Introduction
La pandémie a pris de court de nombreuses entreprises qui n’étaient pas préparées à passer rapidement des interactions en face à face à des opérations principalement numériques. Qu’il s’agisse des banques, des commerçants, des magasins d’alimentation ou des prestataires de santé, les organisations n’ayant pas mis en place de systèmes pour sécuriser l’accès des utilisateurs 24h/24 et 7j/7 depuis des appareils exposent leurs entreprises, leurs employés, leurs partenaires et leurs clients à des risques. D’après l’enquête 2021 de Ponemon, The Real Cost of Online Fraud, 61 % des personnes interrogées ont déclaré que leurs organisations n’avaient pas les bonnes technologies pour réduire les fraudes financières en ligne.
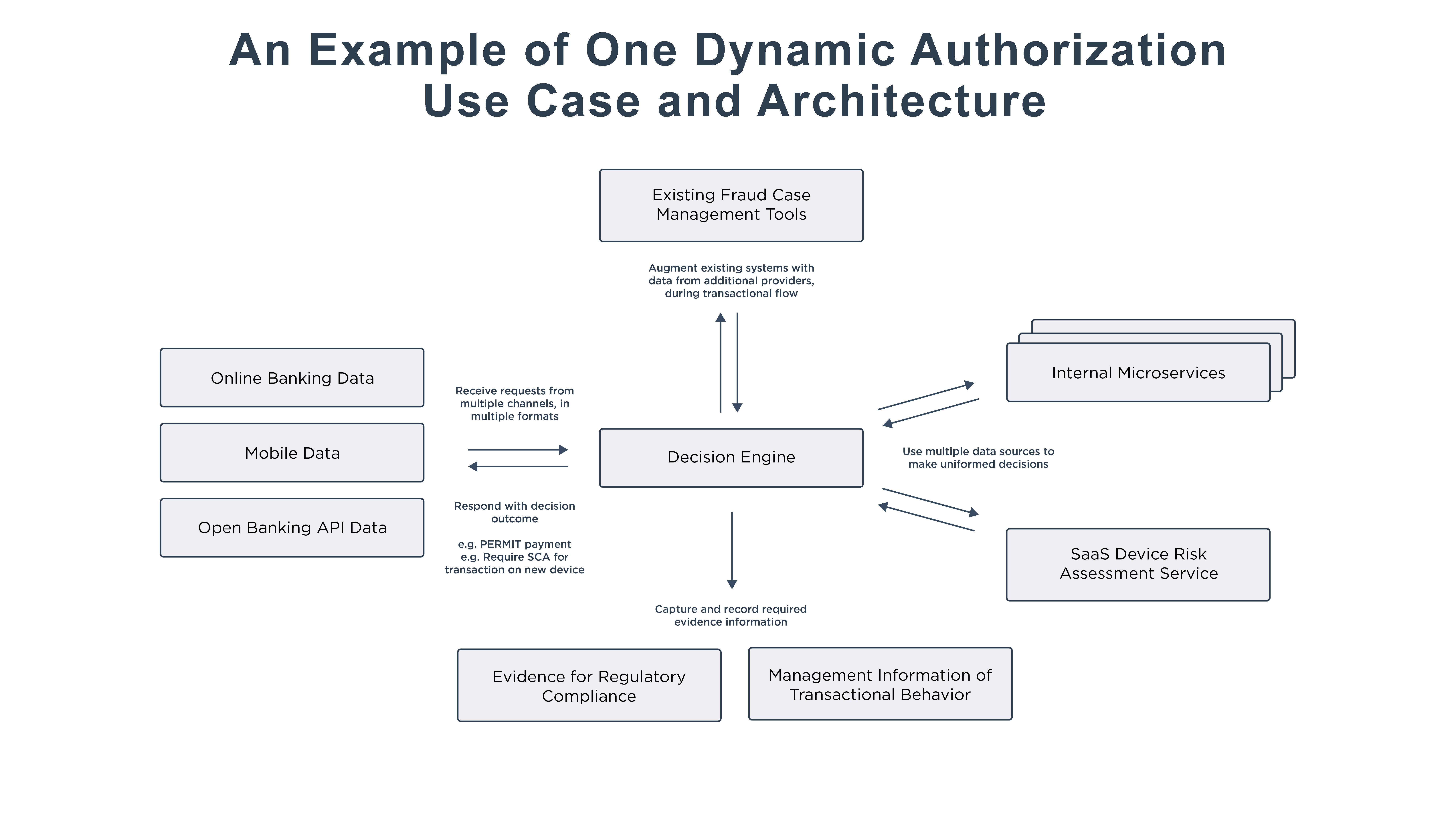
Lors des premières étapes de leur transformation numérique, les entreprises ont eu du mal à s’adapter aux acteurs des nouveaux marchés proposant de meilleures expériences client, et elles ont commencé à perdre des parts de marché. Elles se sont aussi exposés elles-mêmes à des attaques par des acteurs malveillants. Les organisations utilisant le contrôle des accès basé sur les rôles (RBAC), une approche large qui était efficace quant les utilisateurs et les systèmes étaient sur site, ont constaté qu’elles avaient besoin d’une approche plus flexible et ont migré vers une solution de sécurité définie par l’identité, un contrôle des accès basé sur les attributs avec l’autorisation dynamique. Cette nouvelle approche associe le contrôle centralisé et le contexte au niveau de l’utilisateur pour prendre des décisions en temps réel.
Many leading global companies have unlocked huge value in identity and access management solutions.
But putting identity at the core of your security architecture, you can reduce the risk of stolen credentials, eliminating the number one threat of breach in the enterprise.
Centralized access control to remove security holes and improve compliance.
Protect your customers and employee identity data from end to end.
And enforce both corporate data access policy and user preferences for data privacy.
Most organizations today still rely on a perimeter based approach to security.
This is made up of both the physical walls of their office and a network firewall.
This made sense when all the users applications and identities were inside this perimeter and the bad guys were on the outside.
But today, users and their devices are mobile.
And many SaaS enterprise applications and services are in the cloud, making a perimeter based approach to security ineffective in securing the enterprise.
To make matters even worse, users authenticate with many passwords giving hackers a much larger surface area for attack.
Well there's a better way, the Ping Identity platform makes identity a security cornerstone with five key capabilities.
