Hello, I am Hannah Murphy, an FT tech correspondent based out of San Francisco.
Uh, where I cover cybersecurity and social media.
And I'm delighted to be here at the Global Banking Summit, Uh, and have very knowledgeable panelists coming, uh, With me to discuss how Financial Services groups should think about combating Cyberattacks.
Uh, to get things started, we have Lauren Russin of Ping Identity.
Welcome, Lauren.
Hi, Hannah, thank you.
Hi, great to have you here.
Um, now, we're gonna chat, chat, uh, for a couple of minutes before we bring on the other Panelists.
Um, and I wanted to start, uh, by speaking a Bit about the landscape of cyber threats, uh, that the banking sector in particular faces.
Um, I was wondering if you could talk a bit about sort of the pandemic and the shift to Remote and hybrid working, as well as this, as well as this greater reliance on online banking Services.
How has this sort of changed things?
Changed the landscape of threats?
Yeah, I mean, it's a great question.
And, you know, I had a chance to talk with some of our financial customers over the course of the Pandemic, and it's been interesting how a lot of the terminology they use is what we planned To do in 5 years, we had to compress into almost 6 to 8 months.
So it's just the rapid change.
Of really securing up their infrastructure, making sure their employees and their customers Are secure.
And so just everything, you know, Essentially accelerated, you know, tenfold, and it brings up kind of an interesting quote is That, you know, over that period of time, there was a, Or it's more of a statistic: you know, 37% of the consumers that one of our banks had Prefer to do all of their online registration, all of their flows online.
And, um, you know, what that has done has really made that the primary vehicle for Communication and even Millennials are, uh upwards of about 50% of them all prefer to, To engage online.
And so you consider what that did was change The attack surface where it's, you know, all digital, all remote, As well as then, um, everything related to that, that user journey from really registration all The way through authentication and authorization.
And I wondered if there are sort of any particular threats, Um, that are emerging that are particularly worrisome.
Yeah, um, so the ones that we primarily hear from our customers are, You know, really what we call in that unknown to known state, Um, where it's fraud, that or either bot detection.
So, you know, a lot of attacks that are really, you know, Trying to either take over accounts, they're trying to Imitate, You know, that they are the user and it's really, you know, In those first days, if they can start to create a synthetic identity to where, You know, you think you know who they are, but you really don't, It's, you know, again, that, that mechanism to really, you know, Take over the account, be able to then imitate or impersonate, um, that we hear quite often.
And uh uh I, I'm hearing this phrase more and more synthetic identity.
What exactly is the attacker doing here, and how are they sort of exploiting particular Vulnerabilities in the first instance?
Yeah, so, um, you know, if you look at just the definition, I mean, It is, it's almost a contrived identity where they take, You know, attributes of an individual and start to create an account for them.
There's a lot of mechanisms that, you know, are either traditional, Even through phone calls to establish an identity, um, Based on information they may know about a user.
And then once that account is created, you know, it becomes then, um, a synthetic identity of the Individual that they're actually trying to take over.
So, um, it really is just, you know, hackers or people out there, Fraudsters, if we use that terminology, are there to establish an identity that's not real but representative of an existing account.
And, um, it is, you know, I'd say, especially in the E-commerce space, Probably 70, 80% of the attacks are really an account takeover, Um, done in a variety of ways.
And there are particular sorts of technologies that the attackers use, Um, that are that are gaining in sophistication that allow them to do this sort of thing?
Um, you know, again, we're hearing this from a lot of customers, and it really is the way that They are building bots that, um, are able to impersonate who they are.
You know, we hear everything from, you know, devices being the entry point, And they'll mask a device, they'll be able to then associate or repair a device to a user Identity.
You know, there's a lot of just brute force Attacks where they have a bit of info about someone and they'll do an account Recovery UM flow to be able to again imitate that user and take over that account.
Um, but it's, it's primarily, you know, a lot of the, The bots out there that are again gathering information and then replicating that information as if they are a user.
And sort of synthetic identities are, are one thing, but we're also hearing about a lot of Scams and sort of social engineering, um, which may be part of building that, But also sort of separately.
Can you talk a bit about the sort of scam?
Landscape, if you will?
Um, so from a scam standpoint, and that isn't really a, A preview from Ping's Identity, we don't, you know, generally look at that space, But from a, you know, just in industry in general, you know, Some of the scams are where there's, you know, leveraging some of these, You know, online account recovery mechanisms is the one that we see primarily where they will, You know, take information about a user, try it through an account takeover.
Um, you know, essentially recover a password or recover an identity and leverage that flow.
And now, sort of on the other side, could you walk me through some of the technologies out There to sort of help mitigate or tackle the threats that we've been talking about?
