Introduction
Password isn’t exactly a four-letter word, but as a IT director, it should be just as cringe-worthy. You don’t need to read every study or article about the weaknesses of passwords—though there are plenty—to know that single-factor authentication is putting your enterprise at risk.
Two-factor authentication (2FA) provides an extra layer of protection. Is it a step in the right direction? Sure. But it leaves something to be desired in terms of both security and experience. Not only is 2FA notoriously unpopular with your users, it’s also not the sharpest security knife in the drawer, particularly if the second factor is delivered via text message.
This weakness came into the public light in 2016 when attacks on political figures were found to be a result of intercepted SMS messages. Around the same time, the National Institute for Standards and Technology (NIST) stopped recommending 2FA systems that use SMS, because of their many security weaknesses. While 2FA is correct in theory, “using SMS text messages isn’t technically two-factor at all,” according to security researcher and forensics expert Jonathan Zdziarski.1 He asserts there are better tools that can actually prove possession of the “what you have” factor.
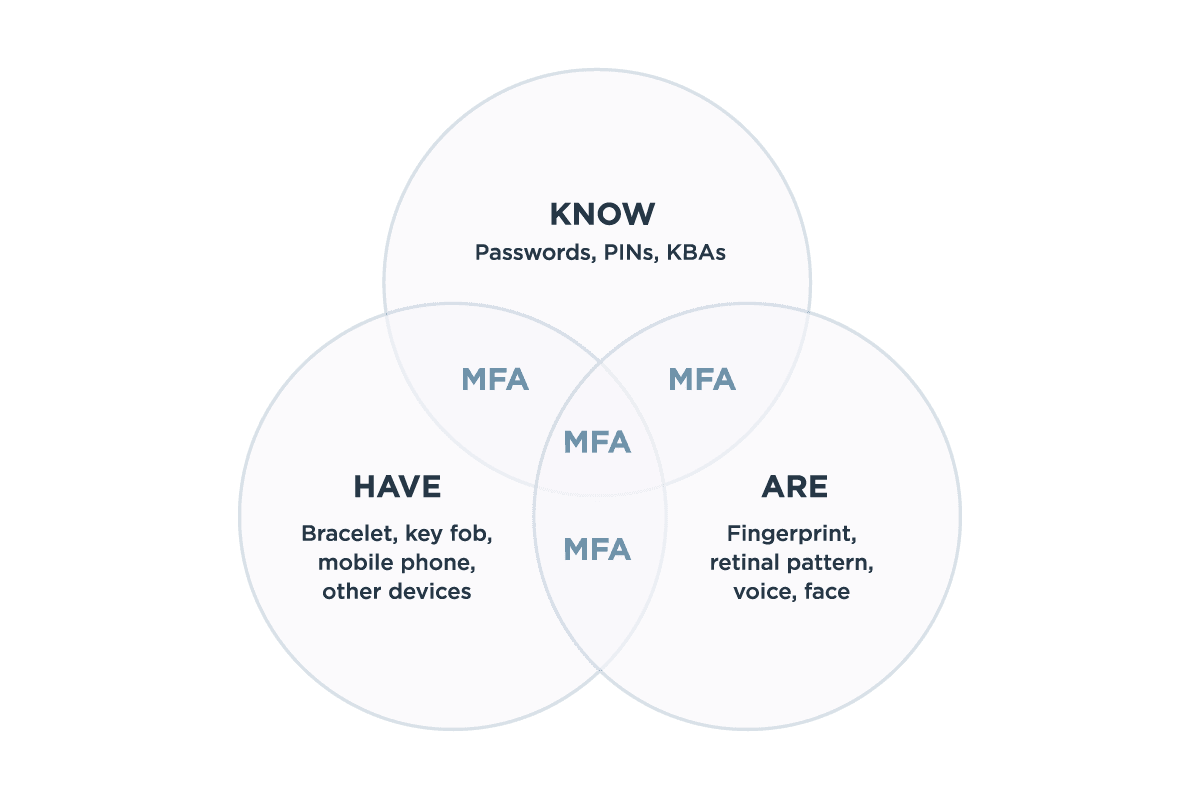
He’s right. And that better tool is multi-factor authentication, or MFA.
[For those that] only offer second factor protections that depend on SMS, it’s time to wake up, smell the targeted attacks, and give users better options.2
Andy Greenberg, Wired