a role and get them access to only the right things.
Do you have someone with a larger view of the overall company or organization? You can give them the Organization Admin role, and they’ll be able to change or upgrade licenses and promote or demote certain environments. Or, if you have someone responsible for a certain segment of your company like QA, Production Environment or North America Lead, you can allow them to take control of some kind of environment by giving them the Environment role. They’ll be able to do things like set the default password policy, create populations and give permissions to certain apps.
Going down the list, for individuals dealing with users or identities behind the scenes, you can assign them the Identity Data Admin role. They’ll be able to reset user passwords, create users and modify user attributes. And a developer working on integrating identity into their apps has their work streamlined when you give them the Client Application Developer role, which allows them to start testing out the PingOne for Customers integration into that app.
Roles are easy to apply and experiment with and there’s a list of permissions you can always reference within the admin console and in our API docs. Come try it out with a free trial of PingOne for Customers.