Yeah, so if you look at, you know, every one of these either socially engineered or done through kind of an automated fashion.
And when Ping looks at it, it’s really looking at, you know, They're trying to impersonate the identity, trying to take over an identity account.
And some of the things that and when we talk to customers, it's really about, You know, first managing the journey that that user takes, Because if it's, you know, really You know, somebody that you don't know, But you want to start to gain information about them.
A lot of technology is there, you know, that is in the online risk and fraud space, And it's how do you gather information about um that user.
So in that unknown state, things you can know is the browser, The ROM, the IP address, you can know the device that they're, Um, accessing, and it's just really any information you can, You know, better know the user.
Uh, once you know that user, then there's a way to strengthen that because now you have a sense of who they are.
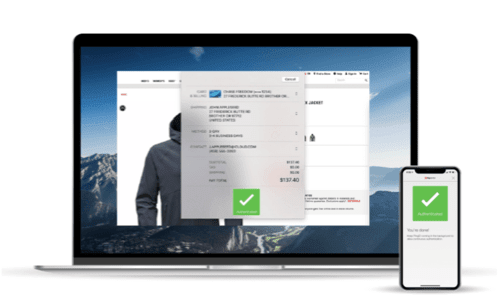
You can use identity verification technologies, You know, that helps confirm against either a live, you know, Selfie match or against some, um, credential that has been verified or validated by, You know, passports or government agencies or even corporations.
And once that identification happens, then it's, you know, Much easier to now start to look for different authentication mechanisms.
And, um, it's really that combination of, you know, How do I identify who they are by something?
They know or some, uh, something they are or even a location that they're in.
And so it's those ways of creating what we say on the journey of detect, To verify, to authenticate are great tools, great mechanisms to help mitigate some of the Risks that are out there from fraudsters and from the people who are making these attacks.
And what are the sort of uh the kind of baseline technologies that might have been Around for a while and some of the innovations in particular that Ping are working on that are Newer and, um, and juicier.
Yeah, no, that's, that's great.
So authentication has always been the kind of Core, and a lot of technologies existed too.
Um, determine based on how much information you know, or maybe the context that you're in Attributes I know about you, I can determine how I want to strengthen that authentication Event.
But, you know, it's interesting with a Synthetic identity or a hacker, they will take advantage of that authentication flow, and once They connect, um, they have enough info that they can access.
And so it's really where the majority of innovation is, You know, in kind of threefold.
It's that first authentication core and be able To adapt based on the information and based on the context that you have.
So you may, if you know the user well, and you're in a protected context, and the resource You're protecting is low value.
You can make that a fairly frictionless flow.
And then ways to introduce what we call more implicit friction is that you start to gather Information UM through intelligence.
So using artificial intelligence or machine Learning, you can quickly start to determine, Hey, I've seen this, Use it before.
I know the behaviors, um, I have enough trust.
In them that I can allow them in.
And then kind of the last resort is then I can create high friction.
But with a really fairly good user experience, how do you do identity verification in a live, You know, fashion, leveraging just your phone and a lot of technology then is really in that, You know, getting to know the user well, and then be able to use some of these verification Tools and a natural flow.
And just one more question before we move to the wider group, But following up on that, you mentioned sort of artificial artificial intelligence.
To what extent do you think, can you tell from the way I use my phone currently?
The way I tap it and type, um, can you, can you verify my identity?
Is that possible?
And if, if not, will it be possible, Where are we on the sort of trajectory of being able to sort of map an individual profile?
Yeah, no, it's a great question.
I, um, I used a statistic from a vendor I talked to, and that was artificial Intelligence space, and he said, you know, you really only need 16 characteristics of someone to essentially map with a very high assurance, 59 is what he was giving me from a level of Assurance.
And he said it's really more about how much I can know about, you know, the context they're in, and that the device that they're using, And then I need to know a pattern around the resources they're accessing, And then I need to know more information about who they are.
And a lot of that information is interesting if leveraging a phone.
You can even look at how someone holds a phone or how quickly they can swipe a different Button or how fast can they type, and those all End up being intelligence that starts to derive Who you are.
So as I talk with customers, many say, Yeah, I still, I believe you, you know, I think you probably have enough information that you Know who I am.
But I'm still not quite there to trust it.
And it's that combination of things is what we see most, um, customers doing is I know who you Are.
I still, based on the resource I'm protecting, I want something that's, uh, you know, that, that high-friction moment where you're using Identity verification or a lower friction, but where you're actually doing explicit Authentication.
Um, so I think we're close.
I don't think all customers are quite there yet, but, um, I think that journey is getting much, much better because of, You know, how we sort of started the call, you know, with the pandemic, A lot of remote workforces and a lot of things going online.
I think that's where a lot of the technologies evolved.