Financial institutions face a wide range of technical challenges of securing access to Open Banking APIs under UK Open Banking. In the coming weeks, I will be covering how Ping Identity can address these challenges. In this first blog, I focus on how Ping Identity enables Account Servicing Payment Service Providers (ASPSPs) to comply with the Open Banking UK Dynamic Client Registration specification. Specifically, you’ll learn:
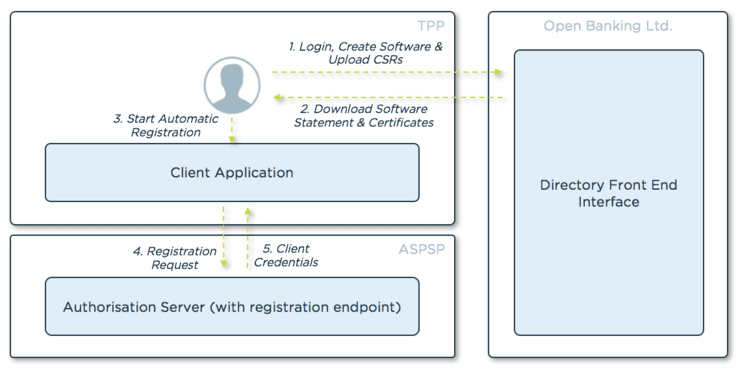
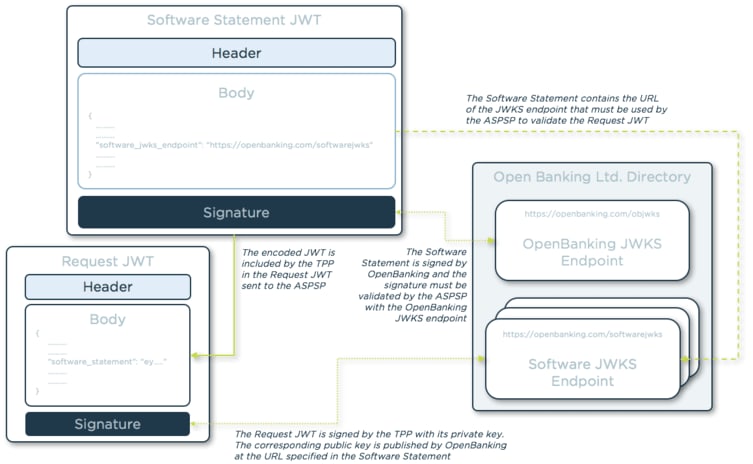
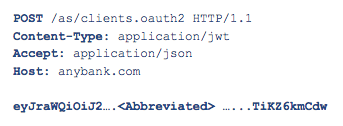
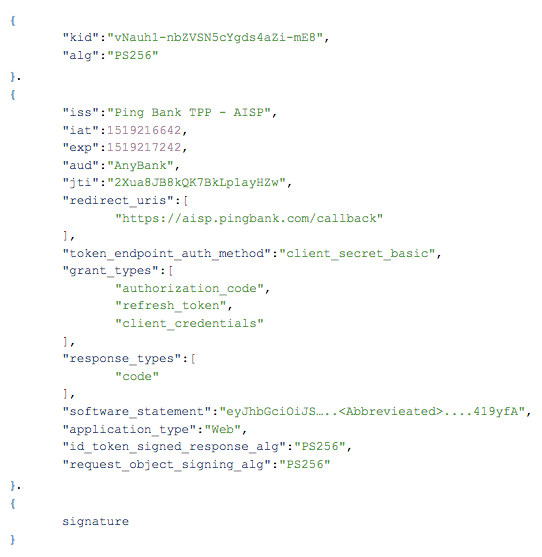
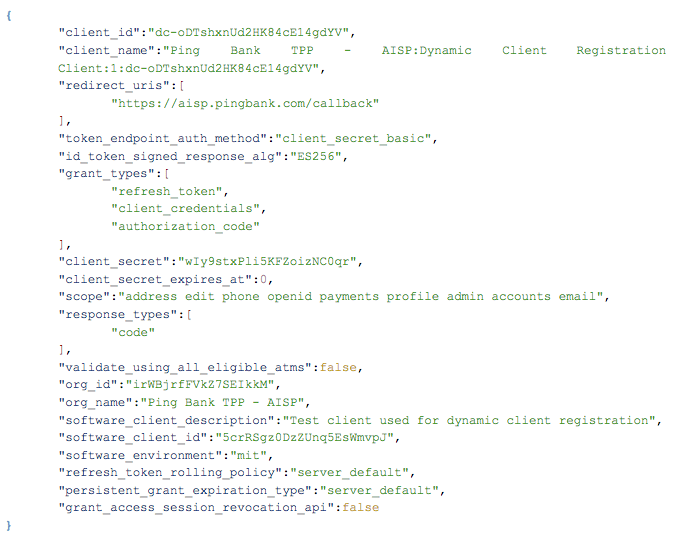
- How the Open Banking Dynamic Client Registration process works.
