PingOne Authorize
Tour the Product
On top of all that, you're struggling to meet regulatory requirements around consent and data Access.
Sound familiar?
The bottom line is you want the right users to be able to access the right apps and data at The right time, but how do you make this process seamless while still maintaining Security?
That's where PingOne Authorized comes in.
PingOne Authorize acts as a cloud-based hub and provides dynamic authorization.
It's customizing your user experiences using real-time data to automatically decide what Each user can see and do within all APPs and digital resources.
Business users can easily create a policy decision tree using a simple drag and drop Interface, removing the need for development.
The decisioning API enforces authorization policies and mitigates risk.
It's time to move beyond role-based access controls to dynamic authorization.
Protect your users, protect your data, and personalize user experiences all in one easy to Use Centralized-UI hub.
To learn more about how PingOne Authorized can Help your business, contact Ping today.
Meet PingOne Authorize
PingOne Authorize leverages real-time data to decide what users can see and do within applications and APIs. With an exploding number of data connections, regulations, and access requirements to manage, dynamic authorization is the key to enabling scale and consistency.
How It Works
PingOne Authorize acts as a decisioning hub by ingesting risk signals and user attributes to enforce access policies. This solution provides a Trust Framework that allows administrators to easily connect and define data sources that will be used by a policy. The policies section features a drag-and-drop interface for managing the conditions and rules that evaluate data to make policy decisions. The decision API enforces the policies by accessing external data sets, ingested signals, and directory attributes to make real-time authorization decisions about whether to grant or deny access or to kill a suspicious user session. A record of all policy configuration changes is captured in the version control history and is easily shared for privacy compliance and auditing purposes.
PingOne Authorize externalizes authorization from code to a centralized, collaborative interface where admins can build and test policies by layering attributes in a visual policy decision tree.
With PingOne Authorize you can:
Move beyond role-based architecture controls for decisioning and save time by taking the burden off resource owners to make authorization rule changes
Gain increased control/visibility of how users are interacting with your systems and address authorization sprawl
Comply with increasingly strict data regulations and enforce consent and data privacy
User Journey Alignment
PingOne Authorize spans from the “Authorized” to the “Disabled” stages of the user journey.
Zero Trust with Fine-Grained Access Control
