Continuing Collaboration in Service of Real-World Customer Challenges
With the rapid expansion of cloud technologies and an overwhelming amount of security and identity data to analyze, organizations are now focused on finding effective ways to harness resources securely. The biggest challenge is trying to secure their environments without adding complexity or unnecessary decision-making burdens.
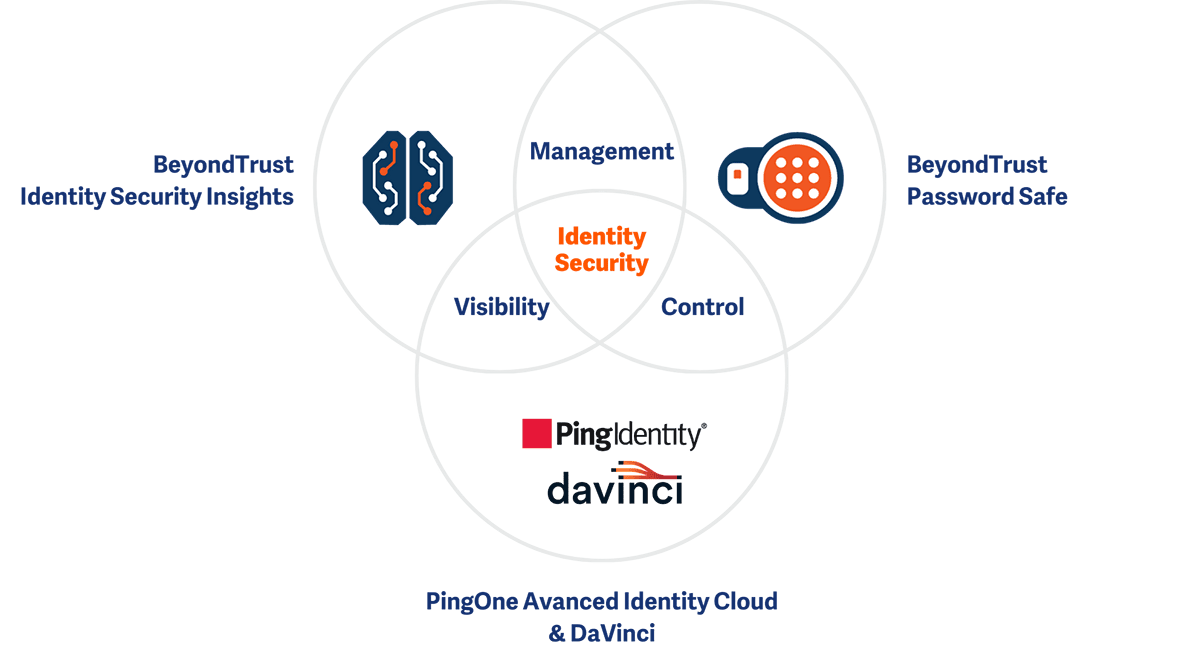
BeyondTrust and Ping Identity have been partnering to deliver seamless integrations that advance identity security and governance for over five years. Now we are excited to introduce several new BeyondTrust - Ping integrations that further expand on our current strategic partnership to provide our customers with powerful visibility, management, and control:
- BeyondTrust Identity Security Insights and Ping Identity Platform
- BeyondTrust Identity Security Insights and Ping DaVinci
- BeyondTrust Password Safe and Ping Advanced Identity Cloud
By enhancing our customers’ ability to continuously assess their identity security posture across endpoints, servers, cloud services, DevOps systems, and identity providers, we are better equipping them to manage and secure their expanding identity estates.
Read on to learn more about these exciting new integrations and how they can help advance your identity security strategy.