Just over a year ago, we faced an overnight shift in how we live and work. For some businesses and organizations, the quick pivot to support work from home was relatively painless. But for others, making this shift was anything but a slam dunk. Hamstrung by outdated and siloed identity and access management (IAM) systems, government agencies have been challenged to maintain productivity and serve their constituents during a period of maximum telework.
“Digital transformation has become a priority for a significant majority of government leaders as a result of COVID-19, but legacy IT systems are hurting their ability to respond efficiently to constituent needs in a remote world.”
Source: “Government efforts to accelerate modernization face tech hurdles,” TechRepublic, Feb. 9, 2021
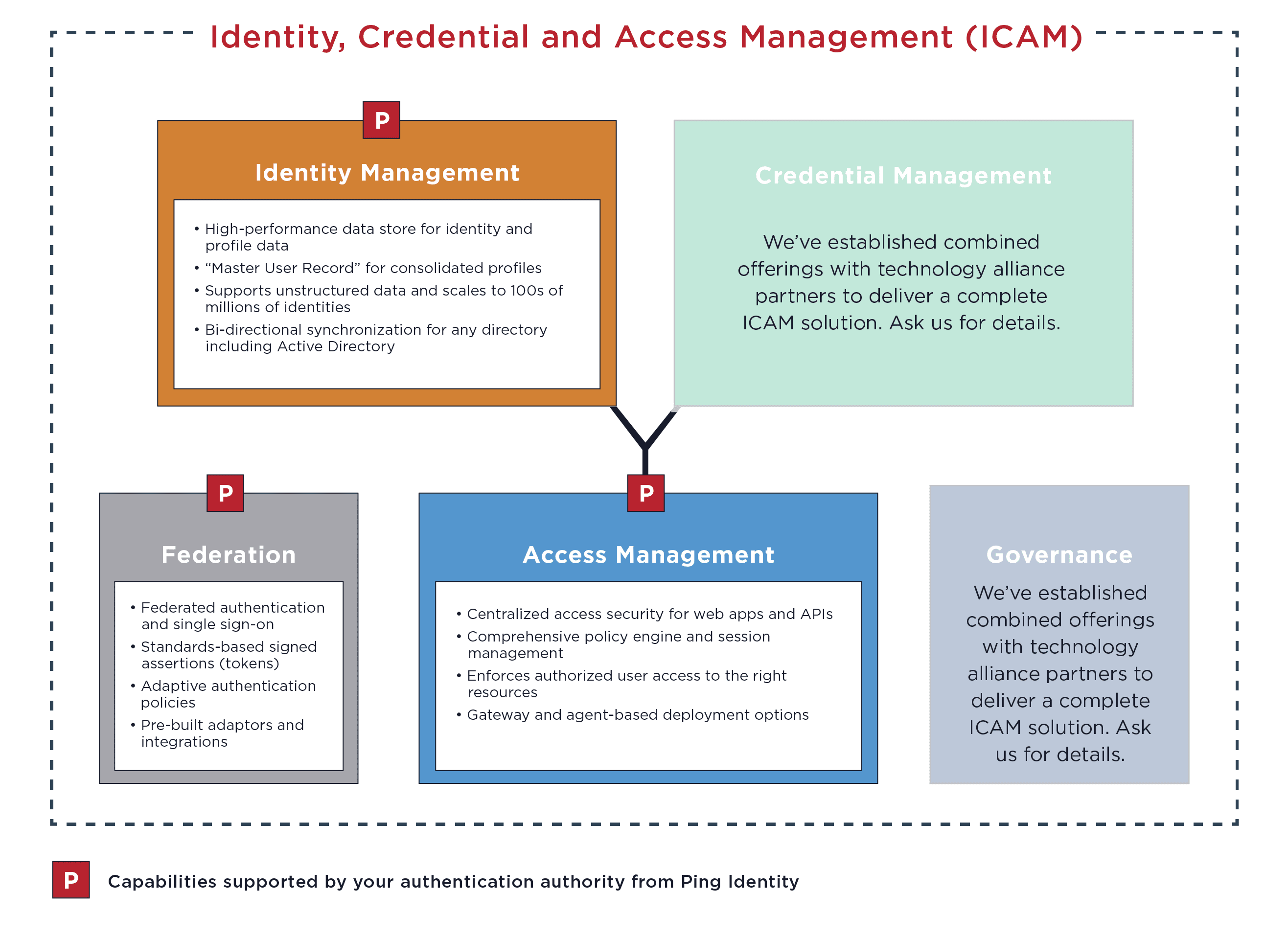
The rapid shift to telework and the acceleration of cloud initiatives magnified the gaps in legacy government identity technologies. These rigid IAM tools lack the centralized federation capabilities needed to support remote workforces and provide mission partners with access to critical resources. And they weren’t designed to support hybrid IT environments or identity and credential access management (ICAM) programs.
To give the right people access to the right resources—whether on-premises, SaaS or cloud—your agency needs a reliable single source of identity truth, aka an authentication authority. An authentication authority that specifically provides federated single sign-on (SSO), identity management and access management designed for government requirements will ensure you’re able to securely and reliably authenticate your workforce users and partners.