OAuth is Shooting for PAR
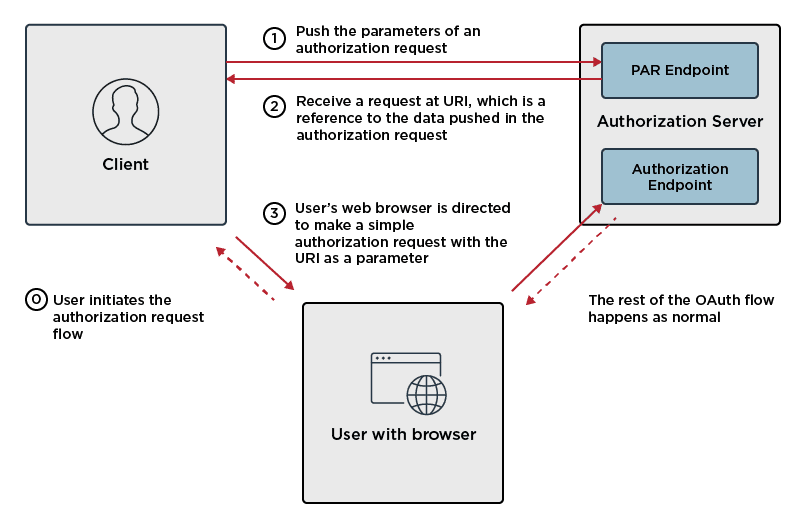
There’s a relatively new draft specification making its way through the Internet Engineering Task Force (IETF) process. OAuth 2.0 Pushed Authorization Requests, colloquially referred to as PAR, was adopted by the OAuth Working Group shortly after the fall IETF meeting last year in Singapore.

The 106th meeting of the IETF was held in Singapore in November 2019.
The PAR draft recently completed the working group last call process, which is an important step on the journey to becoming a Request for Comments (RFC). While nothing is truly fast in the IETF, PAR is believed to progress relatively quickly and with the expectation that it will remain stable enough with respect to the protocol definition to allow for interoperable implementations prior to becoming an RFC.
Now I realize that you might be thinking, “Wait a minute. With all the par talk, I was hoping this was going to be about golf, not Internet standards.” I get it and can commiserate. You can imagine my own dismay when I learned that my job at Ping wouldn’t involve early access to all of the latest golf equipment. But we’re in this together now, and it won’t take anywhere near as long as a round of 18, so let’s keep chipping away at it.