Introduction
Identity and access management (IAM) and identity governance and administration (IGA) work hand-in-hand to control access to resources, prevent data breaches, and comply with regulations. IGA isn't something offered by Ping, but we work with partners that provide this crucial solution. Read on to learn more about IGA, its importance in any security strategy, and how IGA and IAM work together.
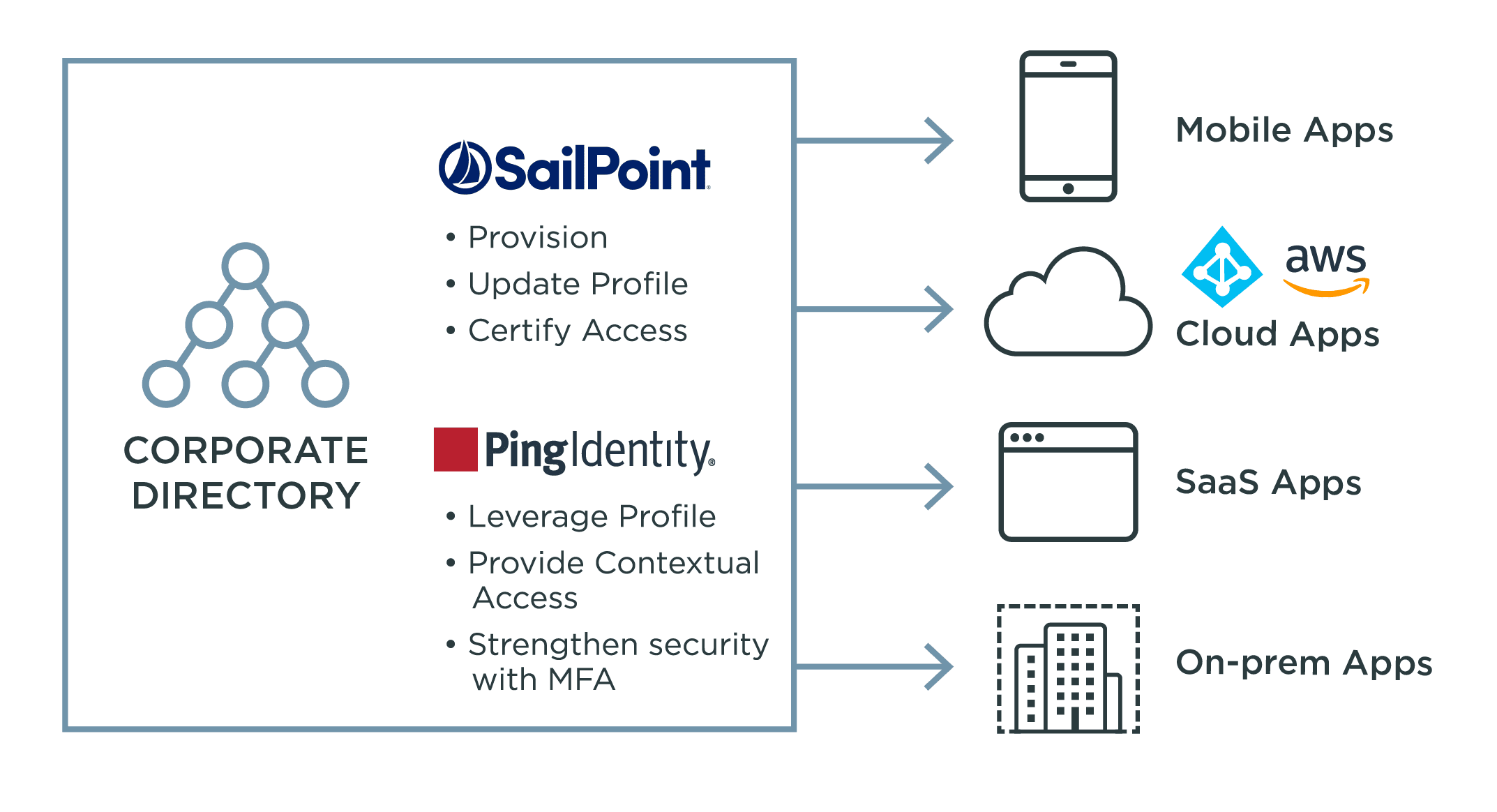
That's why Salepoint and Ping Identity, leaders in enterprise identity management, Management has partnered to put Identity at the center of your IT and security Infrastructure, enabling organizations to move from Zero Trust to trusted.
Our solutions provide an Identity foundation so that secure, Seamless access can be closely governed, ensuring the right level of access to the right Resources, wherever they may be.
Together they empower your teams with increased visibility; centrally view all access to ensure Each login is securely authenticated and entitlements are appropriate based on their Current role, greater governance and control, automate processes like provisioning, Password management, access requests, and certification, all of which are documented to Meet regulatory and audit requirements, and seamless and secure access.
Empower users with self-service access to applications with advanced authentication Workflows, using single sign-on and multi-factor authentication anywhere, Reducing IT workload.
With AI and machine learning, improved security through advanced detection of threats and Breaches.
Here's how it works.
First, Ping Identity provides an authentication authority that enables any user to access any App on any device.
It authenticates users and determines their appropriate access.
Next, using AI and machine learning, Salepoint builds the user profile with policy-based Self-service access to all applications and data.
SalePoint then assigns the appropriate attributes and permissions.
For each user profile based on their role or group.
Ping Identity consumes the profile's attributes and permissions for a seamless and secure user Experience.
Together, this integration helps you fortify Your security posture and keep users productive.
See why leading organizations across the globe trust SalePoint and Ping Identity to move from Zero Trust to Trusted.
Visit us online today to get started.