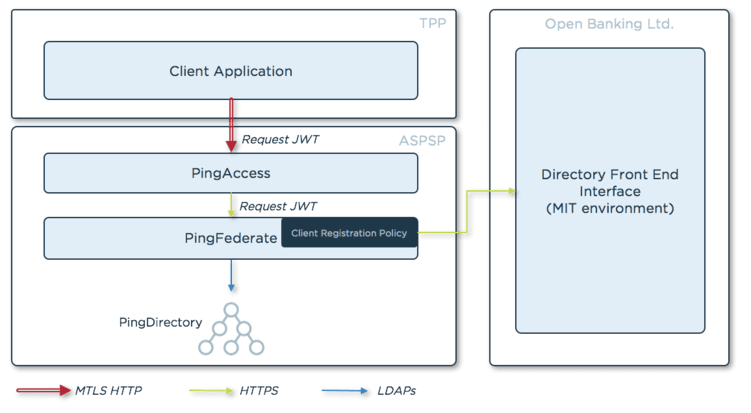
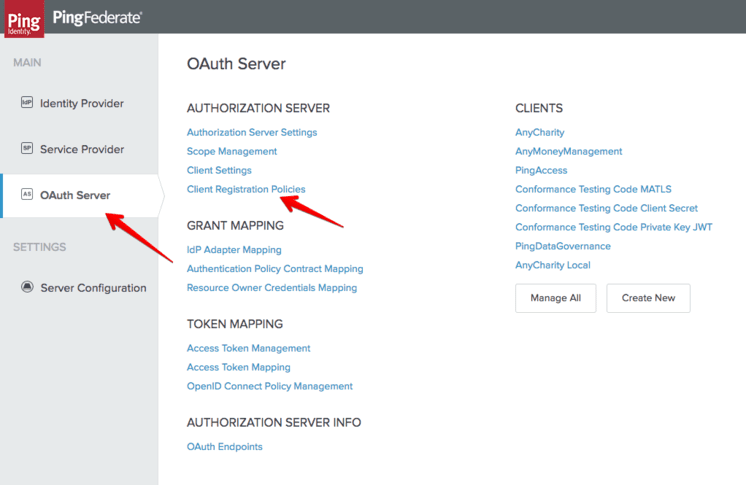
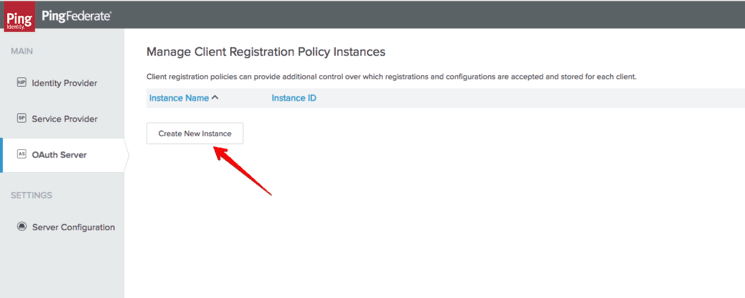
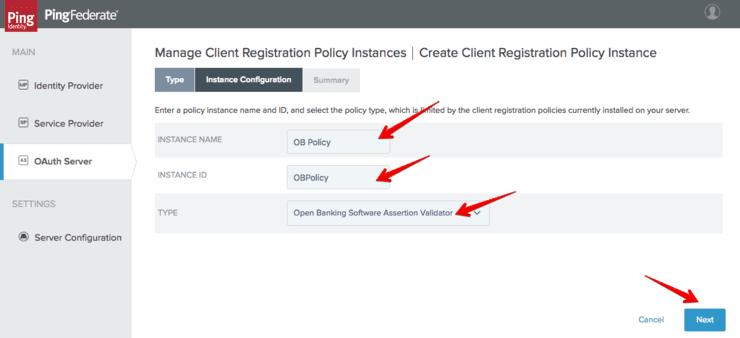
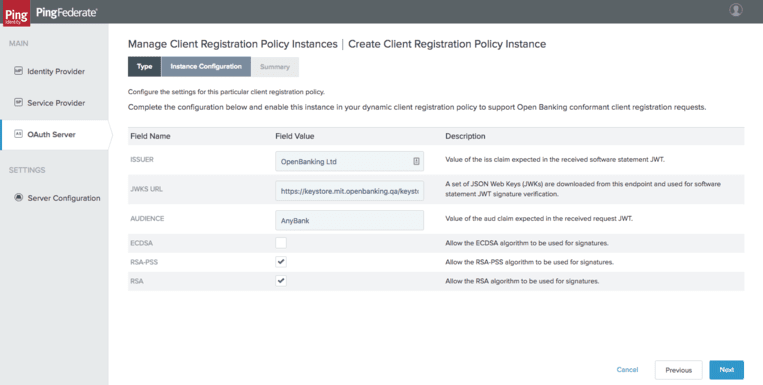