To achieve just the right balance of security, privacy, and user experience, fine-grained access control is essential. Attribute-level, dynamic, and externalized authorization facilitates a Zero Trust approach, adherence to regulations, and enforcement of consent.
Business-Driven Policies
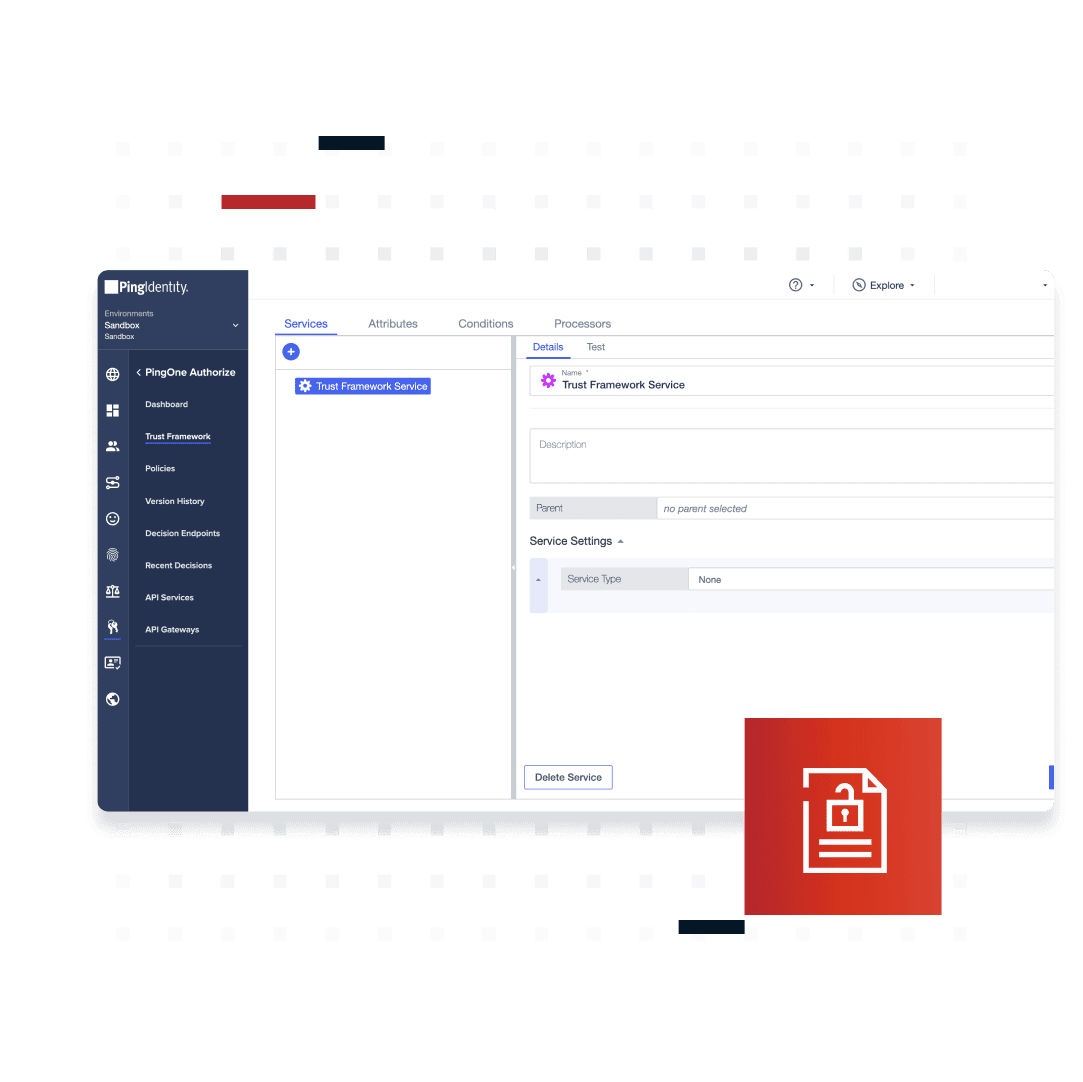
PingOne Authorize provides an elegant “Trust Framework” that allows administrators to dynamically connect and define data sources that will be used by a policy. The policies section provides business users with an easy-to-use solution for creating and managing the conditions and rules that evaluate data and make policy decisions.
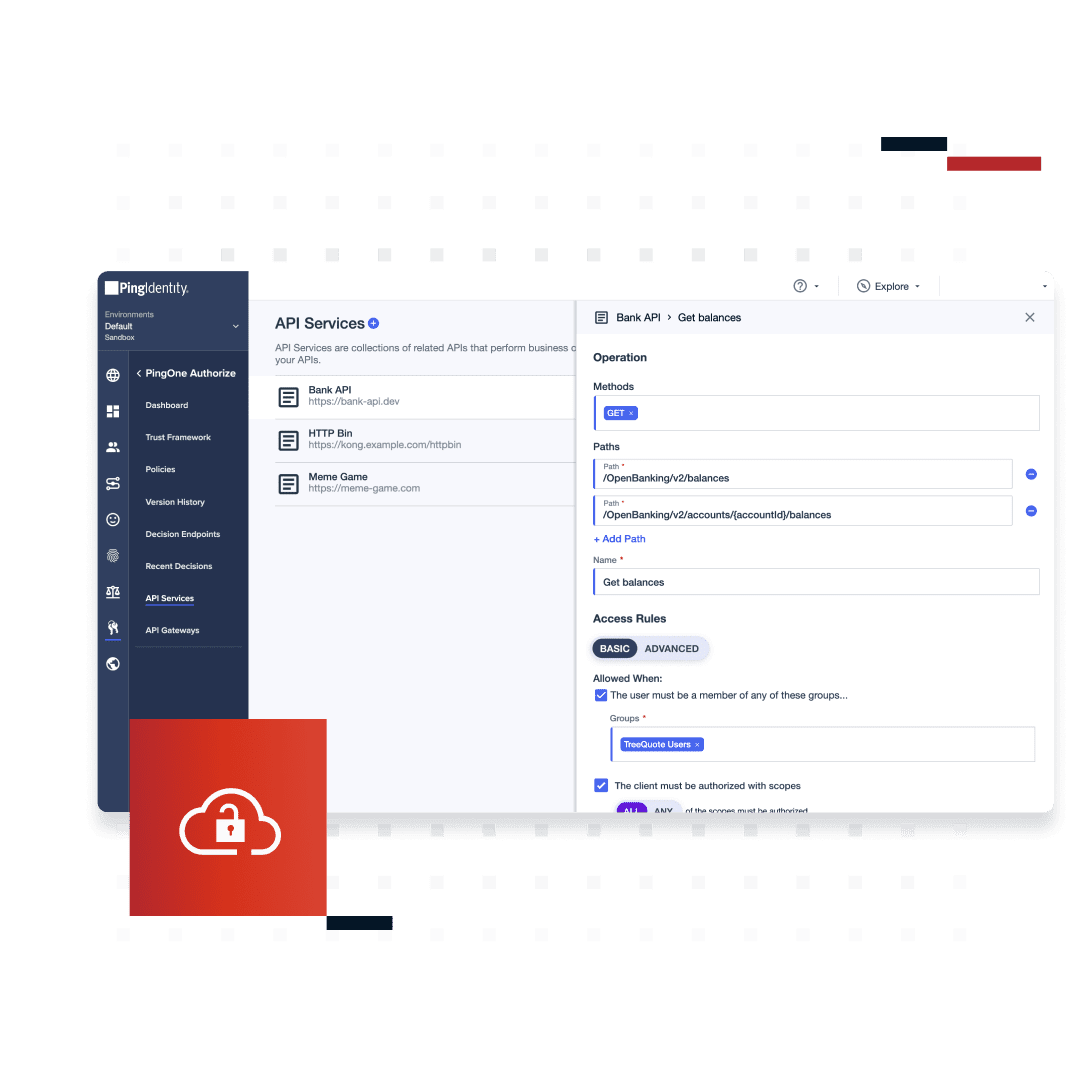
API Access Controls
Improve security, increase agility, and decrease risk with API access management. Centrally manage common API access controls, while distributing enforcement to API gateways using Ping’s integration kits. This simplifies management and enforcement because it removes the need to configure OAuth and OIDC protocols.
Meet Regulatory Requirements
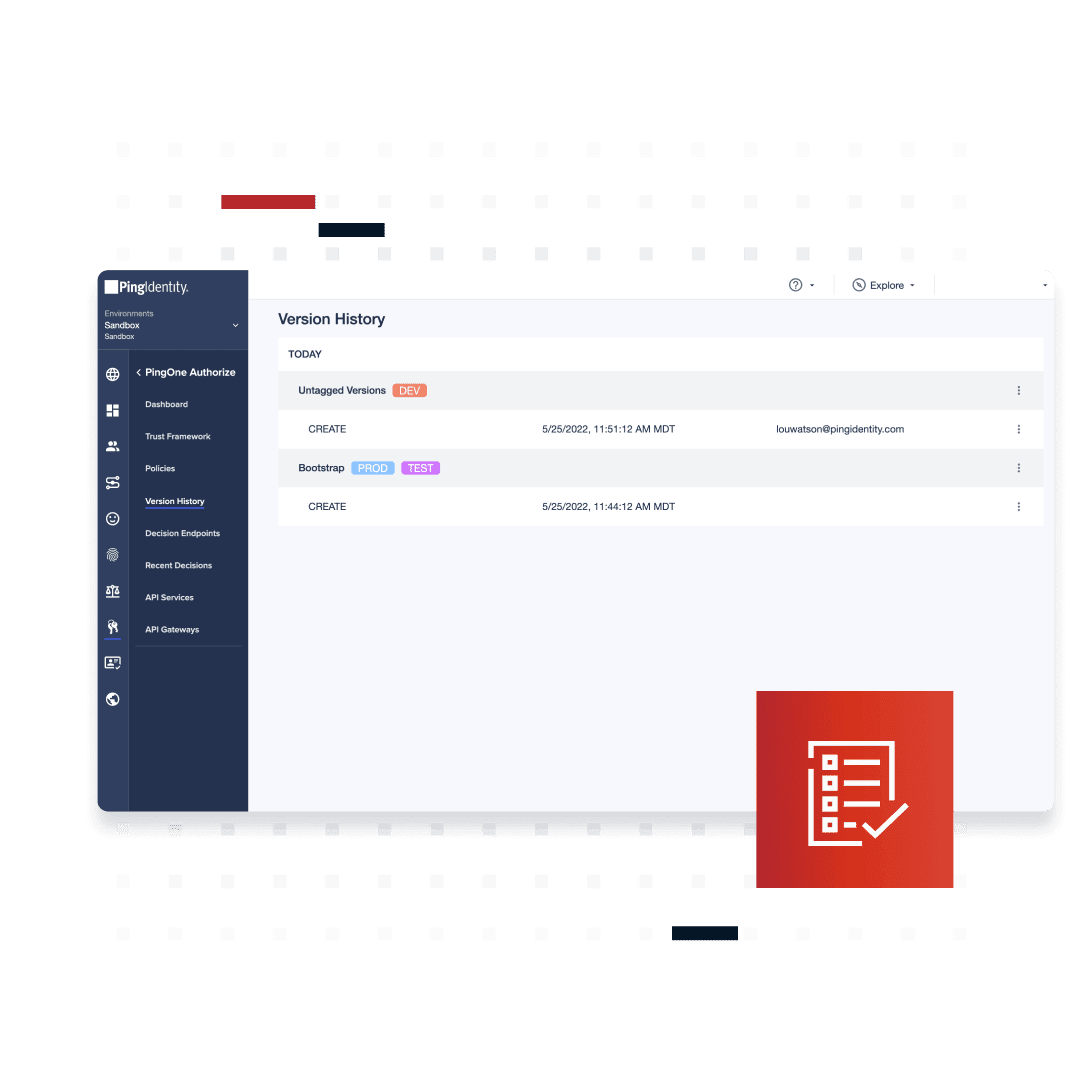
Establish and enforce governance policies around data privacy, consent, and more to satisfy regulatory requirements. Easily capture, share, and collaborate on policy configuration and administration activity from a single, centralized console. See how policy decisions were reached with comprehensive audit logs and version history.
Benefits & Features
Construct fine-grained access rules based on any context-specific and real-time data, like user location, time of access, group membership, and transaction value
Configure API access controls without having to change OAuth or OIDC protocols
Provide and enforce consent, data privacy, and other regulations in a single console, includes version history control reporting
Ingest fraud and risk signals to build adaptive authentication and authorization
Consolidate access policy administration, decision, enforcement, information, and retrieval points
Allow internal and external users to easily access the web apps and APIs they need
Kill a user session or prompt additional authentication based on ingested risk signals
Ingest custom or third-party risk signals
Easily configure access policies with out-of-the-box examples and templates
Connect to external systems to make authorization decisions based on original data sources
Business Value
Increase security
Maximize uptime
Minimize friction
in the user
experience
Flexible Deployment Options
PingOne Authorize can be deployed as:
PingOne Services - Multi-tenant SaaS
Platform Alignment
PingOne Authorize is an integral part of the PingOne Cloud Platform and is essential to the “Authorize” phase of the identity and access management user journey.
Platform Alignment
PingOne Authorize is an integral part of the PingOne Cloud Platform and is essential to the “Authorize” phase of the identity and access management user journey.
Start Today
Contact Sales
See how Ping can help you deliver secure employee, partner, and customer experiences in a rapidly evolving digital world.