First, single sign-on gives all of your users, your employees, customers and partners single-click access to SaaS, cloud, and legacy apps.
SSO from Ping lets you authenticate your users once, no matter where they are with a single set of corporate credentials, eliminating all of those insecure passwords and giving your organization a single authentication authority.
But since most organizations still rely on passwords for their corporate credentials, they're still susceptible to breach.
Multi-factor authentication or MFA allows your enterprise to move beyond passwords with a great user experience.
As users sign on, policy is evaluated using contextual data to determine if step up authentication beyond a password is necessary.
If so, they're prompted for another factor.
This is highly configurable, including one time pass codes via SMS, email or voice or maybe a user is prompted for a fingerprint on their device.
With MFA, hackers are denied access even with a stolen password.
Okay, so now your users are securely authenticated, but not every user should have access to all applications.
The access security capability will give your organization a central policy driven access control layer for all enterprise apps, whether they're in the cloud or on premises.
As users make requests to applications or to API's through a mobile application for instance, contextual data and attributes such as the application page requested, time of the day, network, session status, group, etc.
are used to evaluate authorization policy at the application page or API level and determine whether access is granted or denied.
Another challenge that many organizations face is keeping their customer and employee identity data safe and secure.
Many times identity data is scattered across many unsecure data stores and directories.
The Ping directory consolidates and secures your sensitive identity data at all phases during capture, and transit, at rest, or during reporting and logging.
It does this without sacrificing performance or scale.
In addition, most organizations are required to govern who has access to what data.
For instance, when a partner requests customer data maybe to fill an order, you may need to protect social security numbers or credit card data.
The Ping data governance capability enforces both corporate policy and user privacy preferences for all requested data from partners, various corporate groups or other applications.
Ensuring your organization complies with all relevant industry, geographic, or corporate policies.
The Ping Identity platform makes identity the new perimeter, strengthening corporate security, and ensuring regulatory compliance without sacrificing user experience.
Thank you.