Key Takeaways
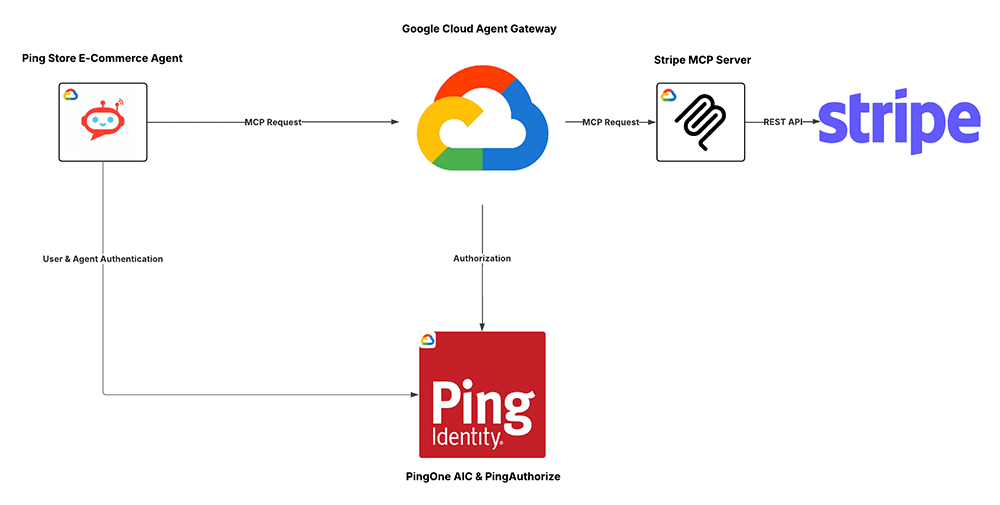
Google Cloud Agent Gateway gives organizations a managed control point to secure and govern agent and tool traffic on every network path.
- Ping Identity adds Runtime Identity and fine-grained authorization via PingOne Authorize so every agent and tool call is continuously checked and approved.
- Together, they deliver centralized, consistent control over agent and tool traffic without changing application code.
Enterprises want agents that do real work: complete transactions, call tools and APIs, work with other agents, and move tasks across systems without constant user clicks.
That means every request becomes an identity and authorization event: who is behind this action, which agent is acting, what system is being called, and should this happen for this user, in this context, right now?
Ping Identity’s integration with Google Cloud Agent Gateway brings Runtime Identity into that managed path. These questions are now answered at runtime, not just when things are first set up.
Ping Identity is integrating our Runtime Identity solutions with Google's Agent Gateway, delivering continuous authentication and authorization decisions on every agent and tool invocation. This gives customers a centralized way to enforce fine-grained policies—scoped MCP tools, context-based authorization, and runtime protections. Our interoperability with the Google Agent Gateway is critical to Ping’s Identity for AI strategy, combining Google's managed infrastructure with Ping's enterprise-grade identity capabilities enable agents to act with the right permissions, at the right time, in the right context, and the right scale with clear accountability to the users they represent.
Peter Barker
Chief Product Officer, Ping Identity