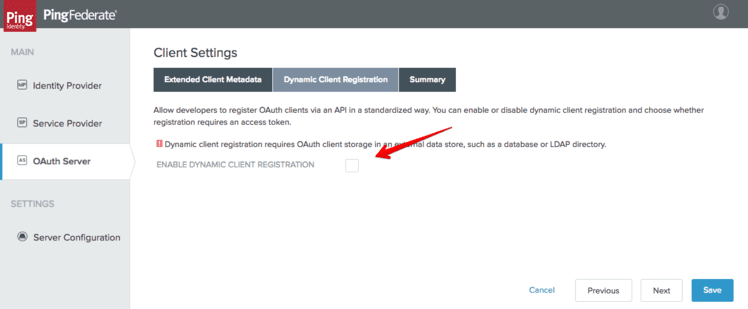
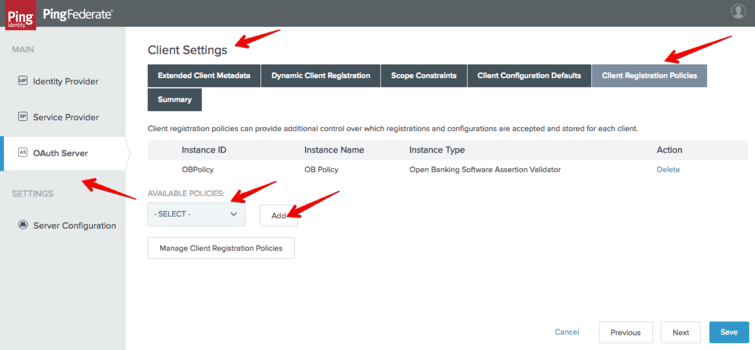
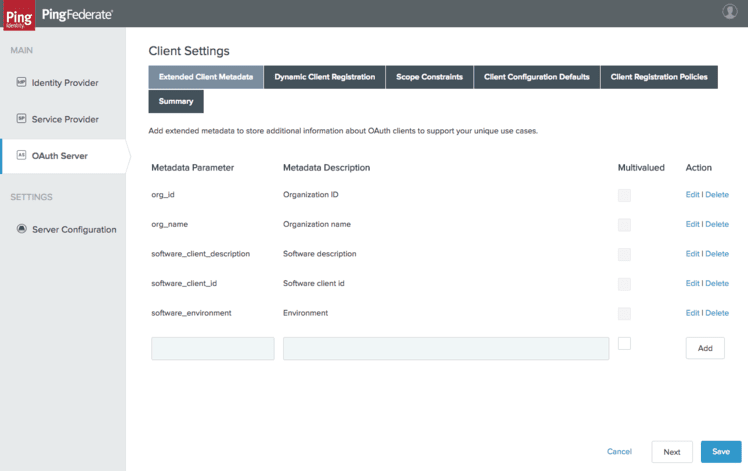
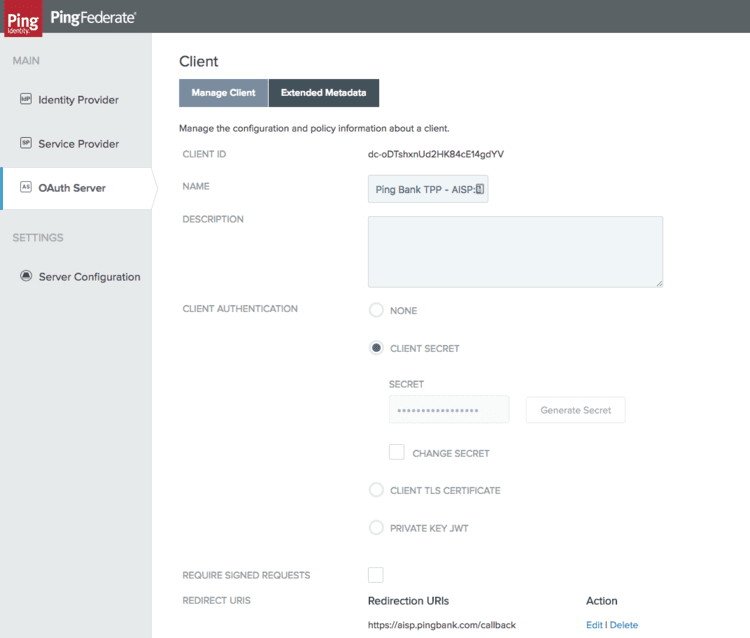
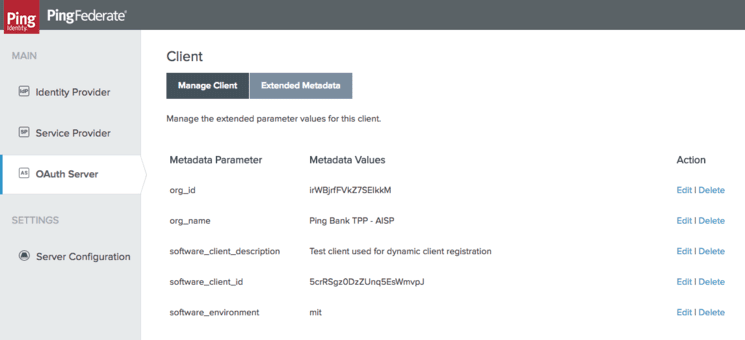
