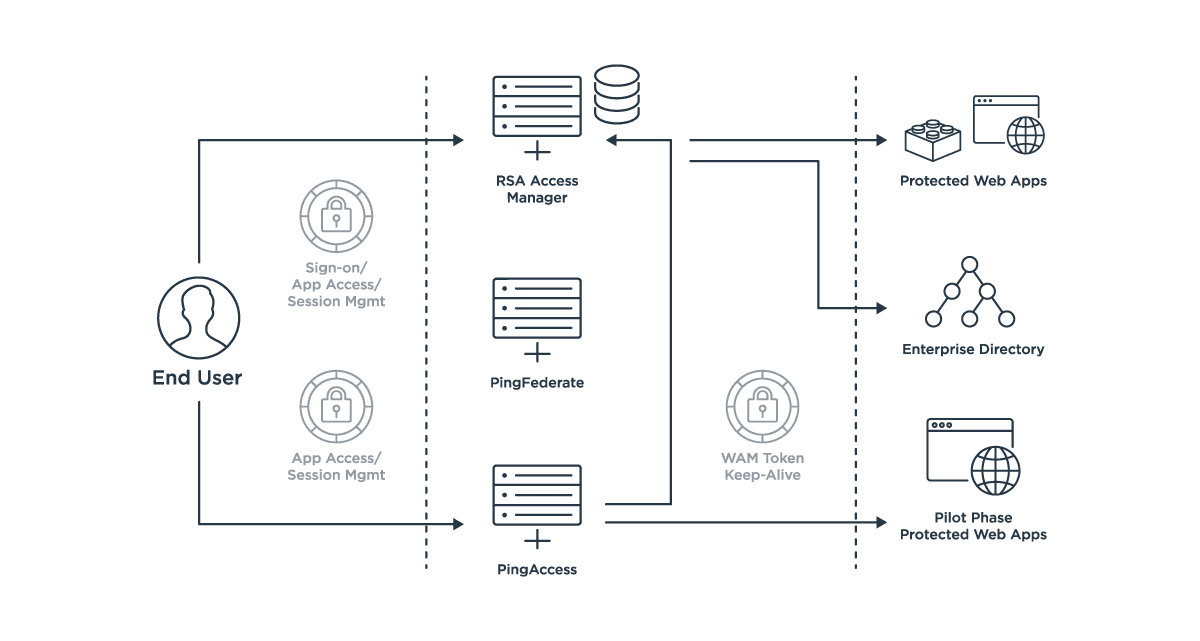
The first step in migrating an application from RSA Access Manager to PingAccess is to ensure that the required integrations are complete and that PingAccess can provide the necessary identity information to the application. The next step is to create the PingAccess rules that enforce access in the same way that RSA Access Manager enforces access.
The final step is to select the architecturally appropriate deployment option. Appendix C highlights a sample migration scenario from an agent- based architecture into either a gateway-based or proxy architecture.
Migrating Application Protection to the PingAccess Gateway
The first step is to determine if the application will continue to require the RSA Access Manager Cleartrust SSO cookie. If it’s still required (for example, if the RSA Access Manager agent will remain on the target web server), you configure token mediation so that PingAccess will acquire a target token on behalf of the user.
Next, you configure the application in PingAccess, defining where the protected web server resides, how it’ll be exposed via the gateway, what the required web session management controls are, and how end user identity details will be passed down to the application if needed (i.e., HTTPheaders using identity mappings).
Then you define your access policies using rules that are equivalent to (or a simplification of) those employed in RSA Access Manager.
Last, you configure network routing to start sending request traffic to PingAccess instead of the application.
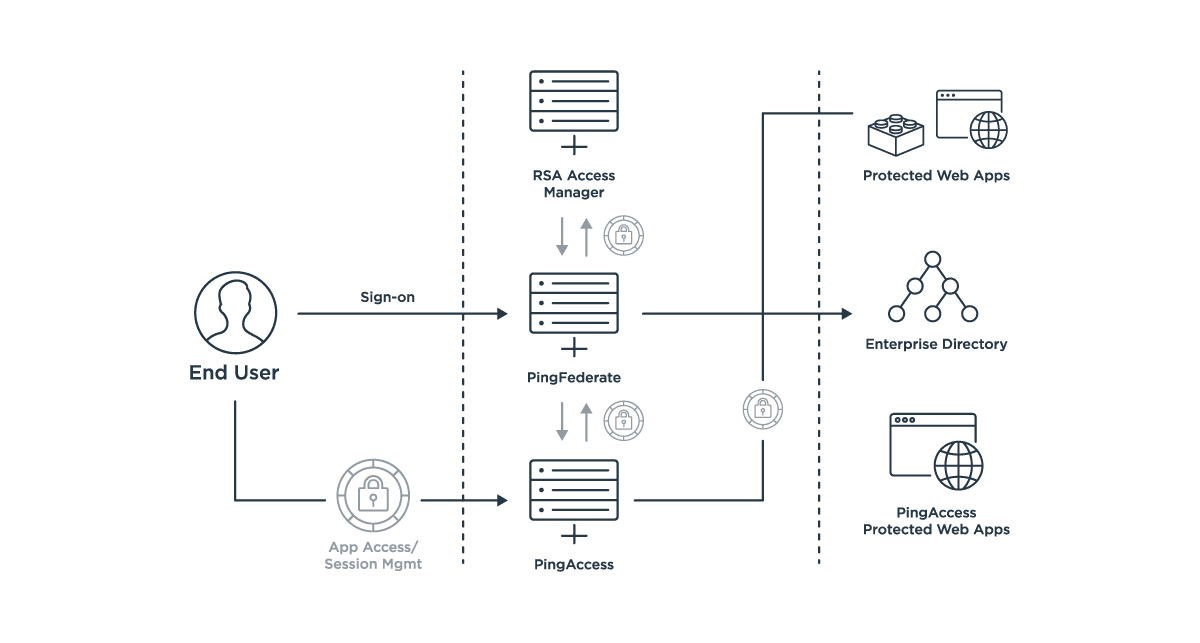
Migrating Application Protection to a PingAccess Agent
In scenarios where an agent model is still preferred, the PingAccess agent replaces the existing RSA Access Manager agent.
You should start by defining the application details in PingAccess, including virtual host and path information, web session management controls and how end user identity details will be passed down to the application, if required (i.e., HTTP headers using identity mappings). The agent bootstrap configuration must be defined in PingAccess, and produces a configuration file the agent plugin will read on the target system.
Next, you define your access policies using rules that are equivalent to (or a simplification of) those employed in RSA Access Manager.
Once configured, you uninstall the RSA Access Manager agent on the target web server and install the PingAccess agent.
Documentation for the agents can be found here.
Deploying New Applications
Any new applications protected by the solution should be deployed behind PingAccess. They immediately benefit from the lighter weight integration and combined web and API access management features that PingAccess provides. While a gateway-based implementation is recommended to simplify ongoing maintenance, agents can be installed where required in order to accommodate existing deployment models.