IDENTITY VERIFICATION
Prove They're Real.
Don't Slow Them Down.
Confirm humanity and build trust into every step of your digital journeys.
We work with the world’s top brands
THE CHALLENGE
Malicious AI Is Booming.
So Is Complexity.
Synthetic Identity & Imposter Fraud
Fraudsters are registering fake accounts, hijacking real ones, and blending in. You need to confirm who belongs in your ecosystem without disrupting trusted users.
Every Touchpoint Is a Target
Login isn’t the only attack surface. From account setup to recovery, every step of your user journey needs a trust check to prove that people are who they claim to be.
Fragmented Stacks = Broken UX
Multiple point solutions mean more brittle integrations and inconsistent user experiences. You need the agility to easily add verification everywhere.
THE SOLUTION
Identity Verification That Adapts to the Journey
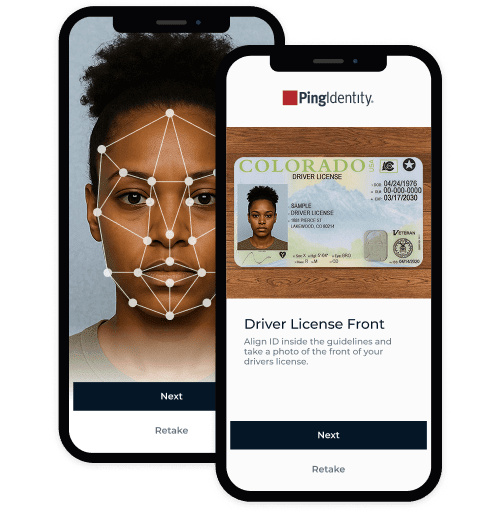
Verify your users with the right mix of checks at every touchpoint across the user journey. Ping combines documents, biometrics, devices, and data to verify users at every step, but only when needed. Minimal friction for trusted users. Dead end for the fraudsters.
Why You’ll Love Our Identity Verification
Protect your revenue and conversions. Hit your assurance and compliance targets.
Block More Fraud
Check a combination of documents, biometrics, devices, and data to stop fake or stolen identities before damage is done.
Cut Support Costs
Let your users self-verify for account creation and recovery. No manual reviews or support tickets required.
Smooth UX Across Channels
Start and complete verification from QR, email, or SMS, on any preferred device.
Verify Progressively
Escalate to higher-assurance verification methods only when risk demands it.
What Makes Our Verification Work
Security, scale, and interoperability that’s built to work with your tech stack.
What Makes Our Verification Work
Security, scale, and interoperability that’s built to work with your tech stack.
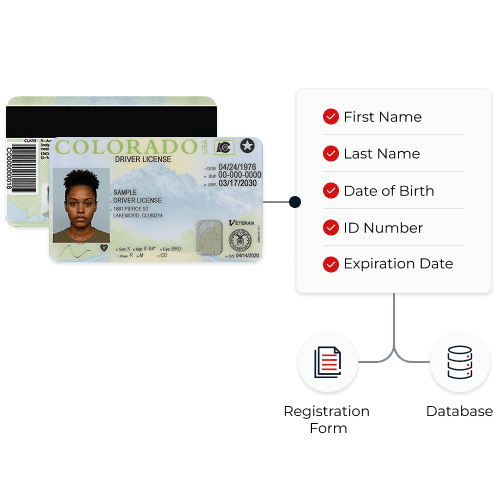
Validate government‑issued IDs, detect tampering, and extract data.
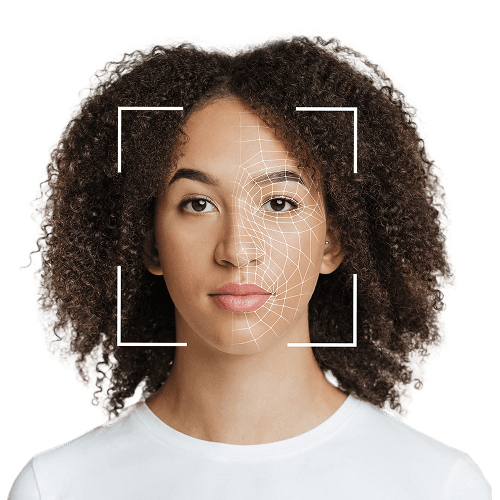
Capture a selfie and match it to any reference material. Detect presentation and injection attacks..
Cross-check identities with fast, reliable access to credible global data sources.
Match user-provided data with captured PII, and configure confidence thresholds for nicknames and multi-part names.
Use PingID or embed verification into your apps with SDKs, and orchestrate with your risk and authentication policies.
DIVE INTO THE DETAILS
From document and liveness checks to risk signals and reusable assurance, explore how Ping verifies real users at any point in the user journey.
Works with
What You Have
Across your SaaS, on‑prem, and hybrid environments, you can easily add identity verification to mobile and web apps, and integrate with your CIAM, SSO, MFA, and fraud controls. No rip‑and‑replace necessary.
Sample Integrations
Ping has been powerful in RMIS, Truckstop’s carrier onboarding and monitoring tool for brokers. Verification takes just a few minutes with a click of a button, and brokers can easily identify verified carriers. The result? Reduced fraud and peace of mind.
Thousands
of known theft attempts blocked
Millions
saved by preventing fraud
Why Ping?
Securing your most sensitive access points shouldn’t mean being locked into a single stack or stitching together a dozen tools. Our platform combines a powerful IdP foundation with a suite of services that are interoperable with any provider. No matter where you start, you can unlock value with flexibility, speed, and scale across every stage of your identity journey.
Here’s what sets us apart:
Universal identity services, built to work anywhere
Trusted globally, proven at enterprise scale
Easy to deploy, effortless to evolve
Let’s Make Trust Seamless
You don’t have to choose between fraud prevention and great UX. With Ping, you can build identity journeys that verify real users without driving them away.
Helpful Resources
Helpful Resources
Frequently Asked Questions
Identity verification is the use of documents, biometrics, devices, and data as checks to confirm a user’s real‑world identity.
It proves that the selfie is captured in real time and not a photo, deepfake, fabrication, or reprint.
No. Your users can start from a QR link, email, or SMS and finish on their preferred device. Our identity verification works across apps, browsers, mobile devices, tablets, and more.
Absolutely. You can issue reusable verified credentials or use selfie-capture for future authentication, account recoveries, or step-ups.
Our accuracy is strong, but it depends on the government ID being verified, the selfie matching the ID photo, or the confidence score of the data matching. Pass rates depend on several factors such as use case, attempted fraud rate (desirability of the outcome), user demographics, expected conditions where verification takes place, IDs being used (issuer and type), and more. You can tune thresholds based on risk and experience.