- The PingFederate configurations needed to enable Dynamic Client Registration.
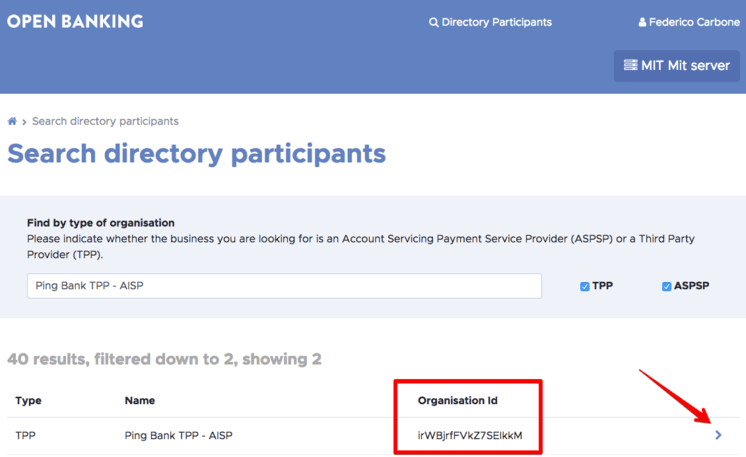
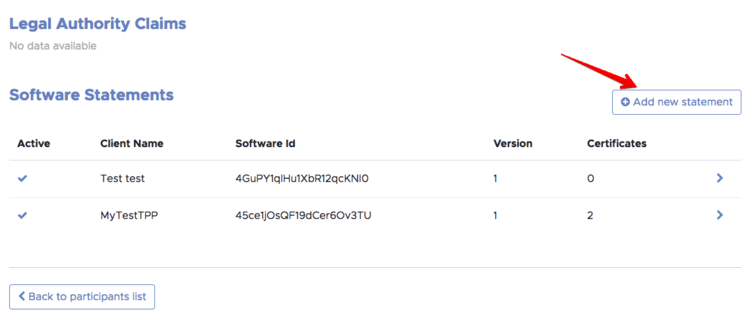
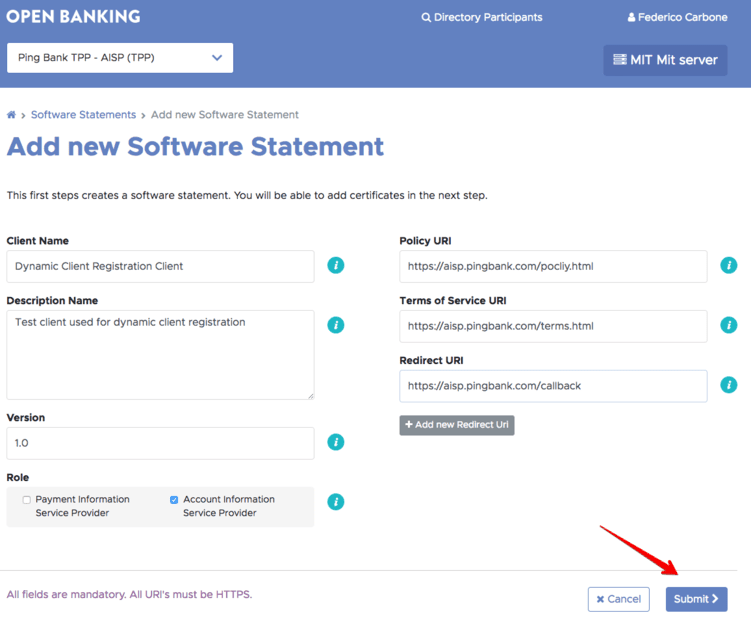
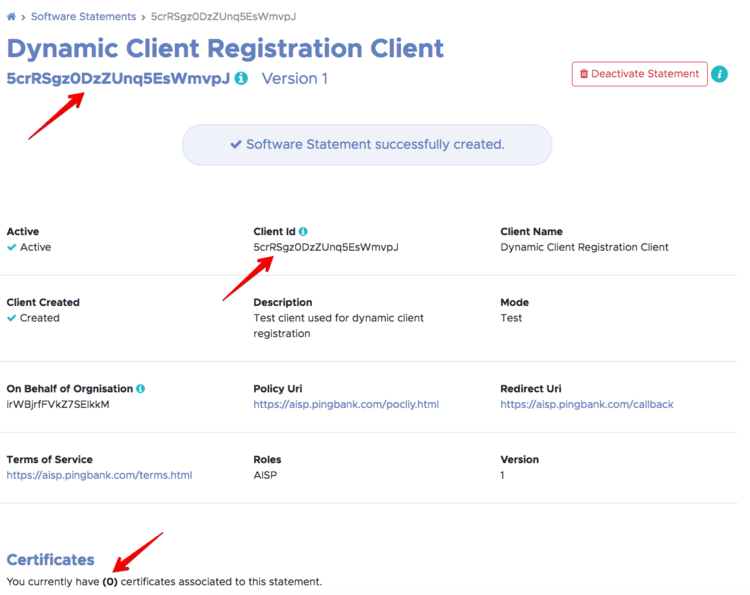
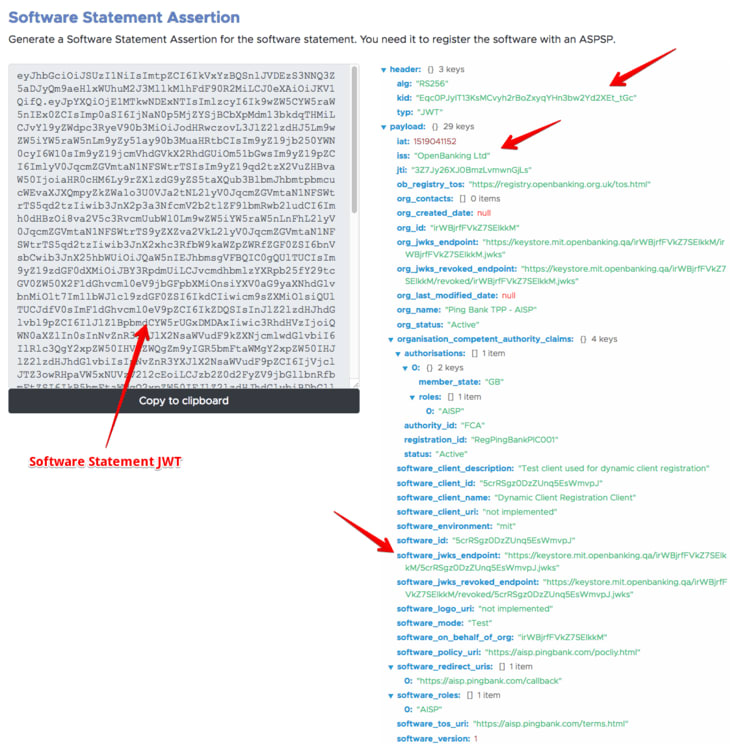
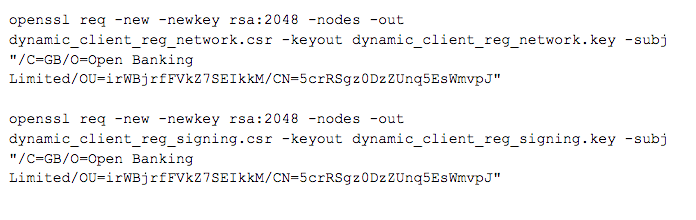
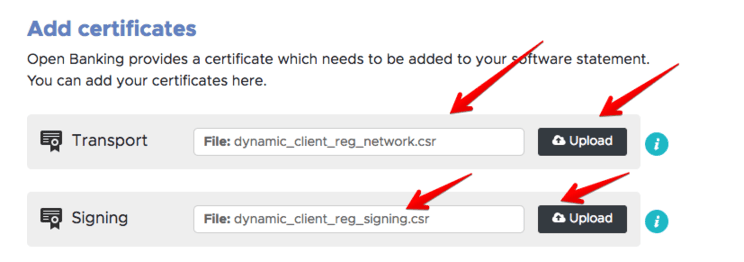
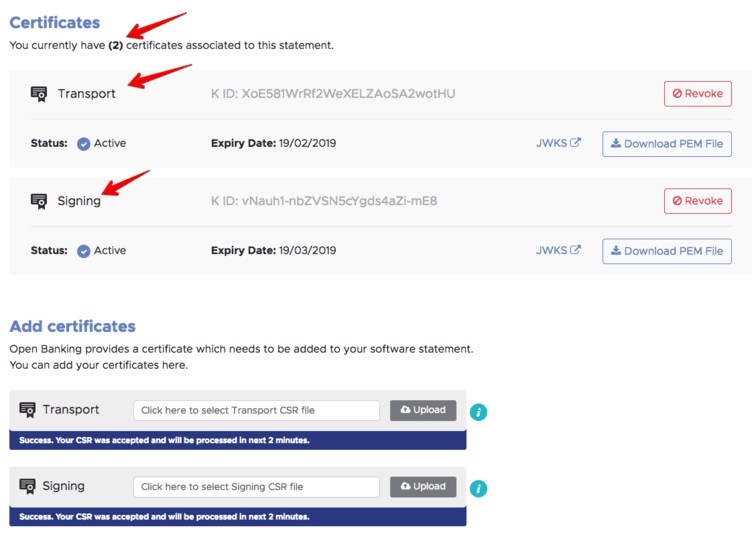
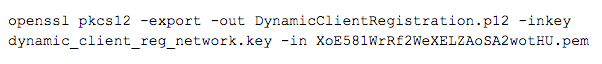
- How third-party providers (TPPs) can obtain software statements from Open Banking and issue registration requests to PingFederate for client registration.